Perfect Forward Secrecy (PFS) API and SSL/TLS Analysis | AppResponse 11.10 | Riverbed
Keeping track of SSL and TLS security certificates is important. An expired certificate can erode trust in your organization in that customers may no longer want to do business on your website. In fact, Google looks at SSL/TLS configurations as part of its search ranking algorithm. Having an invalid certification can lower your search results quickly.
Even more importantly, according to Gartner, more than 70 percent of malware campaigns in 2020 used some type of encryption to conceal malware delivery, command-and-control activity or data exfiltration. Clearly, it is becoming essential to have visibility into encrypted traffic.
TLS stands for Transport Layer Security and it is responsible for encrypting data in transit over the network. TLS is an updated, more secure version of SSL or Secure Socket Layer. TLS performs data encryption, prevents eavesdropping by intermediaries by using symmetric cryptography, and allows the client to verify the identity of the server.
On the server side, there’s a private key and a public certificate that’s been signed by a trusted third party called a Certificate Authority (CA). Certificates are typically valid for up to two years, although some can be as short as 90 days. Because certificates are issued for a limited time, it is crucial to monitor their expiration date.
AppResponse’s new PFS API
Earlier this summer, Riverbed created a PFS API (Perfect Forward Secrecy) which allowed us complete integrations with two partners—Nubeva and The Load Balancer Crew (LBC)—on symmetric key intercept SSL/TLS decryption technology. This technology allows Riverbed AppResponse users to gain visibility into TLS encrypted application traffic for use in performance and security analysis.
LBC’s integration with AppResponse’s PFS API is an LBC-authored iRules LX script that runs on F5 load balancers and sends TLS 1.2 PFS crypto ephemeral keys to AppResponse. Nubeva offers cloud-hosted and software versions of their symmetric key intercept. It can discover symmetric keys from container and Kubernetes environments, intra-zone VPCs, cloud and pinned traffic. It requires three components:
- A Key Sensor learns and extracts the symmetric keys inter-/intra-host;
- Key Depots are an aggregation and key distributions buffer system, which enables scaling and multi-use;
- A Controller that simplifies management and rule definition along with elastic and automatic deployment of sensors.
SSL/TLS Analysis
Just this week, the AppResponse team released version 11.10, which adds TLS analysis to the Application Stream Analysis (ASA) module among a slew of other great enhancements. AppResponse 11.10 keeps track of the TLS handshake metrics and certificate information. You can enable the new TLS Analysis on the configuration page just by checking the enable box. Once enabled, new rules filter the traffic for TLS handshakes and certificates. All traffic is filtered by default, so you may want to customize the rules to get just the traffic you need.
TLS Handshake Insight
First off, SSL/TLS handshake data is available as a new ASA Insight. It helps you answer important security questions like:
- Which versions of SSL/TLS are being used on the network and in how many sessions?
- Is anything in the network using an obsolete cipher suite?
- Which clients and servers are using specific SSL/TLS versions and cipher suites?
- Is anything in the network using expired X.509 certificates?
- Is anything in the network using renegotiation?
- How many sessions are experiencing SSL/TLS errors in the network?
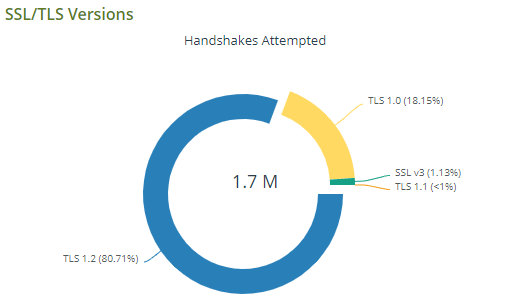
TLS Handshake Insight makes it easy to determine which versions of SSL and TLS are being used and in what quantity.
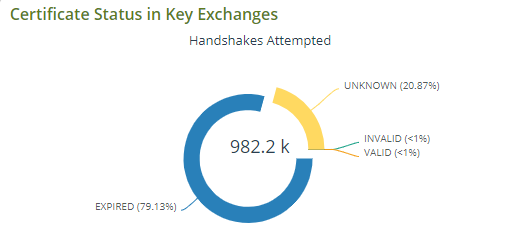
Easily identify invalid, expired or unknown certificates to keep your network, employees and customer safe.
New Certificates Tab
You can find all the certificates listed with information pertaining to expiration, hosts and servers in a tabular format under SSL Decryption for easy viewing and maintenance. It has five sections to help you maintain cert compliance: Installed Keys; Certificates with Installed Keys; Certificates with Missing Keys; Ignored Certificates and PFS. The tab lists all server IPs for a given certificate, and there is more information about the certification in the certificate details section.
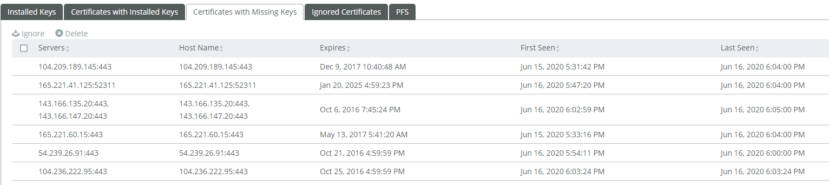
The Certificates Tab shows detailed information about current SSL or TLS certifications and their status.
In short, AppResponse’s new TLS Analysis Insight is essential for anyone who wants to understand their encryption situation. Enterprises are using a variety of encryption technologies and some of them are now obsolete and risky. Riverbed AppResponse can give you the visibility you need to keep your network secure.
For more information
To get TLS Analysis, you need to be running AppResponse version 11.10, which current customers on active maintenance can download free of charge at https://www.riverbed.com/support/. Others should contact Riverbed Sales.
To learn more about our PFS integration partners and how to interact with them, go to the following Knowledge Base articles (login required to access this content):
This post was first first published on Riverbed Blog’s website by Heidi Gabrielson. You can view it by clickinghere

