Cyber Cyber, Burning Bright: Can XDR Frame Thy Fearful Asymmetry?
The outcome of an Attacker’s mission may depend entirely upon a single misplaced charge on a single memory chip on a single server, perhaps the difference between a vulnerable and secure setting in a registry key, and the difference between success and failure to gain access to infrastructure, information, and identities (I3) to subsequently wreak havoc, disable critical operations or infrastructure, and put lives at risk.

The security industry is engulfed in the most asymmetric cyberwarfare we have ever seen.
This ridiculously uneven war between Attacker and Defender has been a well-known challenge in cybersecurity for some time, and a few fear-inducing statistics always find their way into the first few slides of PowerPoint presentations. However, this asymmetric dynamic remains perhaps the single most fundamental truth that should guide us to innovate and to design solutions to give our Defenders better outcomes every day. From this lens, first, we must discuss how to shape and prioritize the protection, detection, and response capabilities with which we will arm Defenders.
The outcome of a Defender’s day depends entirely upon how well they secure trillions of charges across chips, computers, containers, clouds, and even cars against potentially thousands of simultaneous Attackers running millions of attacks, each scouring the Defender’s kingdom for the crown jewels of control and information.
A. Better incident response (IR) programs and better IR training will not solve this problem. Best practices and tool upgrades will win a few battles for the Defender. Still, research suggests a full investment in SOAR and other automation tools will at most reduce costs by roughly 60% for leaders over laggards, all while the cost of breaches continues to rise across all organizations. Investment in IR programs is unquestionably justified from a financial perspective, but that investment is equivalent to sharpening our spears around the campfire while waiting for the tigers to pounce in the long view of the asymmetric war.
Tyger, ‘Tis But a Flesh Wound: The Defender’s Déjà Vu
We must face some harsh and humbling truths that history has taught us about our asymmetric war:
So, do we accept our fate and ultimate defeat of the Defender at the hands of the Attackers? Or is there a Mars Shot initiative that could dwarf anything we have accomplished in the past, bringing symmetry to the war and erasing millions of person-years of Attacker experience and superiority in a flash? And what the heck does this have to do with eXtended Detection and Response (XDR)?
B. Continued entrepreneurship and innovation in novel but transient security controls and frameworks will not solve this problem. Simson Garfinkel, currently Senior Data Scientist at the U.S. Department of Homeland Security, spoke of “The Cybersecurity Mess” and how “cybersecurity is a wicked problem that can’t be solved” almost a decade ago, which was arguably a much simpler and more manageable time for Defenders. Gartner’s Hype Cycle is an excellent value-lifecycle tracker for categories of inventions, and few categories have a faster ride on the Hype Cycle rollercoaster than cybersecurity. At best, security controls rapidly transition from revolutionary standalone products to line-item features on a data sheet as Attackers adapt to and overcome their main value proposition. Perhaps the next ten tigers are caught in camouflaged traps, but we soon notice that they have adapted to avoid them and even set their own.
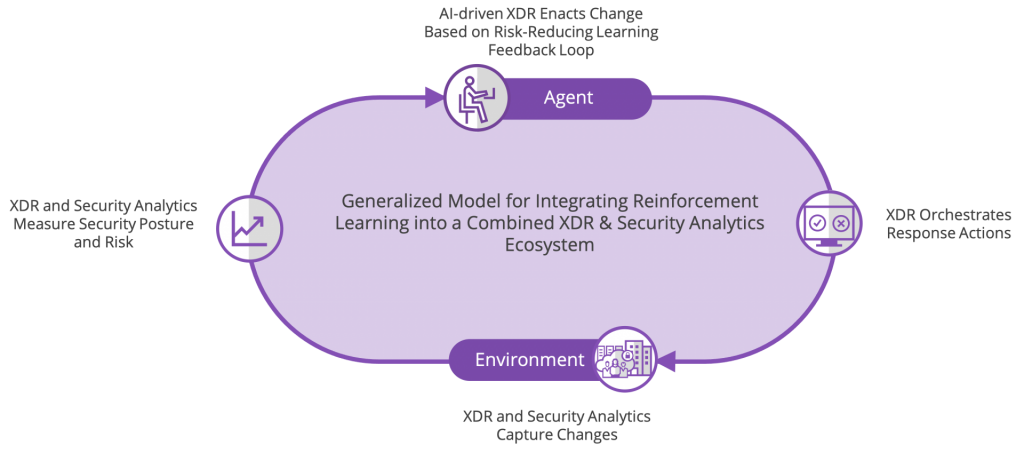
We have the same massively disruptive opportunity to give hope to the Defender by looking to embed self-learning automated AI systems into our prevention, detection, and response controls, as outlined by the MIT Technology Review discussing security uses for AIOps. Less a point on the Gartner Hype Cycle, and more an entirely new dimension of innovation, this cybersecurity AI system, like all AI systems, requires two major components to feed its hunger to learn: (a) large amounts of data related to the inputs and outputs of the I3 systems across the attack surface, and (b) reliable feedback mechanisms and workflows to train the algorithms. The precursors of these needs map readily to (a) the well-established SIEM and Security Analytics markets and (b) the newer EDR and emerging XDR markets.
Go and The Great Equalizer: Cybersecurity and Not-your-everyday AI
Almost 25 years ago, IBM’s Deep Blue overcame 1500 years of cumulative chess knowledge to defeat Garry Kasparov. Five years ago, Google DeepMind’s AlphaGo destroyed over 3000 years of accumulated techniques and strategy to supplant Lee Sedol as the greatest go player ever. Shortly after, Google’s next-gen AlphaZero rendered its own AlphaGo mentor obsolete, having learned chess and go without any human interaction. It seems unfathomable that human beings will even attempt to win these titles back, and we have deep reinforcement learning (Deep RL) to thank.
EDR and Security Analytics: The Starter Fluid for This Promethean Fire
Allie Mellen, an analyst with Forrester Research who covers SecOps, has already written an excellent research report succinctly describing key strengths and weaknesses of these markets and the dynamics likely to unfold in the near term:
Source: Sutton, R.S., Barto, A.G. (2015). Reinforcement Learning: An Introduction, pp. 54.
B. EDR and EDR platforms are the natural evolutionary precursors to XDR, given that endpoints have become pivotal nodes in attack chains.
A. A convergence of critical technologies and capabilities from the SIEM, SOAR, and XDR markets is inevitable; and,
There also exists a more foreboding reason to invest in XDR as a precursor to DeepSecOps. Tomorrow’s Attacker is honing their craft today: They will casually launch thousands of containers across a hybrid multi-cloud infrastructure designed to morph into multiple target infrastructure profiles with various off-the-shelf security controls already in place, and then unleash thousands of simulated attacks while their own Deep RL engine watches and measures its success.
EDR technology on computers, notebooks, and phones has proven to give us the most detailed and robust knowledge about end-user behavior and risk. EDR provides a natural data-rich progression to XDR on the Gartner 2020 Hype Cycle for Endpoint Security as the “next tech up” to provide meaningful and prescriptive training feedback to emerging AI platforms (e.g., IR Analyst A carried out Steps X, Y, and Z across Controls 1, 2 and 3 to negate Threat A). Through research such as Google’s multi-task machine learning exercise and Zhamak Dehghani’s groundbreaking rethinking of data architectures, we have also come to understand that future I3 datasets for AI consumption will likely reside in globally distributed data meshes and not monstrous and monolithic data lakes. The evolution from SIEM to Security Analytics and from EDR to XDR offer the preliminary steps to bring us to a fully integrated “DeepSecOps” platform that has the potential to turn the Attacker-Defender asymmetry on its head. For this blog, let’s define DeepSecOps as a platform or system that seamlessly and automatically integrates the components and processes described in the diagram above (and potentially more), with self-fueled learning and effective automated response as the fundamental goals.
- Prioritize working with a security vendor who has a strong foundation in EDR that will inform them as to the best approach to XDR and AI/ML guidance,
- Ensure that your security vendor has experience providing Security Analytics solutions that integrate into their portfolio and with other vendors and partners to maximize I3 data collection,
- Consider security vendors who prioritize the integration of third-party APIs and components into a shared ecosystem to increase the amount and types of data available to the DeepSecOps system,
- At the same time, ensure that your security vendor supports enough organic security controls on their platform to train AI systems on the best path forward without relying on partners (i.e., a native-capable XDR vendor that still encourages hybridization per Mellen’s article). These technologies could include CASB, DLP, SWG, and more, both as raw data sources and as controls upon which to train outcomes. Ideally, the vendor should have native visibility end-to-end, from end user to cloud, from app user to app coder,
- Ensure your security vendor has a platform, strategy, and roadmap well-suited to delivering a data mesh architecture,
- Look for opportunities to work with vendors who already leverage AI/ML to preemptively reduce attack surfaces and provide guided investigations that indicate early adoption of DeepSecOps principles and architectures.
Make these considerations the tactical precursors to unleashing the DeepSecOps technology that will reframe and contain the Attacker-Defender asymmetry.
To the Defender: Find Allies who are Building Towards that Winnable Future
Defenders should look to cybersecurity partners who offer them a clear path to build the foundation for a DeepSecOps future. What does this look like today? Some key considerations:
What the hand, dare seize the fire?
On what wings dare [they] aspire?
To learn more about what MVISION XDR can do for you watch the video below.
Capture that Promethean Fire with MVISION XDR
Whether you are building a SOC function with limited resources or maturing a well-established SOC, McAfee is here to help you simplify and strengthen your security operations with MVISION XDR. With MVISION XDR, you can proactively identify, investigate and mitigate threat actors targeting your organization before they can gain a foothold in the network. By combining the latest machine-learning techniques with human analysis, XDR connects and amplifies the early warning signals from your sensors at the network, endpoint, and cloud to improve situational awareness, drive better and faster decisions, and elevate your SOC.
* With apologies to William Blake for dragging his brilliant metaphor into the world of cybersecurity and with a nod to that early Wolverine comic.
The post Cyber Cyber, Burning Bright: Can XDR Frame Thy Fearful Asymmetry? appeared first on McAfee Blogs.
This post was first first published on Enterprise – McAfee Blogs’s website by Jamie Cromer. You can view it by clicking here

