Qualys Research Alert: Prepare for a Critical Vulnerability in OpenSSL 3.0
On Tuesday, November 1, 2022, the OpenSSL project will release a new version of OpenSSL version 3.0.7 that will patch an as-yet-undisclosed vulnerability in current versions of OpenSSL.
OpenSSL rates the severity of the vulnerability as CRITICAL, which means this vulnerability affects common configurations and is also likely to be exploitable. Examples include significant disclosure of the contents of server memory (potentially revealing user details), vulnerabilities that can be easily exploited remotely to compromise server private keys, or where remote code execution (RCE) is considered likely in common situations.
What is OpenSSL?
OpenSSL is the core open-source library that implements SSL and TLS protocols which makes it possible to securely communicate over the internet.
What do we know so far?
Vulnerability Impact
The details of the vulnerability are not known, but given the critical nature of the vulnerability, it would likely result in the disclosure of server memory, potentially reveal user details, and potentially exploit it remotely to compromise server private keys or execute remote code.
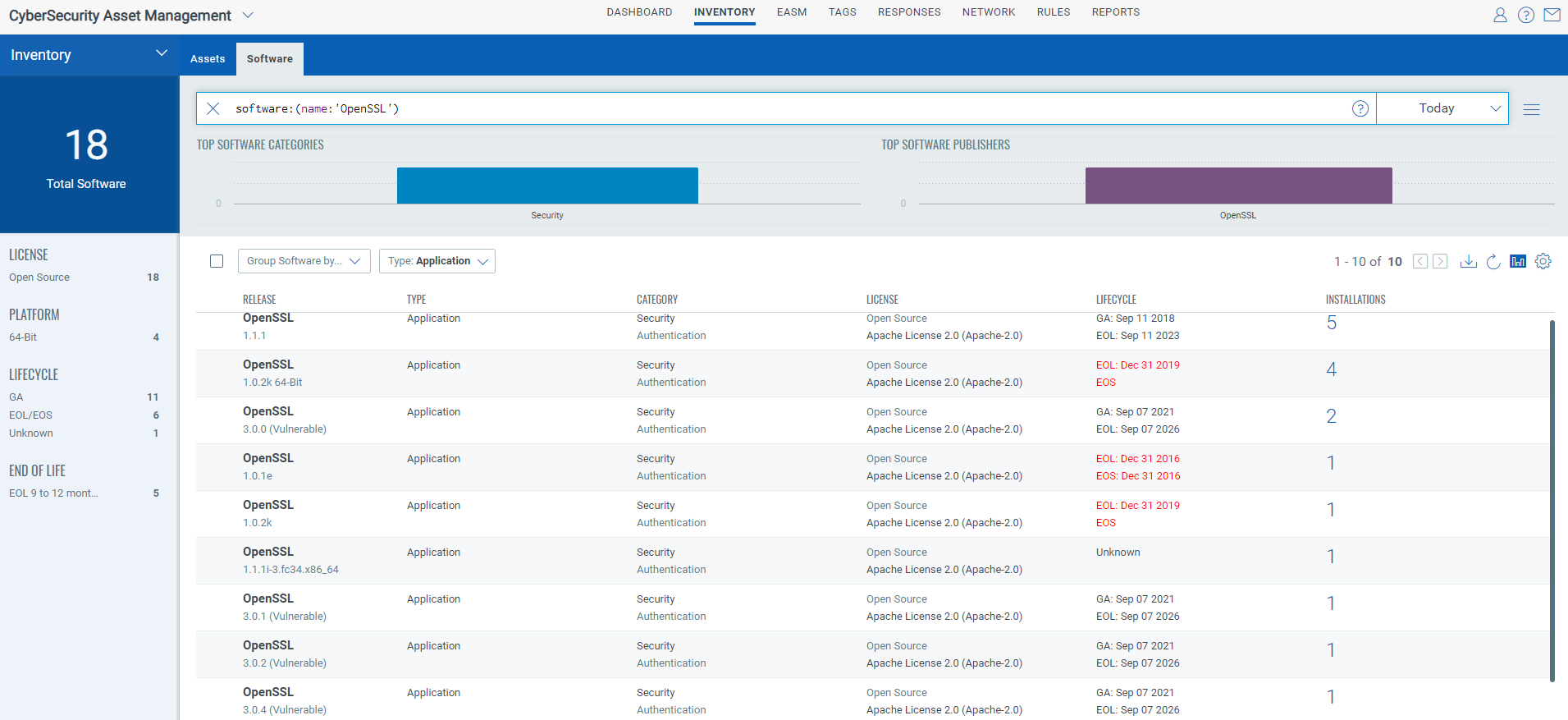
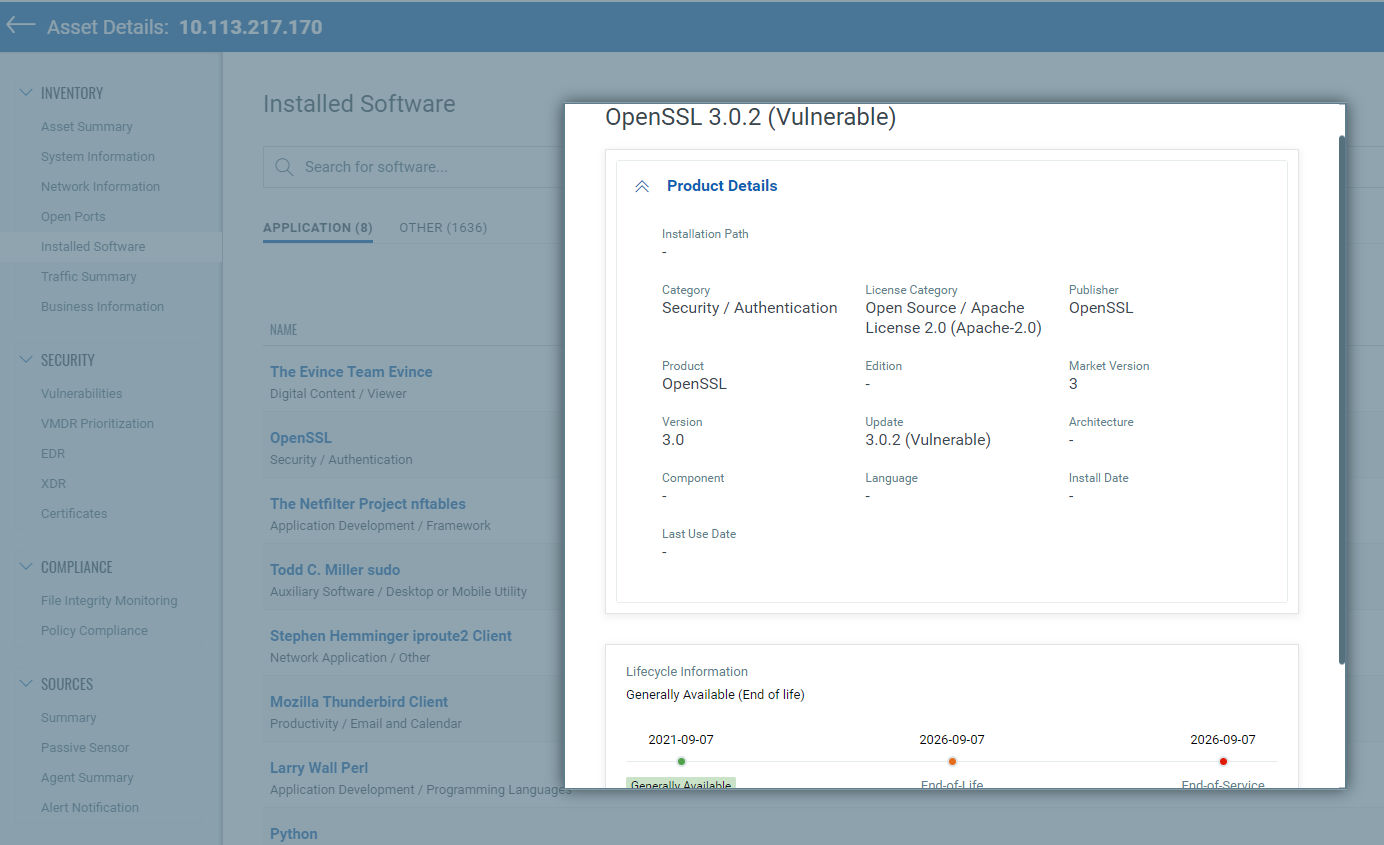
Vulnerable Versions
Only OpenSSL versions 3.0 through 3.0.6 are vulnerable. The commonly deployed OpenSSL 1.x versions are not vulnerable.
What should organizations do?
Organizations should prioritize inventorying all systems with vulnerable versions of OpenSSL.
Information is still being released leading up to the disclosure. The Netherlands National Cyber Security Center NCSC (NCSC-NL) in collaboration with CERT-Bund from Germany and the CISA has centralized information on the vulnerability on the NCSC-NL Github page. Here you will find information on vulnerable software, scanning utilities, as well as IOCs associated with any attacks exploiting this vulnerability.
How can Qualys Help?
Inventory OpenSSL Using Qualys CSAM
Qualys CSAM makes it easy to identify assets containing OpenSSL. The following CSAM Software QQL query will identify assets with OpenSSL installed.
Software Query: software:(name:"OpenSSL 3.0.*" and not name:"OpenSSL 3.0.7")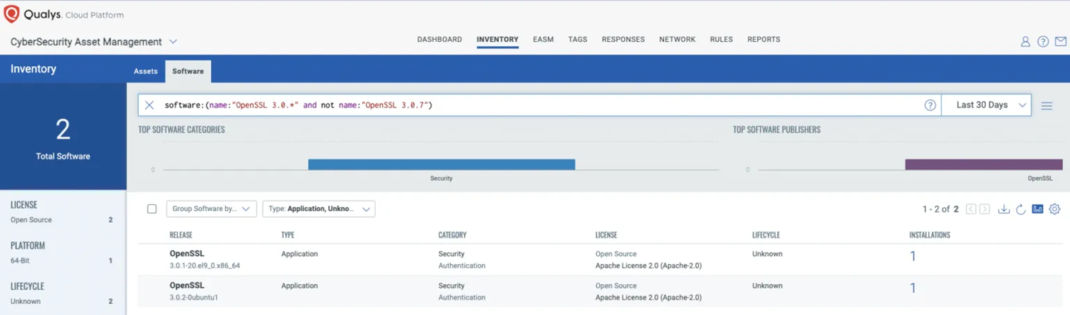
The above QQL will help identify assets that have a vulnerable version of OpenSSL installed.
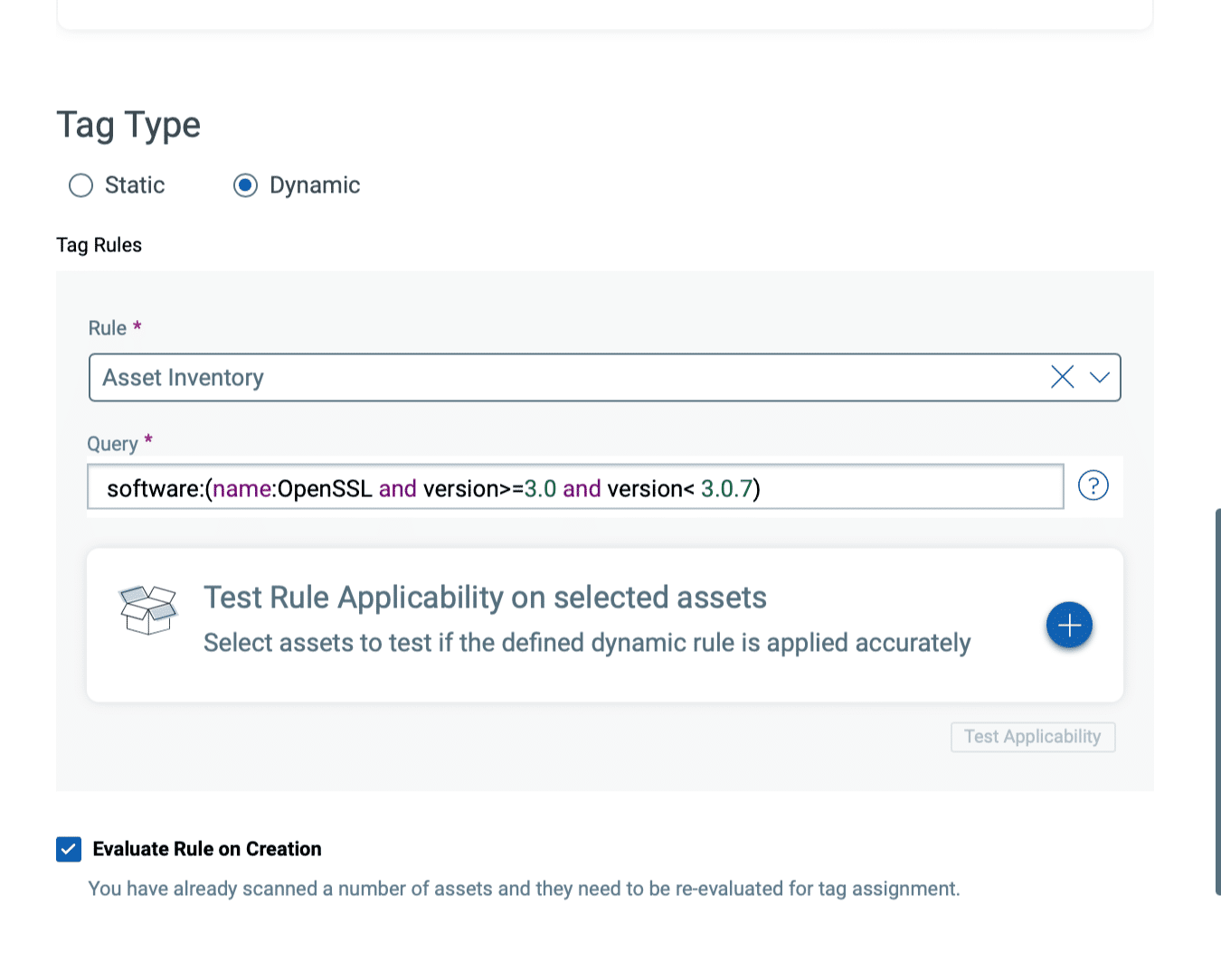
Tag Potentially Vulnerable Assets with CSAM
In addition to identifying the assets, Qualys also recommends customers tag the assets with OpenSSL installed.
Discover Vulnerable Instances Using Qualys VMDR
Qualys QID Coverage
Qualys has released QID 38879 to help customers detect vulnerable versions of OpenSSL 3.0.x. The QID is available starting VULNSIGS-2.5.617-4 and lx-2.5.617.4-3. Qualys will release additional QIDs as and when the respective vendors make the advisories and patches available.
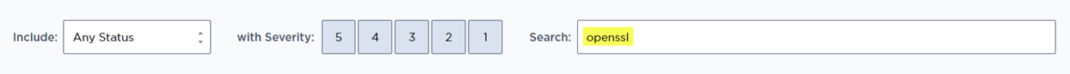
Search for the following QIDs in your subscription to find vulnerable instances.
| QID | Title | Supported On | Release Versions |
|---|---|---|---|
| 38879 | OpenSSL 3.0 < 3.0.7 Critical Vulnerability | Agent + Scanner | VULNSIGS-2.5.617-4 and lx-2.5.617.4-3 |
Please note, once the vulnerability is disclosed on November 1, 2022, each vendor will likely release backported patches for the vulnerability. The Qualys Research Ream is closely tracking the vulnerability and will release QIDs to detect those backported versions.
Please stay tuned for more updates. Qualys Research team will be regularly updating the blog as more details become available.
We encourage our customers to leverage our Vulnerability Detection Pipeline to track new vulnerability detection development and status.
This post was first first published on Qualys Security Blog’ website by Bharat Jogi. You can view it by clicking here

