WhatsApp Vulnerabilities: Automatically Discover and Remediate Using VMDR for Mobile Devices
WhatsApp has recently fixed critical and high-severity vulnerabilities affecting WhatsApp for Android, WhatsApp Business for Android, WhatsApp for iOS, and WhatsApp Business for iOS. The Indian Computer Emergency Response Team (CERT-In) has issued a high-severity security warning for WhatsApp users in India. It has again confirmed that businesses need a mobile security solution to secure their devices.
Remote Code Execution (RCE) Vulnerability: CVE-2021-24026
WhatsApp released a patch to fix the RCE critical vulnerability (CVE-2021-24026). This vulnerability has a CVSSv3 base score of 9.8 and should be prioritized for patching. It affects assets running:
- WhatsApp for Android prior to v2.21.3
- WhatsApp Business for Android prior to v2.21.3
- WhatsApp for iOS prior to v2.21.32
- WhatsApp Business for iOS prior to v2.21.32
Sensitive Information Disclosure Vulnerability: CVE-2021-24027
WhatsApp released a patch to fix a Sensitive Information Disclosure high vulnerability (CVE-2021-24027). This vulnerability has a CVSSv3 base score of 7.5 and should be prioritized for patching. It affects asset running WhatsApp for Android v2.21.4.18 and WhatsApp Business for Android v2.21.4.18.
The latest vulnerabilities are also affecting WhatsApp Business. If you are using it within your organization then it becomes critical to fix it on priority. According to CERT-In, “Successful exploitation of these vulnerabilities could allow the attacker to execute arbitrary code or access sensitive information on a targeted system.” To minimize the risk, you need to identify the affected assets and then update the application to the right version.
Identification of Assets using VMDR for Mobile Devices
The first step in managing the critical vulnerabilities and reducing risk is to identify the assets. Qualys VMDR for Mobile Devices makes it easy to identify the assets running WhatsApp. To get the comprehensive visibility of the mobile devices, you need to install Qualys Cloud Agent for Android or iOS on all mobile devices. The device onboarding process is easy, and the inventory of mobile devices is free.

Discover WhatsApp Vulnerabilities (CVE-2021-24026) and (CVE-2021-24027)
Once you have the list of assets running WhatsApp, you next want the list of assets with the latest WhatsApp vulnerabilities. VMDR for Mobile Devices automatically detects the new vulnerabilities based on the always updated Knowledgebase.
To see all impacted assets, navigate to the Vulnerability tab, add and run the following QQL in Vulnerability dropdown
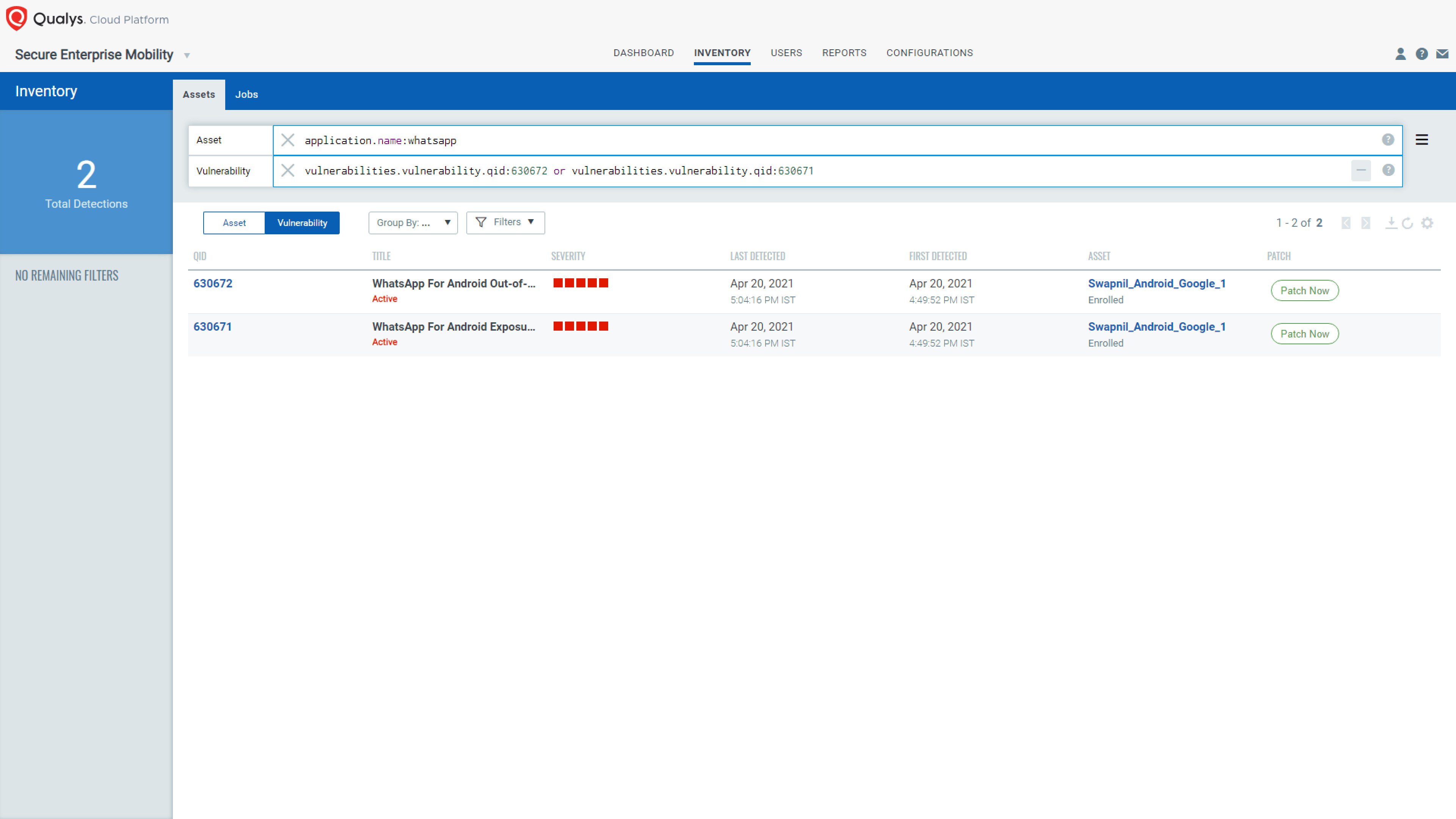
QID 630671 and 630672 is available in signature version SEM VULNSIGS-1.0.0.31, and there is no dependency on any specific Qualys Cloud Agent version.
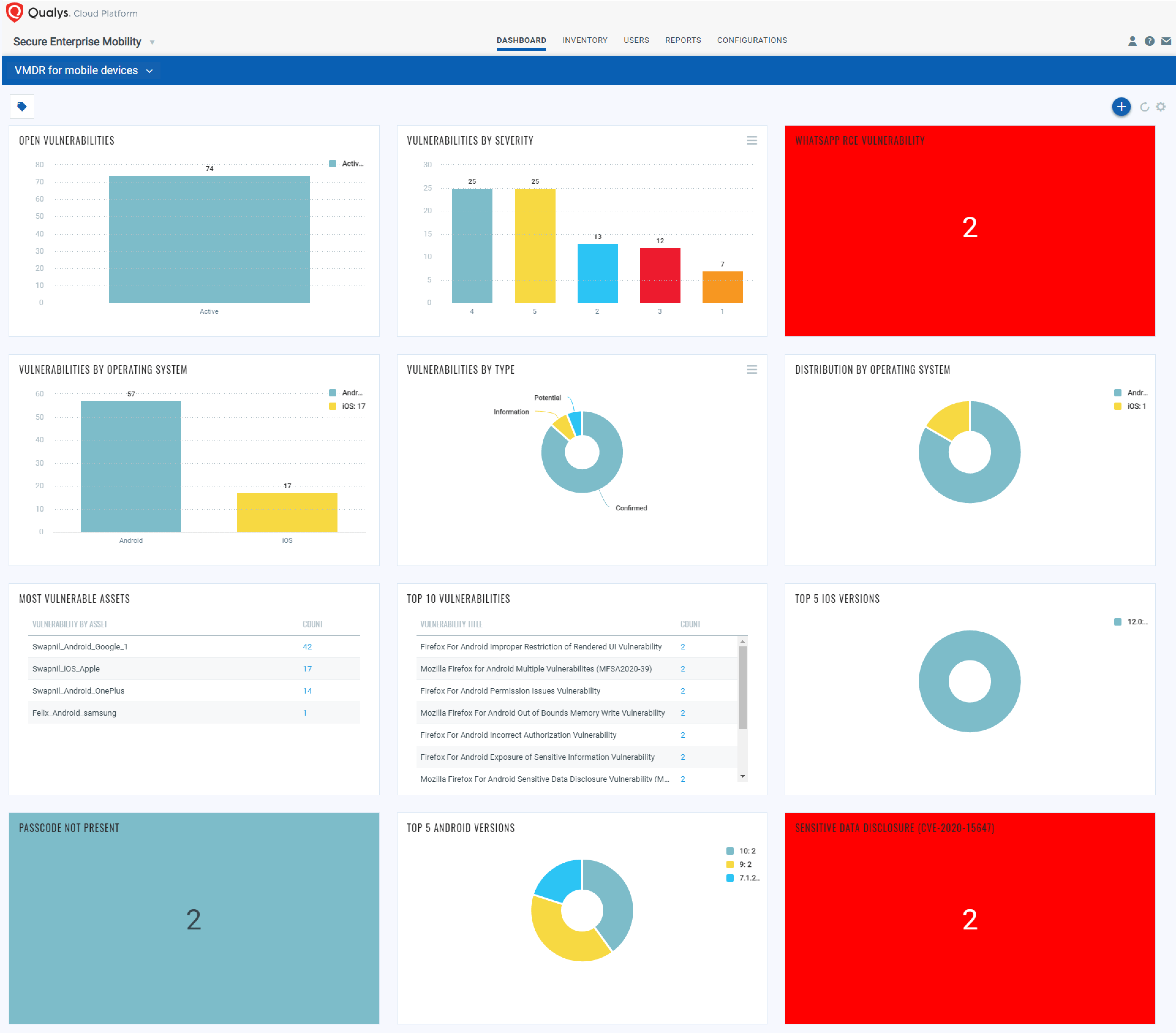
With the VMDR for Mobile Devices dashboard, you can track the status of the assets on which the latest WhatsApp vulnerabilities are detected. The dashboard will be updated with the latest data collected by Qualys Cloud Agent for Android devices.
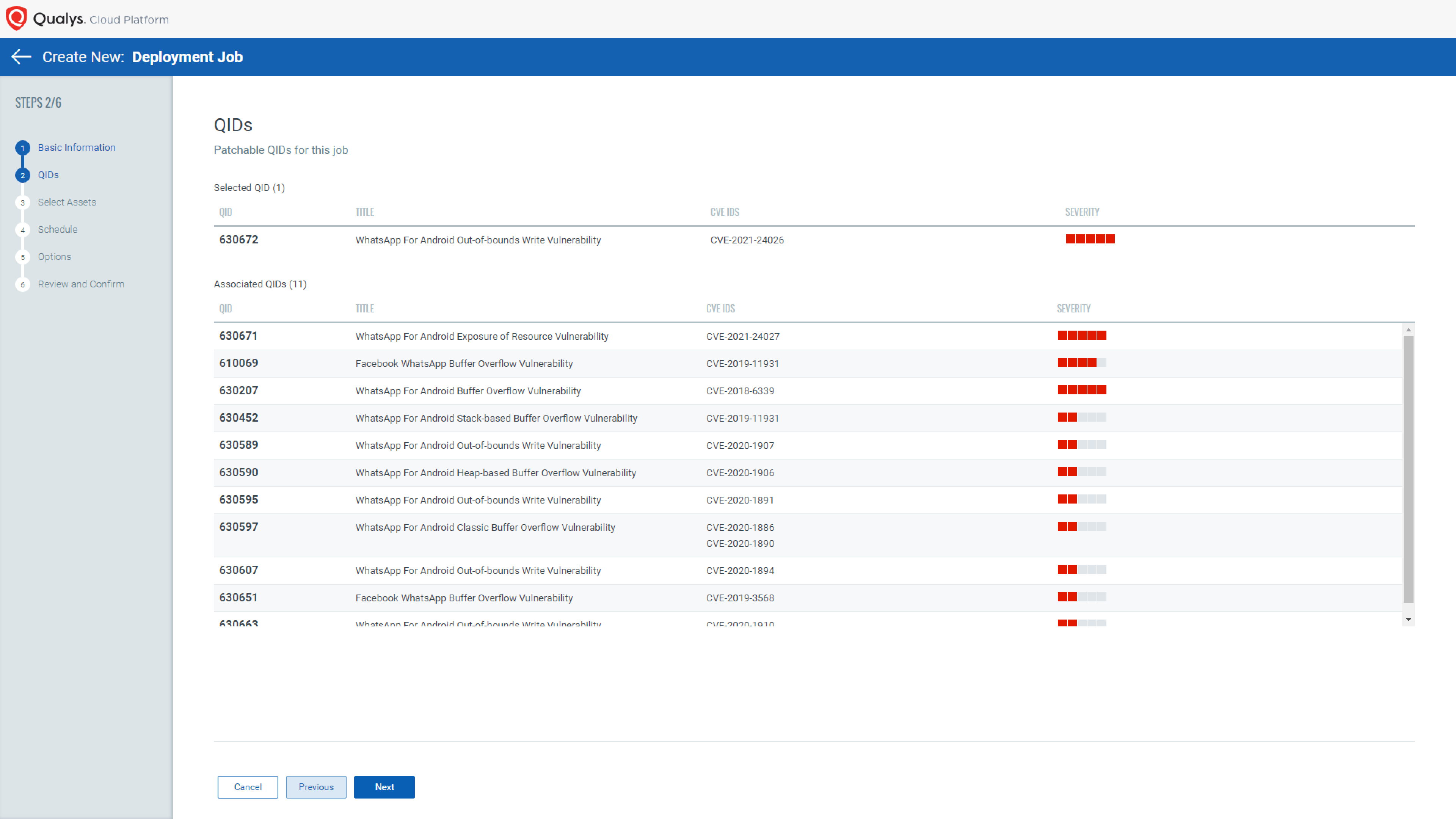
Respond by Patching and Remediation
VMDR for Mobile Devices provides you the patch orchestration for Android devices that helps you rapidly remediate the Android assets. Patch orchestration helps you initiate the most relevant per-application version patches on the affected assets.
You do not have to create multiple jobs; one job will take care of all vulnerabilities of that application.
Users are encouraged to apply patches as soon as possible. For iOS assets, you can perform the “Send Message” action to inform the end user to update WhatsApp to the latest version. Also, you may provide step-by-step details to update WhatsApp from the Apple App Store.
Get Started Now
Qualys VMDR for Mobile Devices is available free for 30 days to help you detect vulnerabilities, monitor critical device settings, and correlate updates with the correct app versions available on Google Play Store. Sign up now for a free 30-day trial of VMDR for Mobile Devices.
This post was first first published on Qualys Security Blog’ website by Swapnil Ahirrao. You can view it by clicking here

