Biometrics and 2FA

One set of fingerprints. One set of retinas. That’s all we have. Using them and other biometric factors such as palm prints, voice and facial recognition as forms of identification can be risky. If that data is compromised or stolen, refer to the first three sentences in this blog. And it happens. In 2015, the U.S. Office of Personnel Management was breached, and the hackers got away with more than 5.6 million government employee fingerprints.
The three primary concerns to consider with biometric methods of identity management are largely related to implementation, as follows:
- Where the biometric data is stored: For reasons like those cited above, many experts recommend that biometric data – even encrypted biometric data — be stored on a device, such as a smartphone, rather than in the cloud with a service provider or even in databases within an enterprise. Data stored on the authentication device typically means the organization that has implemented biometric verification has no control over that data – putting the user at less risk. If a database of passwords gets hacked, it easily can wreak havoc on a company. But passwords can be changed. If a database of biometric markers for individual employees is breached, there is no easy fix.
- The biometric sample: The sample is what is captured by the biometric sensor device – capturing a retina, for instance, when the eye is brought up to the screen. What is important to consider here is where the sample resides in comparison to the template, which is the matching data stored in a system – often a local server, but sometimes on the reading device itself. If data has the potential to leak from either location, the bio system is at grave risk. While local storage is viewed as efficient from a speed viewpoint, and as a good value, this type of system is also more vulnerable to breaches. In the cases where data is stored in the cloud or on an external server, the threat level increases. One benefit of external storage is that the biometric element can be used in multiple locations (if a company has multiple international offices, for instance). However, even when this data is encrypted, the prospect of putting biometric data in external locations is one that should be carefully considered.
- How the biometric data will be used: We strongly recommend biometrics be used solely to unlock a credential, not to be the actual credential. So, for instance, a biometric marker could be used to unlock access to a work computer but should not be used as a means of egress into the building.
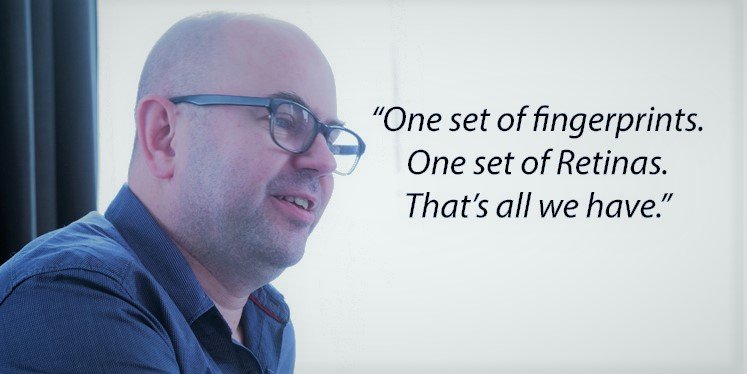
The benefits of biometrics are obvious. Humans are unique creatures. Even identical twins don’t share the same fingerprints, making biometric data one of the best methods of identifying employees . While an employee might lose an access card, his fingerprints and retinas are with him — always. Lots of companies and government agencies use biometric identifiers such as retinal scans or fingerprints as part of a two-factor authentication system. While that’s far more acceptable than using biometrics as the sole form of ID, there are still some important considerations about making biometrics part of a 2FA system.
While biometrics are a great tool for the 2FA tool chest, considerations on how to best protect these unique identifiers should be the first step in any biometric implementation plan. To learn more about our solutions for managing your 2FA system, click here.
By Paul Foley, Versasec, Professional Services Director, Founder
Original Article

