McAfee Enterprise Defender Blog | OMIGOD Vulnerability Opening the Door to Mirai Botnet
This month Microsoft released patches for 86 vulnerabilities. While many of these vulnerabilities are important and should be patched as soon as possible, there is one critical vulnerability that McAfee Enterprise wants to immediately bring to your attention due to the simplicity of what is required to exploit, and evidence that possible exploitation is already being attempted.

CVE-2021-38647 (CVSS score: 9.8) – Open Management Infrastructure Remote Code Execution Vulnerability
The list of flaws, collectively called OMIGOD, impact a software agent called Open Management Infrastructure that’s automatically deployed in many Azure services –
CVE-2021-38645 (CVSS score: 7.8) – Open Management Infrastructure Elevation of Privilege Vulnerability
CVE-2021-38648 (CVSS score: 7.8) – Open Management Infrastructure Elevation of Privilege Vulnerability
Azure customers on Linux machines, including users of Azure Automation, Azure Automatic Update, Azure Operations Management Suite (OMS), Azure Log Analytics, Azure Configuration Management, and Azure Diagnostics, are at risk of potential exploitation. OMI can also be installed outside of Azure on any on-premises Linux system.
CVE-2021-38649 (CVSS score: 7.0) – Open Management Infrastructure Elevation of Privilege Vulnerability

The Remote Code Execution is extremely simple and all that is required is to remove the auth header and root access is available remotely on all machines. With this vulnerability the attackers can obtain initial access to the target Azure environment and then move laterally within it.
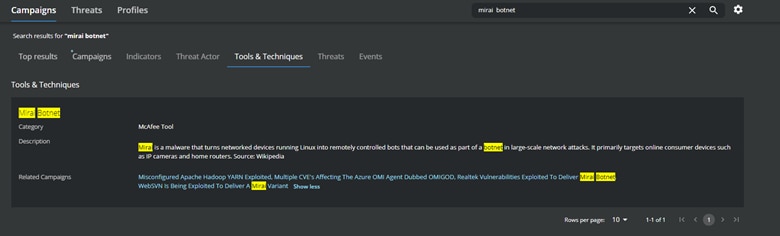
Source: MVISION Insights
Campaign: Multiple CVE’s Affecting the Azure OMI Agent Dubbed OMIGOD
Multiple security researchers shared proof of concept attacks on the exploitation of the vulnerabilities and, soon thereafter, actors mimicked the efforts and have recently been seen actively exploiting CVE-2021-38647 via botnet activities.
Source: MVISION Insights
Background on the Mirai Botnet and related campaigns
McAfee Enterprise Coverage and Recommended Mitigations
Microsoft does not have an auto update mechanism; a manual upgrade of the agents is required to prevent exploitation. Microsoft has released a patched OMI version (1.6.8.1), suggested steps by Microsoft are provided in the below link.
One such botnet is Mirai, which is actively scanning for vulnerabilities, including those identified as OMIGOD, that will allow the operators to infect a system and spread to connected devices. If the Mirai botnet exploits a vulnerable machine, the operators will drop one of the Mirai DDoS botnet versions and close port 5896 on the internet to prevent other attackers from exploiting the same box. Reports of successful exploitation of OMIGOD have reported cryptominers being deployed on the impacted systems.
McAfee Enterprise will continue to update the following KB document with product coverage of CVE-2021-38647; please subscribe to the KB to be notified of updates.
CVE-2021-38647 – Open Management Infrastructure Remote Code Execution Vulnerability
Identifying Vulnerable Systems with the OMI Agent
To identify vulnerable systems in your environment, McAfee Enterprise recommends scanning for systems listening on Ports 5986. Port 5986 is the typical port leveraged by the OMI agent. Industry intelligence from the Wiz Research group is also noting vulnerable systems listening on non–default ports 5985 and 1270. It is recommended to limit network access to those ports immediately to protect from the RCE vulnerability.
McAfee Enterprise coverage for CVE-2021-38647 Remote Code Execution Vulnerability
Detecting Threat Activity with MVISION Insights
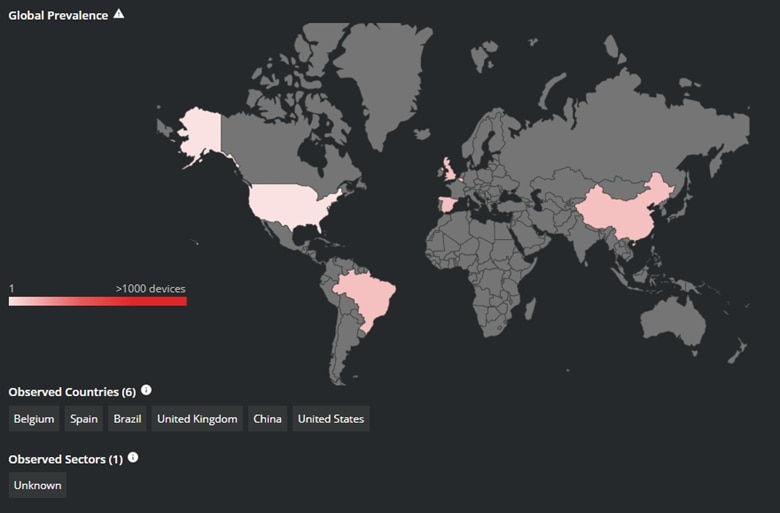
MVISION Insights provides regularly updated threat intelligence for the ongoing attempts to exploit OMIGOD. The “Multiple CVE’s Affecting the Azure OMI Agent Dubbed OMIGOD” campaign will have up to date Global Prevalence, IOCs, and MITRE techniques being observed in the wild. The IOCs within MVISION Insights can be utilized by the Real-time Search function of MVISION Endpoint Detection & Response (EDR) to proactively search your entire Linux endpoint environment for detection.
Global Prevalence of OMIGOD Exploitation Source: MVISION Insights
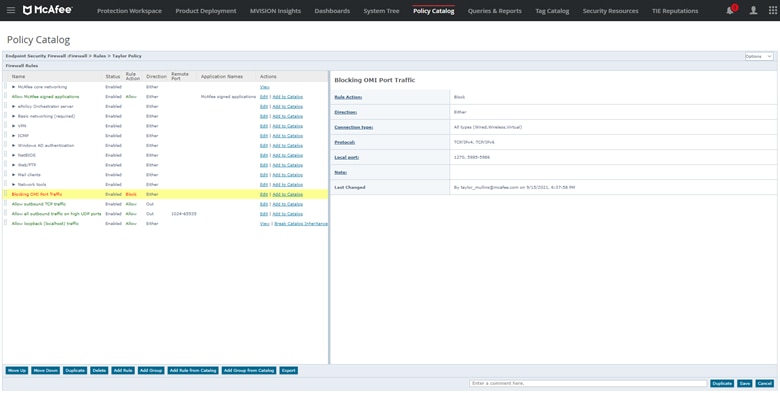
Blocking Ports with McAfee ENS Firewall
The McAfee ENS Firewall Rules will allow for the creation of custom rules to block specific ports until the OMI agent can be updated to the resolved version; please see the below screenshot for a sample rule to block the ports associated with the OMI agent.
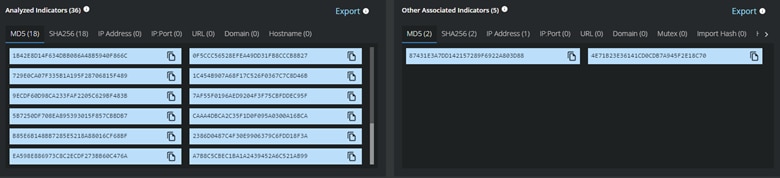
Indicators of Compromise related to exploitation of OMIGOD Source: MVISION Insights
Creation of Block Rule for OMI Agent Ports in McAfee ENS Firewall
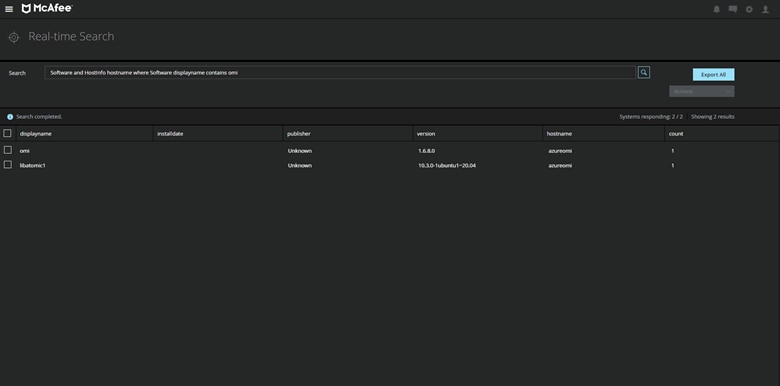
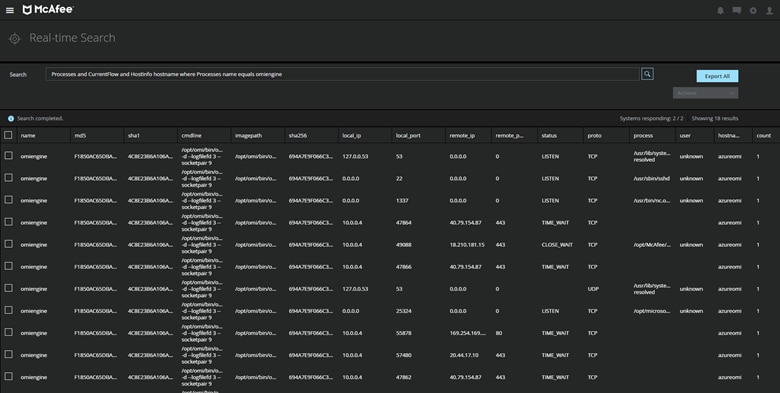
The below pre-built queries can be executed to locate systems listening on the noted ports for the OMI Agent and to verify the version of the OMI agent installed on your endpoint.
Locating Systems Running OMI with MVISION EDR
The Real-time search feature in MVISION EDR with allow for the searching of your entire Linux environment utilizing several different parameters to identify systems that could be potential targets.
Software and HostInfo hostname where Software displayname contains om
Processes and CurrentFlow and HostInfo hostname where Processes name equals omiengine
Locating Installed Software Versions of OMI on Linux endpoints in MVISION EDR
Monitoring the traffic and user information of OMI in MVISION EDR
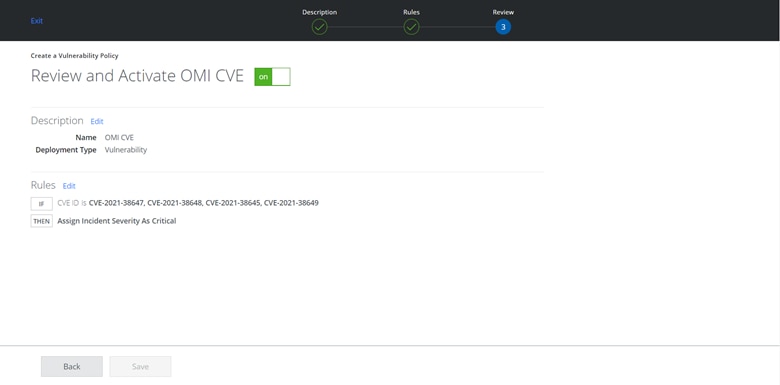
Discovery of Vulnerabilities and Configuration Audits with MVISION CNAPP
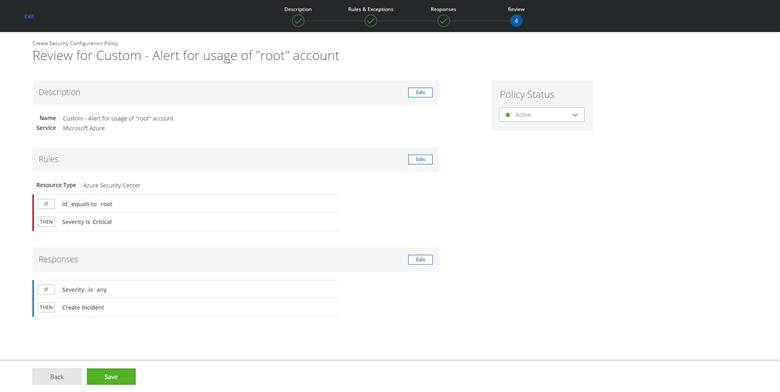
Another method to identify vulnerable systems in your cloud infrastructure is run an on-demand vulnerability scan and create security configuration audits with MVISION Cloud Native Application Protection Platform (CNAPP). Please see below several examples of using the CWPP and CSPM features to locate vulnerable systems by CVE number and detect usage of the “root” account in Microsoft Azure.
Running Vulnerability Scans to Identify Vulnerable Systems by CVE
The post McAfee Enterprise Defender Blog | OMIGOD Vulnerability Opening the Door to Mirai Botnet appeared first on McAfee Blogs.
Setting Security Configuration Audits to be alerted of Root Access in Microsoft Azure
This post was first first published on McAfee Enterprise – McAfee Blogs’s website by Taylor Mullins. You can view it by clicking here

