Improving Cybersecurity Practices by Managing the Asset Lifecycle
Securing enterprise environments continues to increase in importance. Attacks on infrastructure continue to increase and organizations need to focus more on prevention. While new vulnerabilities are continually being discovered, companies are also left vulnerable to attacks because their infrastructure (hardware, operating systems, and software) is not kept up to date and often includes old, unsupported versions of software, operating systems (OS) and hardware. These end-of-service components can significantly increase security risks (and can also have financial implications). Identifying and updating them will reduce the attack surface.
This is why Qualys enriches asset inventory with product lifecycle information as part of its cybersecurity solution.
Since software and hardware ages over time, these components require maintenance and need to be upgraded or replaced with newer versions. As a result, understanding the service lifecycle of these assets plays an important role in general management of IT assets and in Cybersecurity Asset Management.
Unfortunately, software and hardware manufacturers do not follow any standard practices to inform IT about the service lifecycle of the products they provide. Some manufacturers don’t publish any information; others are inconsistent. We also see and hear different terms used to describe different lifecycle stages. The key challenge, therefore, is how to match the available information to your inventory in a consistent way.
The Product Lifecycle
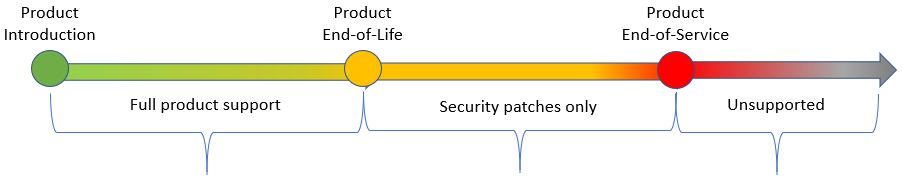
Overall, the product lifecycle can be visualized like this:
Here is what this means to you:
End-of-Sale, End-of-Marketing (EOM) describe when a company stops selling a product. It is no longer being promoted (marketed), but typically it is still fully supported. End of sale/End-of-marketing is more common for hardware since device models are changed on a regular basis. Software End-of-Sale typically happens automatically when the “next” release becomes available and the ability to use newer versions is managed with product use rights (in the majority of cases, if you are paying software maintenance you can upgrade your installation). You should consult your software licensing team to ensure you have upgrade rights.
End-of-Life (EOL) is when publishers stop delivering updates to software and operating systems, except for security fixes. End-of-Life also typically ends standard support and is therefore significant in the software industry. You are still able to get support, but you may need to pay different (usually higher) rates and the benefits you receive will be more limited (e.g. you will no longer get minor enhancements or regular bug fixes). This is the primary signal that it is time to think about an upgrade to a newer version. This phase of hardware lifecycle has similar implications – you will still get security related updates, but no improvements to any firmware. You should also validate you don’t have any regulatory requirements that prevent you from running EOL software.
End-of-Service (EOS) or End of Support is the final lifecycle step. When software (or hardware) reaches End-of-Service, it means it is no longer supported – no security patches or any other support mechanism (some software publishers and hardware manufacturers provide “extended” support, but if you are considering such a contract, you need to ensure you know what this contract entitles you to, since in many cases obtaining any security patches may be difficult). Of course, this doesn’t mean the product stops working – but it does mean you will not get even security patches.
Why Worry About the Asset Lifecycle?
The answer can be best summed up in a simple statement:
“End of Life is the beginning of life for hackers”
This is not just a theoretical statement – there are plenty of examples where unpatched software has resulted in cyber-attacks. WannaCry ransomware attack was very successful affecting Windows XP – in fact, it was so bad that Microsoft issued a security patch for Windows XP, even though it was past End-of-Service. Another example is more recent – China Railway Shenyang trains stopped running for about 20 hours because the company didn’t stop using Adobe Flash. The company had to deploy an emergency update (a pirated version of Adobe Flash!) because they were not aware that Adobe Flash would stop working on January 12, 2021 (Adobe announced this plan in 2017).
But running End-of-Life or End-of-Service software is risky not only from cybersecurity perspective. There are many industry standards that audit for End-of-Life/Service software and hardware. If you are subject to audits for HIPAA (healthcare), PCI (financial) or FedRAMP (US government) compliance, you may fail and/or be subject to penalties if you have EOL or EOS software or hardware in your environment.
Of course, there are also financial costs to consider – with EOL components in your environment, you may be paying premium support fees for minimal service. If your software is End-of-Life, you will get security patches. But if you find any issues/bugs the response you are most likely to get is “we have fixed this bug in a newer version, please upgrade” or “please upgrade and if the issue persists, we will work on it then”. For any End-of-Service software, even custom support agreements are likely to be very limited in what they offer.
In other words, End-of-Life and End-of-Service components will impact you in many areas, including:
- Vulnerability exposure risk
- Regulatory compliance risk
- Financial costs
A Complete Asset Inventory
Qualys CyberSecurity Asset Management (CSAM) provides you with information to help resolve these issues.
Qualys CSAM provides up-to-date, detailed, normalized and categorized asset inventory information, so you can focus on the most critical software and hardware components first. Normalization and categorization are very important, as they provide consistent inventory and help organize assets into useful categories like database software or server computer.
Qualys CSAM also enriches the inventory information with End-of-Life and End-of-Service dates for these assets, so you don’t have to search for this information, and are able to focus on eliminating lifecycle issues. We have added two (2) new dashboard templates: Lifecycle Dashboard Template – Software and Lifecycle Dashboard Template – OS and Hardware to provide you out-of-the-box visibility into lifecycle information. To improve readability of the information they convey, they focus on software separately from OS and hardware assets in each phase of the lifecycle.
Resources
Get Started Now
Get a complete view of your assets from inventory to detection to response – including assets with EOL and EOS hardware, OS and software. See for yourself by registering for a Qualys CyberSecurity Asset Management free trial!
This post was first first published on Qualys Security Blog’ website by Daniel Galecki. You can view it by clicking here

