Introducing Qualys VMDR 2.0
Over the last five years, the number of vulnerabilities disclosed has doubled. The speed at which vulnerabilities are weaponized and leveraged for mass exploitation is down to mere days (from weeks). For example, mass exploitation of the Log4Shell vulnerability at the end of 2021 occurred <48 hours after initial disclosure. Yet organizations take more than 30 days on average to patch critical vulnerabilities, leaving organizations exposed to unnecessary risk.
Qualys pioneered cloud-based vulnerability management software more than two decades ago. When we announced Qualys VMDR in 2020, these broader trends were evident to us. Qualys VMDR consolidated four foundational aspects of vulnerability management into a single all-in-one integrated solution to discover, assess, prioritize, and patch critical vulnerabilities at scale.
The first generation of Qualys VMDR helped organizations get instant visibility into an increasingly hybrid and fragmented IT infrastructure “in under two seconds”, detected new vulnerabilities faster than ever before (on average in four hours or less), prioritized based on threat intelligence, and remediated faster than traditional patch management solutions.
In our most recent analysis, Qualys VMDR customers using Qualys Patch Management patched CISA’s Top 15 known exploited vulnerabilities of 2021 up to 60% faster than customers with traditional patch management solutions, dramatically reducing mean time to remediation (MTTR). In short, “Qualys VMDR 1.0” revolutionized vulnerability management.
Defining the Future of Qualys VMDR
After we released Qualys VMDR in 2020, we embarked on an in-depth listening tour with our customers. What did they want us to focus on next?
The recurring theme that emerged was Cyber Risk Management.
CIOs and CISOs crave answers and insights on some critical questions:
- How can we quantify enterprise risk to measure it reliably and consistently over time?
- Where is our organization exposed to the highest risk?
- Which vulnerabilities pose the highest risk to our organization?
- What actions do we need to take to reduce risk?
- Which assets or groups of assets pose the highest risk to our organization?
- How can we measure and communicate the effectiveness of our cybersecurity programs?
- How can we automate our manual processes so that we respond to threats faster and reduce risk?
It was clear that to these cybersecurity leaders, it was all about managing cyber risk.
With that in mind, we’ve built the next generation of VMDR. We call it Qualys VMDR 2.0.
About Qualys VMDR 2.0

Qualys VMDR 2.0 is an all-in-one risk-based vulnerability management solution that quantifies cyber risk. It gives organizations unprecedented insights into their risk posture and provides actionable steps to reduce risk. It also gives cybersecurity and IT teams a shared platform to collaborate and the power to quickly align and automate no-code workflows to respond to threats, thanks to seamless integration with QFlow and ServiceNow ITSM.
Let’s unpack everything that’s new in this update of Qualys VMDR.
Accurately Quantify Cyber Risk
Risks posed by modern cybersecurity threats are multifaceted. To accurately assess the true risk to your specific organization from vulnerabilities, assets, or groups of assets requires taking multiple factors into account.
For example, a vulnerability with CVSS rating of 9, with no exploits available, is a lower risk than a vulnerability that has a CVSS rating of 7.5 but has a weaponized exploit available and is being actively exploited in the wild.
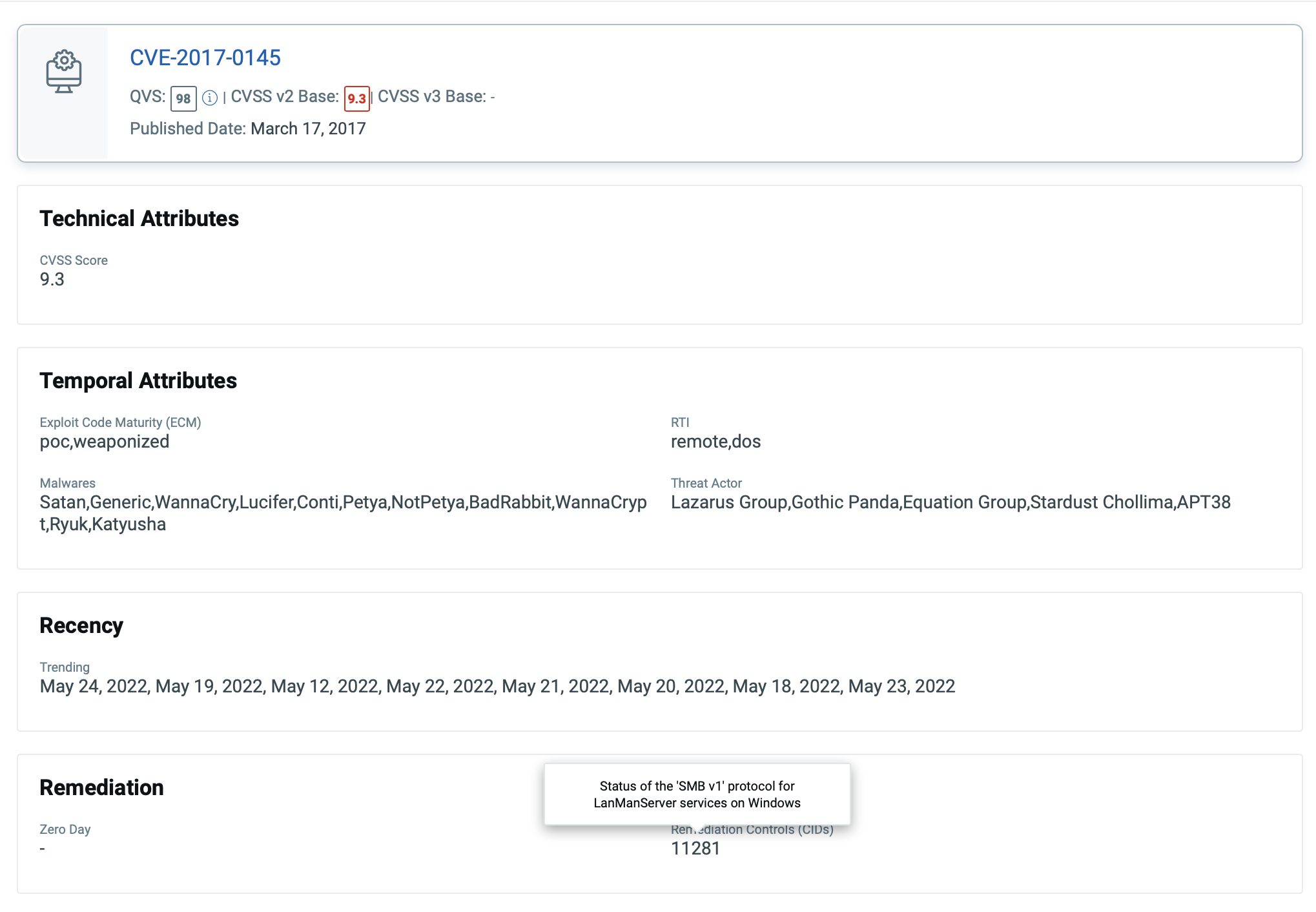
Similarly, an actively exploited vulnerability is a low risk on an asset if mitigation or compensating controls are applied. One of the classic examples was to disable SMBv1 to defend against WannaCry exploitation (a.k.a. MS17-010). If SMBv1 was disabled, then the risk of exploitation was greatly reduced, hence the risk from that vulnerability on that asset should be lower.
At the asset level, similar dynamics are at play. Multiple factors need to be considered to determine the true risk of an asset to the organization. Consider questions such as:
- How critical is the asset?
- Where is it located? Is it internal or internet-facing?
- What is the criticality of the vulnerabilities on the system?
- Is the system hardened based on best practice guidance?
- Is there evidence of malware or end-of-life software or other risk factors?
After all, a squeaky-clean asset with no vulnerabilities but poorly misconfigured, thus giving broad unauthorized access to customer data, can be equally damaging to an organization.
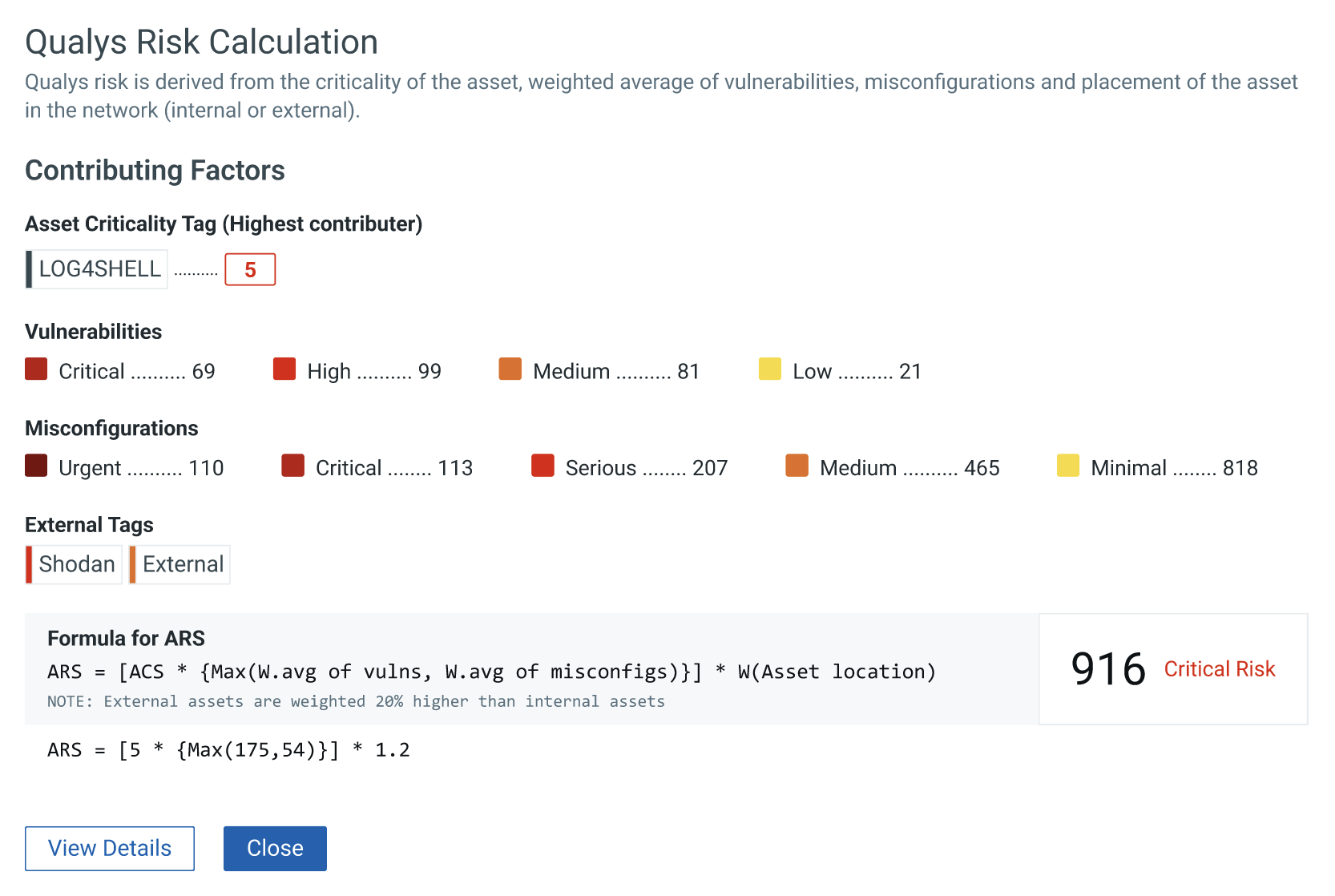
VMDR 2.0 with Qualys TruRiskTM automatically assesses multiple factors such as the asset criticality, its location, the vulnerabilities/misconfigurations found on the system, any compensating controls applied on the asset to reduce risk, exploit code maturity on the vulnerabilities, evidence of active exploitation, and many more such factors. Qualys TruRisk quantifies an organization’s true risk so that IT and Security teams can focus on what’s important. It does this by introducing multiple risk scores.
Let’s review the kinds of risk scores delivered by Qualys TruRisk.
Qualys Detection Score (QDS)
Qualys Detection Score (QDS) transparently rates the criticality of the Qualys vulnerability finding (i.e. QID) by considering multiple factors such as CVSS base score, exploit code maturity, active exploitation by malware or threat groups, real-time threat indicators, active exploitation in the wild, and most importantly any mitigation or compensating controls applied on the system.
The QDS score for a QID is specific to the asset on which it is detected. If an asset is protected from a vulnerability due to a compensating control, then the risk is rated lower.
Asset Risk Score (ARS)
Qualys Asset Risk Score determines the score of an asset by considering multiple aspects of the asset and provides a transparent, easy-to-understand risk score. The key ingredient to the ARS is the asset’s criticality, which is automatically determined from integration with the customer’s CMDB. It also considers the location of the asset as well as the vulnerabilities and misconfigurations found on the system to determine the score.
Identify Highest Risk Assets in Seconds
The Qualys risk scores described above form the foundation to quickly assess risk across the organization and understand where the highest risk resides. By combining them with asset tags, asset groups, business units, and Qualys Query Language (QQL) queries, organizations can quickly get a heat map of their risk exposure within seconds, take actions to reduce risk, and track risk reduction over time. These key features help organizations measure the effectiveness of their cybersecurity program.
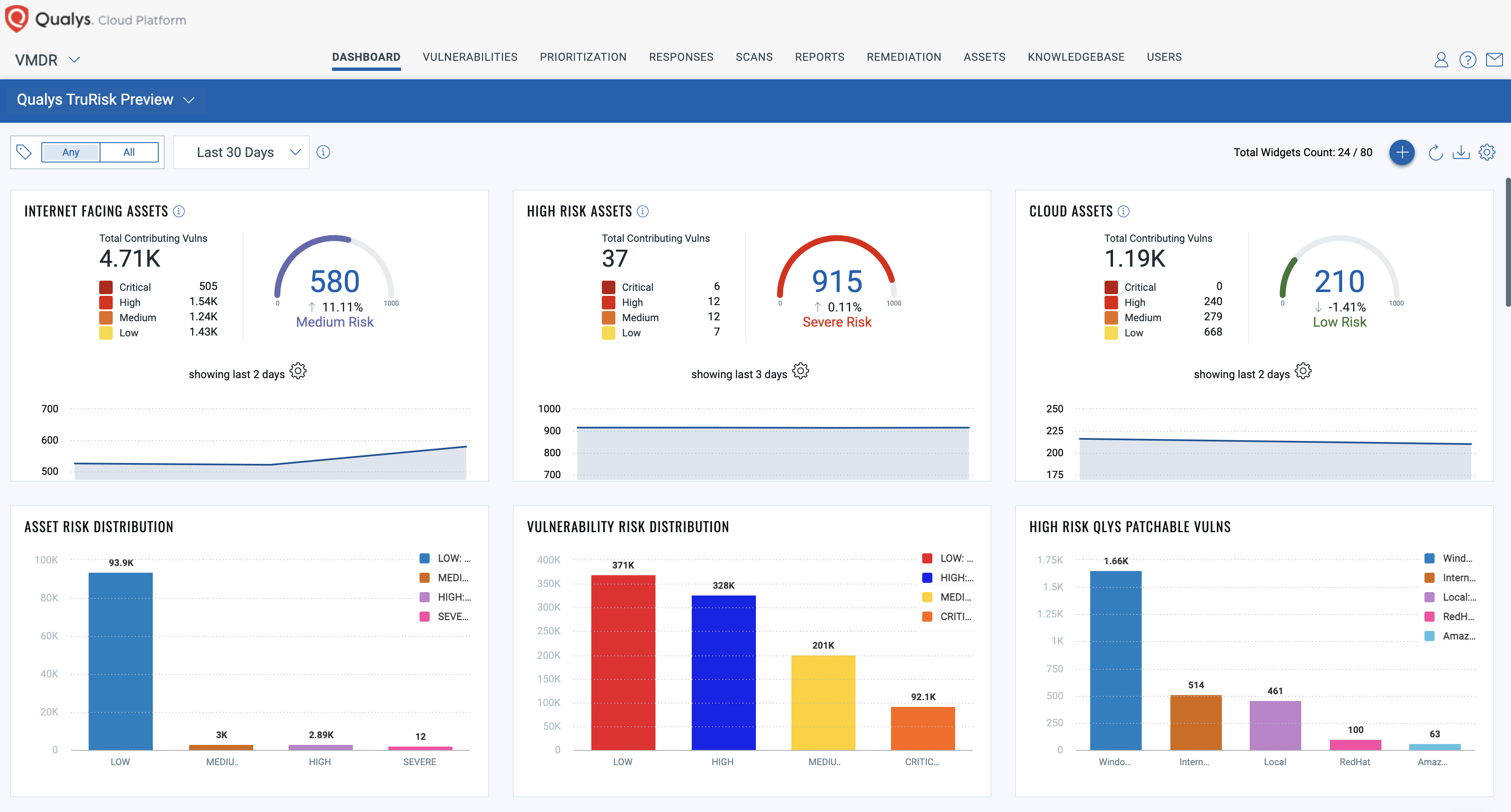
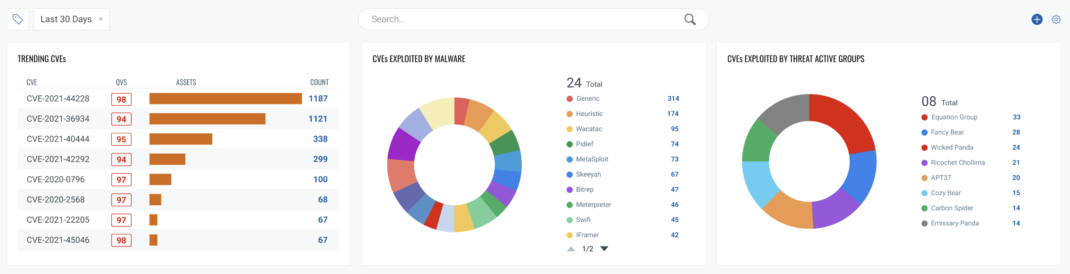
Qualys QDS and Qualys ARS risk scores are powered by in-depth exploit and threat intelligence for more than 180,000 vulnerabilities, sourced from 25+ different threat intelligence sources. These range from exploits available in commercial tools such as Canvas to open-source tools such as Metasploit to trending data that tracks active exploitation of vulnerabilities in the wild. Qualys also tracks exploits published daily on GitHub, which is increasingly becoming the go-to place to publish exploits.
The real-time collection of both exploit and threat intelligence allows organizations to effectively prioritize vulnerabilities based on risk. These would not have been prioritized by traditional CVSS score-based prioritization since they lack both threat and risk context. In the example below, a medium CVSS score is assigned to CVE-2021-36942 based on NVD data, yet it is rated higher by Qualys TruRisk since it has weaponized exploit code available, evidence of active exploitation by malware and threat groups, and is actively exploited in the wild.
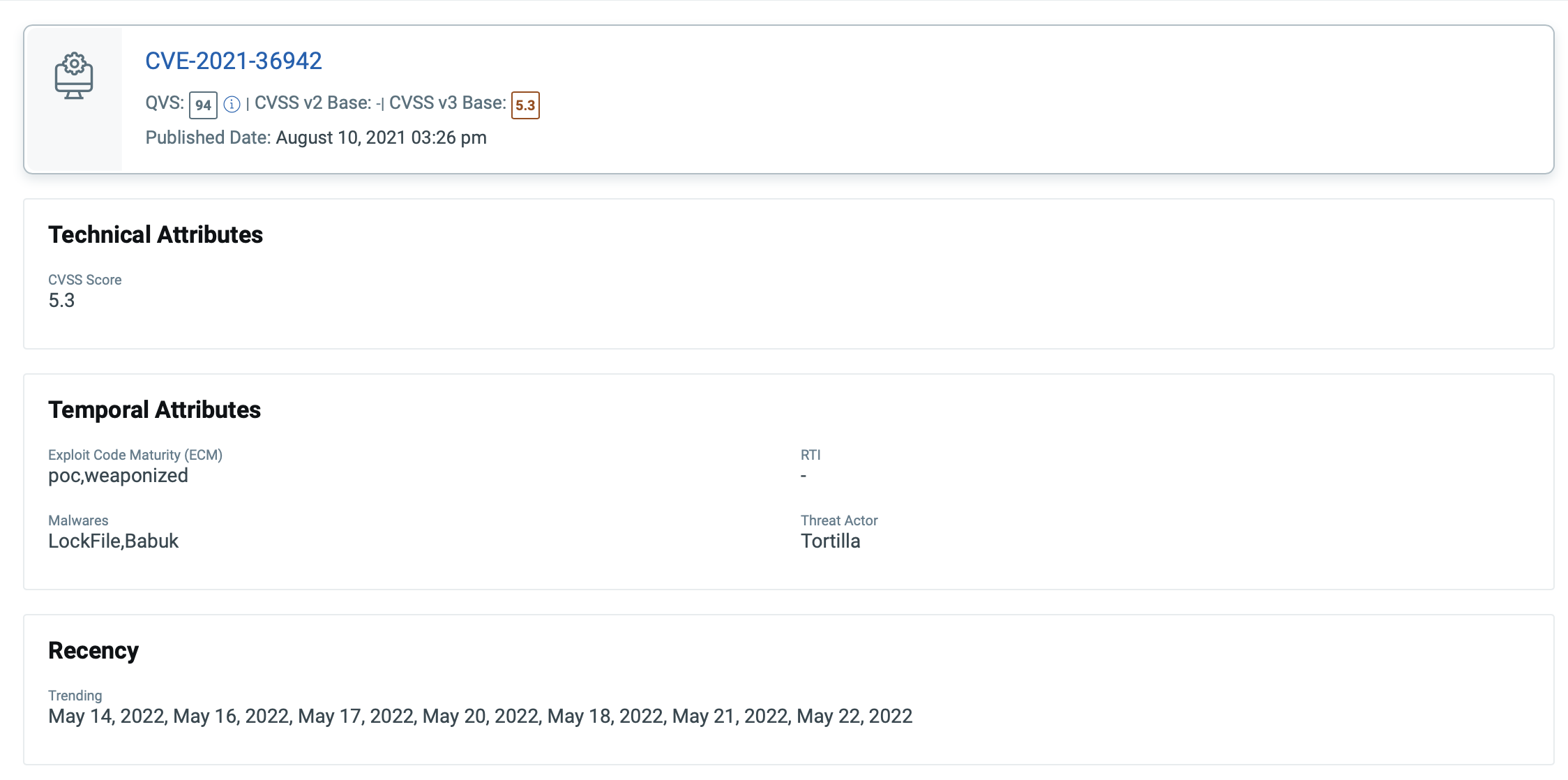
Our transparent risk prioritization algorithm gives enterprises complete confidence to prioritize even unprioritized vulnerabilities and then to explain these decisions to all relevant stakeholders.
Close the Gap between IT & Security
For a vulnerability management program to be successful in any organization, three key elements – people, processes, and tools – need to converge and collaborate.
This is easier said than done.
Vulnerability management teams continue to struggle with manual processes relying on spreadsheets or passing PDF reports to IT teams to remediate and track the status of vulnerabilities. This process is inherently prone to errors and exposes organizations to unnecessary risks when critical vulnerabilities take too long to remediate.
On the other hand, IT teams are overwhelmed with a long list of vulnerabilities to patch… without a clear understanding of what to patch first, how to track the status of remediation, and how to ensure that SLAs are not breached.
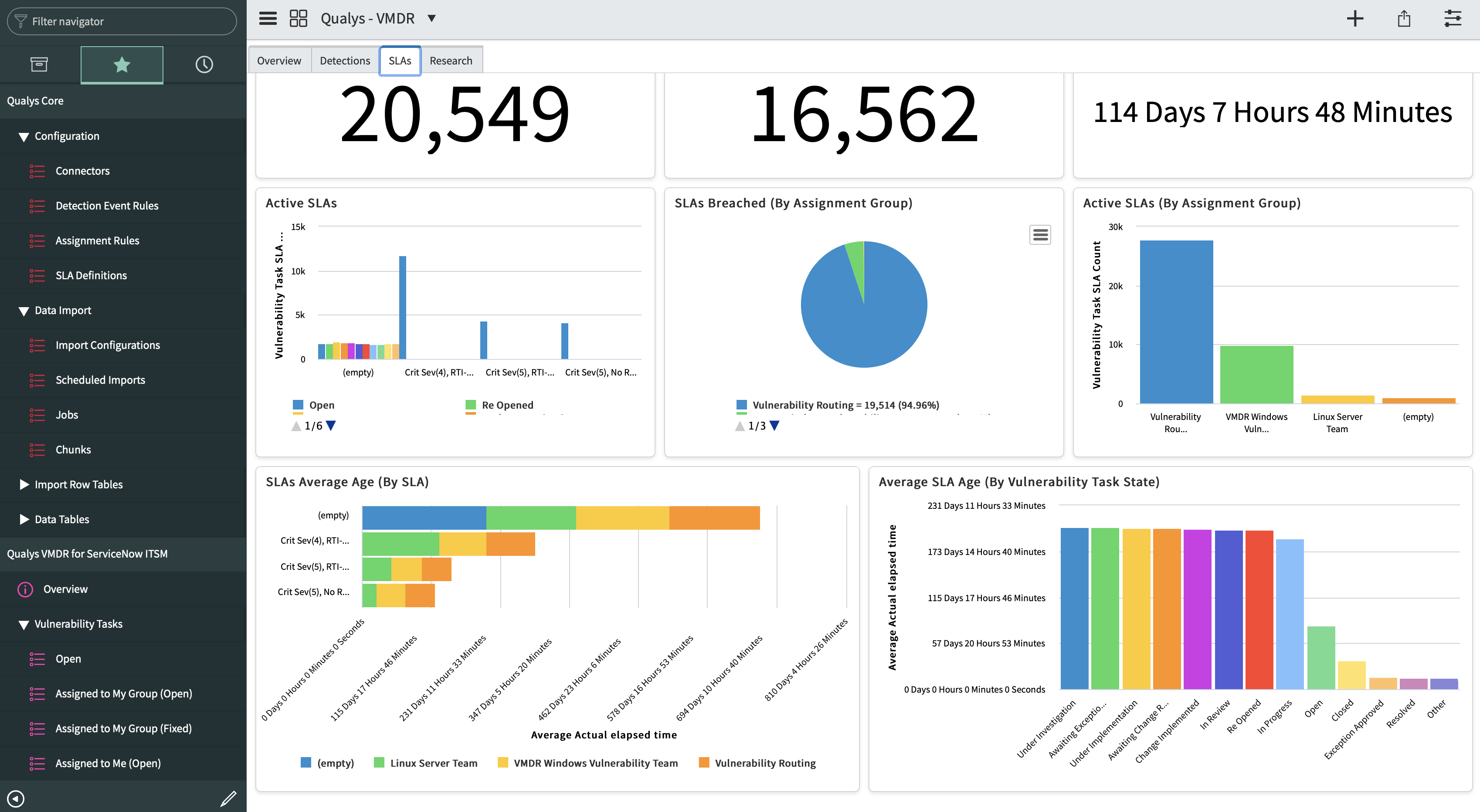
To address these challenges, Qualys has introduced Qualys VMDR for ITSM, a new certified ServiceNow app on the Now Platform, which allows IT and Security teams to share context while working to address vulnerability remediation end to end.
It allows IT teams to import Qualys findings directly into ServiceNow ITSM on-demand or scheduled based on pre-defined criteria. IT can create tickets, assign them to rightful owners, and automatically close them out once the vulnerabilities are remediated.
It also automatically matches the assets to the configuration items (CI) by default. The CI matching is greatly enhanced with the optional Qualys CMDB Sync app available on the ServiceNow store.
Automate Operational Tasks
Qualys VMDR 2.0 also integrates with QFlow technology which delivers drag-and-drop visual workflows that empower team collaboration. They can easily orchestrate complex vulnerability management tasks such as launching scans on ephemeral cloud assets or quarantining high-risk assets, purging terminated assets saving valuable time and resources for both IT and Security teams.
Receive Preemptive Attack Alerts
Qualys VMDR 2.0 leverages comprehensive threat and exploit intelligence to automatically map malware to CVE’s and proactively alert teams on vulnerabilities exploited by malware or those used in an active malicious campaign known to target your organization or industry.
API-first Solution
Qualys VMDR with TruRisk is designed with an API-first approach that helps IT and Security teams get risk insights over API’s which can be directly imported from third party platforms to support reporting and analytics use cases.
All-inclusive with Qualys VMDR
Qualys VMDR with TruRisk, Qualys VMDR for ITSM, and all other capabilities discussed in this blog are included with a Qualys VMDR 2.0 license.
Turbo Charge VMDR 2.0 with Qualys Cloud Platform
That’s not all. Qualys VMDR 2.0 turbo charges other cloud services on the Qualys Cloud Platform.
Qualys Cyber Security Asset Management (CSAM)
Automatically bring attack surface visibility directly into Qualys VMDR with integrations such as Shodan to prioritize assets exposed to the internet.
Automatically sync business criticality with asset criticality in Qualys to drive accurate asset risk scores.
Accurately identify all assets in Qualys VMDR for ITSM based on accurate matching using our CMDB Sync app.
Qualys Patch Management (PM)
Leverage Qualys QDS risk scores and patch reliability score to automatically patch vulnerabilities based on risk, including those known to have minimal impact from a operational point of view. Use zero-touch patching to reduce risk instantly.
Qualys Multi-Vector EDR
Correlate malware events with vulnerability exploitation, quickly assess other assets vulnerable to the same CVE, and then patch them to stop the propagation of malware.
Availability
VMDR 2.0 with Qualys TruRisk will be available in late June, 2022. To request a free trial, visit https://www.qualys.com/forms/vmdr/.
Join Us on June 7th
Qualys invites you to learn how to manage your company’s true risk.
If you can, join us in person at QSC San Francisco (happening in parallel with the RSA show) on June 7, 2022. Register to attend.
Can’t attend in person? Watch our exciting announcement streaming LIVE on June 7th from 10AM to Noon PST. Register to watch.
Ready to learn more?
This post was first first published on Qualys Security Blog’ website by Mehul Revankar. You can view it by clicking here

