SASE, Cloud Threats and MITRE
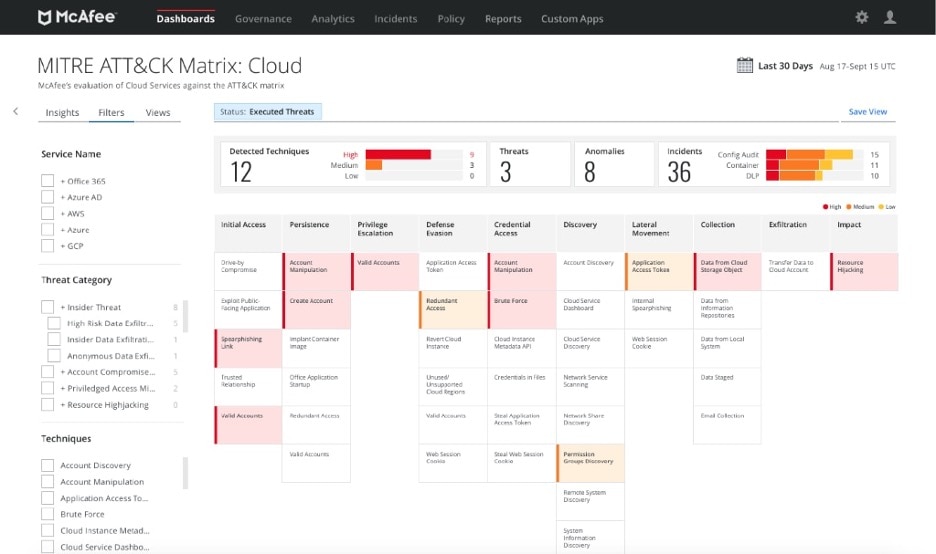
As a quick refresher, the MITRE Att&CK Matrix represents the relationship between attacker Tactics and Techniques:

As you know, McAfee Enterprise’s MVISION Unified Cloud Edge (UCE) was the was the first of all the SASE vendors to implement the MITRE ATT&CK Framework for Cloud last year. An important aspect of Gartner’s SASE Framework is the ability for effective Threat Protection and Resolution in the Cloud. MVISION UCE takes this to the next level – the product takes a multi-layered approach to cloud threat investigation that can speed your time to detect adversary activity in your cloud services, identify gaps, and implement targeted changes to your policy and configuration.
- Tactics. A tactic describes the objective, or why the adversaries are performing the attack. In the ATT&CK Matrix, the table header represents tactics.
- Technique. A technique describes how adversaries achieve their tactical objectives. For example, what are the various technical ways performed by attackers to achieve the goal? In the ATT&CK Matrix, the table cell represents techniques.
This Dashboard is available within the MVISION Cloud console by accessing the Dashboards > MITRE Dashboard link
In this post, I shall summarize some of the significant highlights that we have introduced in the past few releases:
Ever since the launch of this truly differentiated product offering, we have seen a tremendous amount of interest and adoption of this feature within our existing customers. Over the past few months, we have continued to make significant enhancements as part of our MITRE Dashboard.

Executive Summary Section
The Executive Summary displays an at-a-glance view of the current count of Threats, Anomalies, Incidents, types of incidents, and Detected Techniques with severity.
- Service Name. The name of the cloud service.
- Threat Type. The name of the threat type.
- Status. The MITRE Threat statuses available are:
- Executed Threat. Threats that caused risk to your cloud service security.
- Potential Threat. Threats that have the potential to cause risk to your cloud service security. It is recommended to look into the Potential Threats to reduce the impending risk.
- Top 20 Users. Top 20 users who are impacted by the attacks.
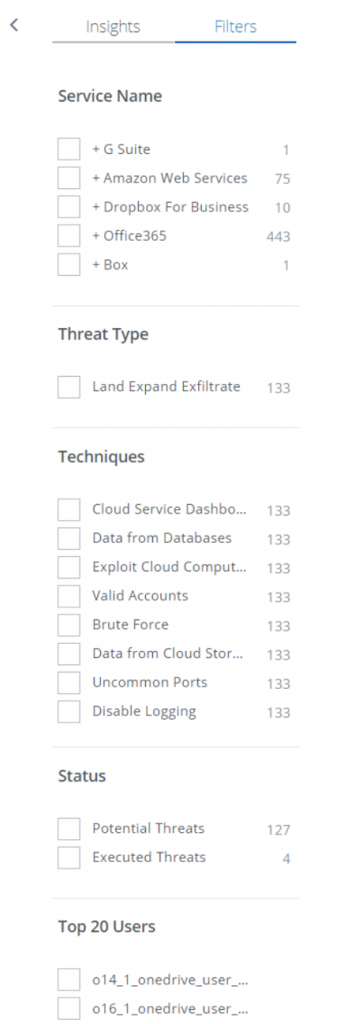
Flexible Filters
To suit the needs of the different teams that would be using the MVISION Dashboard, we now have the ability to filter the MITRE Dashboard by using a variety of facets:
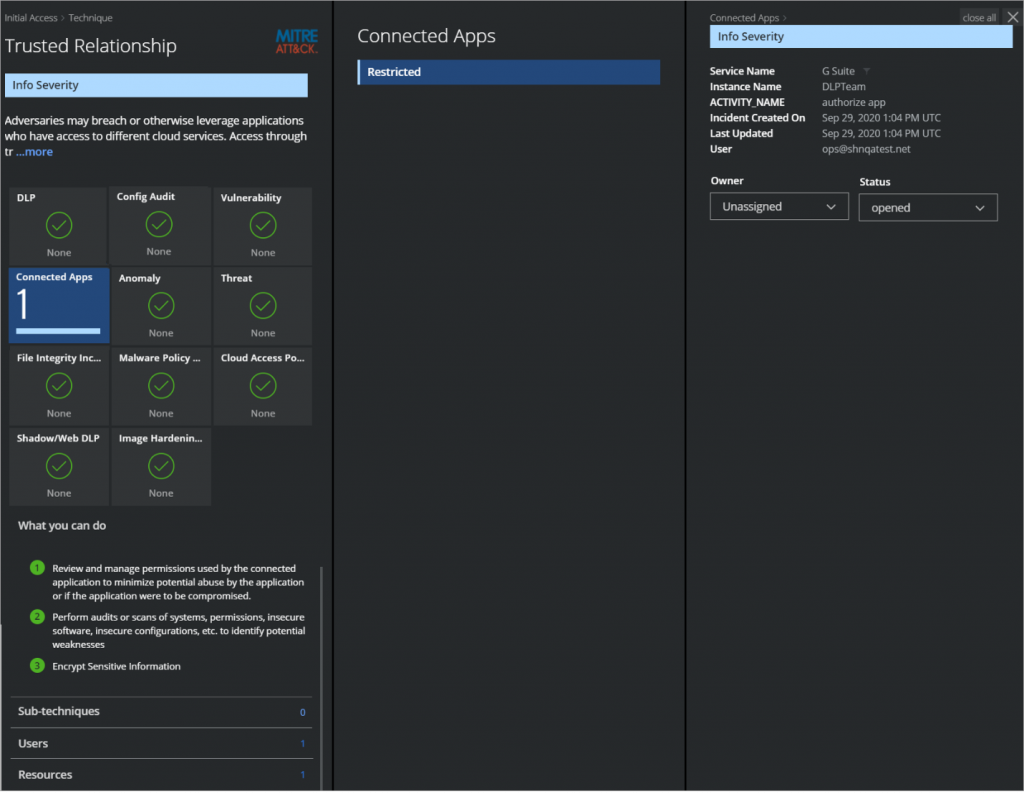
To view the details of the detected techniques:
Detected Techniques – Risk and Drilldown
When an incident is detected for a technique in MVISION Cloud, a severity is computed. The detected techniques are categorized based on the severity of the incidents. Each detected technique is interactive and leads to more detailed explanations.
With McAfee Enterprise, threat investigation isn’t just for one environment – it is for all of your environments, from cloud to endpoint to your analytics platforms. With MVISION Cloud, MVISION EDR, and MVISION Insights, your enterprise has an extended detection and response (XDR) platform for the heterogenous attacks you face today.
- Click any technique on the ATT&CK Matrix table to view the Technique Cloud Card. For example, you can click one of the techniques under the Initial Access category such as Trusted Relationship to learn how an attacker gained access to an organization’s third-party partners’ account and shows the details of compromised Connected Apps.
- Next, click the Connected Apps Mini Card to view an extended cloud card that displays the restricted details of Connected Apps.
- Then click the link to the specific restricted Connected App to see an extended view of the compromised Connected Apps incident.
- Info severity details allow you to investigate and apply a remediation action. As a remediation action, select and assign the Owner and Status from the menu.
MITRE ATT&CK® as a Framework for Cloud Threat Investigation
Want to learn more about how you can leverage MITRE ATT&CK to extend your detection and response capabilities to the cloud?
The post SASE, Cloud Threats and MITRE appeared first on McAfee Blogs.
This post was first first published on McAfee Enterprise – McAfee Blogs’s website by Thyaga Vasudevan. You can view it by clicking here


