Category: FireEye
Limited Shifts in the Cyber Threat Landscape Driven by COVID-19
Though COVID-19 has had enormous effects on our society and economy, its effects on the cyber threat landscape remain limited. For the most part, the same actors we have always […]Thinking Outside the Bochs: Code Grafting to Unpack Malware in Emulation
This blog post continues the FLARE script series with a discussion of patching IDA Pro database files (IDBs) to interactively emulate code. While the fastest way to analyze or unpack […]With COVID-19 Themed Campaigns on the Rise, Here’s How to Manage Email Phishing Risks
There are viruses, and then there are viruses. COVID-19 has rapidly taken over the headlines, with countries, organizations and individuals scrambling to contain the virus and maintain some level of […]Latest Helix Release Features Entity-Based Alert Correlation and
Aggregated Risk Scoring
The latest FireEye Helix release (2020.1) marks a milestone for our security platform. It features the debut of OS change reports from appliances, deeper FireEye Endpoint Security integration, advanced FireEye […]
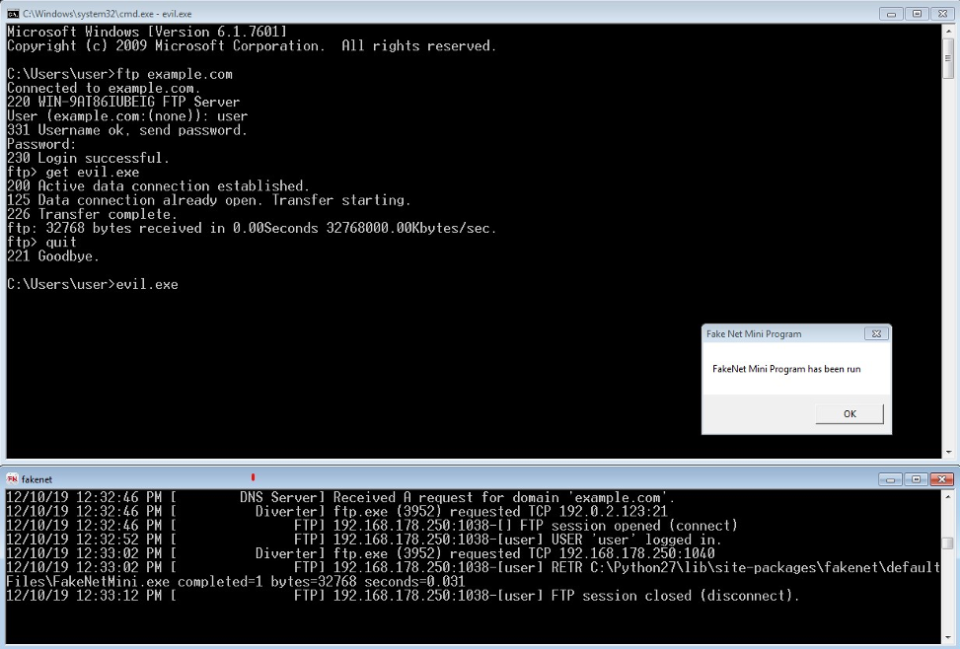
FakeNet Genie: Improving Dynamic Malware Analysis with Cheat Codes for FakeNet-NG
As developers of the network simulation tool FakeNet-NG, reverse engineers on the FireEye FLARE team, and malware analysis instructors, we get to see how different analysts use FakeNet-NG and the […]FireEye Steps Up Effort to ‘Elevate!’ Women in Cyber Security
A few weeks back, our EVP and CMO Vasu Jakkal marked International Women’s Day with a post noting some of the ways FireEye has been helping to lead the way […]Social Engineering Based on Stimulus Bill and COVID-19 Financial Compensation Schemes Expected to Grow in Coming Weeks
Given the community interest and media coverage surrounding the economic stimulus bill currently being considered by the United States House of Representatives, we anticipate attackers will increasingly leverage lures tailored […]This Is Not a Test: APT41 Initiates Global Intrusion Campaign Using Multiple Exploits
Beginning this year, FireEye observed Chinese actor APT41 carry out one of the broadest campaigns by a Chinese cyber espionage actor we have observed in recent years. Between January 20 […]Official agenda of RISK conference 2020 now live!
With our premier annual conference, RISK 2020, set to take place less than one month from now, we are announcing the official event agenda, which will deliver 2 knowledgeful days of technology, […]FireEye’s Michal Ostrowski Invites You to RISK 2020
Michal Ostrowski, Regional Director Eastern Europe, Russia & CIS at FireEye, has created a video invitation, where he states: “I start planning my conference activities for each year with checking […]Load More