Data Exfiltration is a Big Problem

Call it what you will—data exfiltration, data breach, data loss, or data leakage – the theft of valuable corporate information is a persistent and inescapable problem. Because data routinely moves in and out of an enterprise, data exfiltration can closely resemble normal network traffic, making it challenging for IT security groups to detect data hoarding and exfiltration attempts. Making it worse, nearly half the time a trusted internal actor is responsible for the deed.
Data breaches cause a big headache for the hacked companies. I bet you can easily name two or three companies that have recently been in the news for losing customer data. Marriott Hotel,
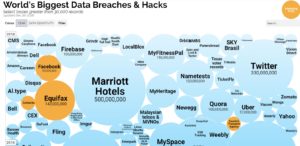
Worlds biggest data breaches or data exfiltration
Facebook, Equifax and Sony are the few that pop into my mind. Check out this World’s Biggest Data Breaches and Hacks infographic to see more examples. It’s mind boggling and scary how frequently it happens. Why does it happen so frequently?
The cost of a data breach
The results of a data breach can be very costly. Some of the costs to containing the damage from a public data loss can include fines and legal fees; investing in new security software to prevent future problems; forensic investigation, audit services and crisis team management; and notifying and compensating customers for credit monitoring services, if the breach includes personally identifiable information (PII) or financial information. But don’t forget, there are other soft costs such as the cost of business disruption and revenue loss from downtime; the cost of lost customers and acquiring new customers; and reputation losses and diminished good will.
According to a Ponemon Institute report on the 2018 Cost of a Data Breach, the global average cost of a data breach is up 6.4% from 2017 to $3.86 million. Yikes! And, the average cost for each lost or stolen record containing sensitive and confidential information is $148.
The question is, why are there so many data breaches and what can you do about it?
Varied means of data exfiltration
There are many ways to transfer data from one computer to another device. Attackers can use a mix of legitimate and malicious tools and techniques to extract specific data from your systems. Here are several common ways:
- If an attacker has insider access to your systems or network, one way to exfiltrate data is manually with a thumb drive, CD, or DVD. Simple, effective and difficult to track unless data hoarding occurs first. Even if you don’t see the final transfer, you can see the would-be exfiltrator collecting data.
- Fake anti-virus hosts sites frequently trick users into installing malware that masquerades as virus protection software. The host site is also typically the exfiltration location.
- Spyware that watches what you do on your computer, steals credentials and passwords, but also documents and files, and communicates them to a spyware download site. Spyware is often installed during a phishing attack.
- Brute force is the simplest method to gain access to a site or server (or anything that is password protected). It tries various combinations of usernames and passwords again and again until it gets in. The trick to stop this form of attack is to use strong passwords, not admin/admin or the like.
There are also several legitimate tools hackers can leverage to steal data:
- File transfer protocol (FTP) is a standard network protocol used to transfer files but can also be used for data exfiltration.
- Web applications: Attackers open their own browsers and directly access information.
- Microsoft Outlook forwarding rules enable attackers to forward themselves copies of the emails that their target users receive.
- Uploading to Dropbox or similar file sharing site are super common and a great place to steal data. These sites are very visible to network security analytics—even over encrypted connections—and they can’t hide the fact that they’re moving data.
- Windows Management Instrumentation (WMI) can be used to check the files opened by the targeted users. As such, cybercriminals can easily determine and gather these files for transferring data.
Sometimes the data is encrypted before exfiltration to hide the information from detection or to make the exfiltration less conspicuous. Encryption gets around some of the protections customers use to watch for the movement of specific files, since they don’t recognize the files anymore. Seeing the network transfer from a sensitive asset is one clues to recognize data loss.
Exfiltration isn’t always malicious. Many data breaches have been the result of mistakes (emailing the wrong file to a client, sending docs to Google Drive or Dropbox to work on from home because the VPN connection is terrible, etc.). Some reported data breaches may not have even happened! In cases where PII information has been exposed, the company has to treat it as leaked if they can’t prove that nobody downloaded it. It’s just as expensive either way.
Protect your critical assets
SteelCentral NetProfiler Advanced Security Module provides full-fidelity flow analytics for network and security monitoring on a single screen. It provides the crucial insights and empirical evidence you need to investigate data exfiltration and other threats fast and confidently.
- Detect data loss sooner. Use threat feeds and blacklists to identify known bad behaviors on the network that can lead to data exfiltration, including botnet command and control, malware download locations, etc.
- Identify suspicious activity. Security analytics can identify reconnaissance, brute forcing, scanners, or suspicious new connections that could mean you have an on-going data breach.
- Isolate problems faster. Quickly determine who was involved, what was impacted, when and where the breach occurred so you can initiate quarantine procedures and implement a fix. Reports that can help include “Top external consumers of data” and “Large/long outbound flows”.
- Eradicate data loss problems. Proactive cyber threat hunting workflows can uncover past breaches, data staging or even ongoing exfiltration.

