You Must Quarantine! Fake Office 365 Email Leads to Curiosity
The Cofense Phishing Defense Center (PDC) has discovered a recent phishing campaign that has targeted Office 365 users and includes a convincing Microsoft quarantine notification reference. The campaign was found in an environment protected by Microsoft’s own secure email gateway (SEG).
By Kian Mahdavi, Cofense Phishing Defense Center
Threat actors continue to leverage standard Microsoft notifications to entice the recipient into interacting with the email. We noticed two variants of this campaign.
The example in question also illustrates a move away from the traditional narrative used to lure recipients. This attacker has opted out of using urgency language with terms such as “urgent” or “you must.” As a result, the reader may overlook the threat and become curious enough to engage with the email, opting to review the “important message.”
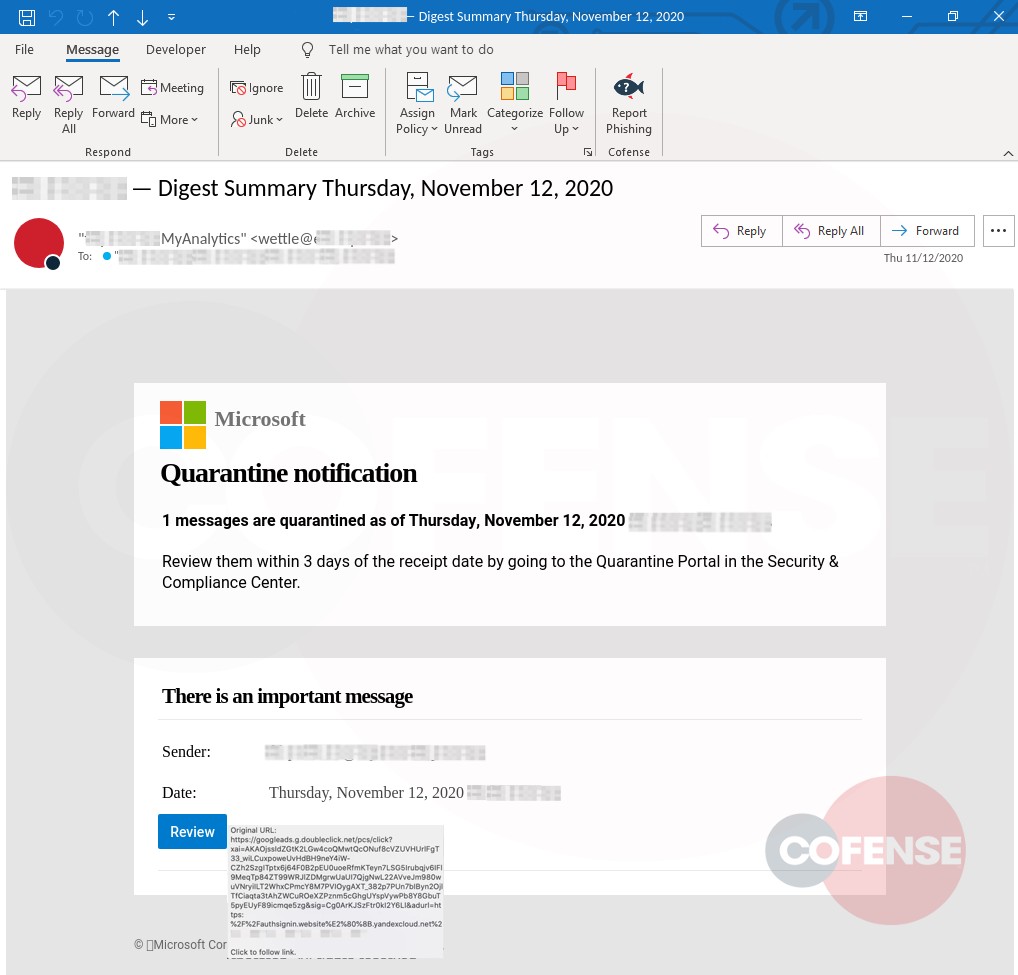
The first example displayed above in Figure 1 showcases a fairly persuasive “Digest Summary Notification.” It displays the same HTML used within the legitimate notifications sent. However, if we look past the display name and dive a little deeper into the actual “from” address, we can see that it belongs to a compromised account belonging to an environmental firm: wettle@redacted [.]com. We can only assume the attacker was hoping the reader wouldn’t notice the domain has no relation to Microsoft.
Should the user hover over the “Review” option, the URL path will clearly display the redirect that has no relation to Office or Microsoft. It will instead direct the user to “googleads,” taking them immediately to the phishing landing page. We can assume the reason for this is to evade detection and bypass existing security measures with whitelisted URLs.
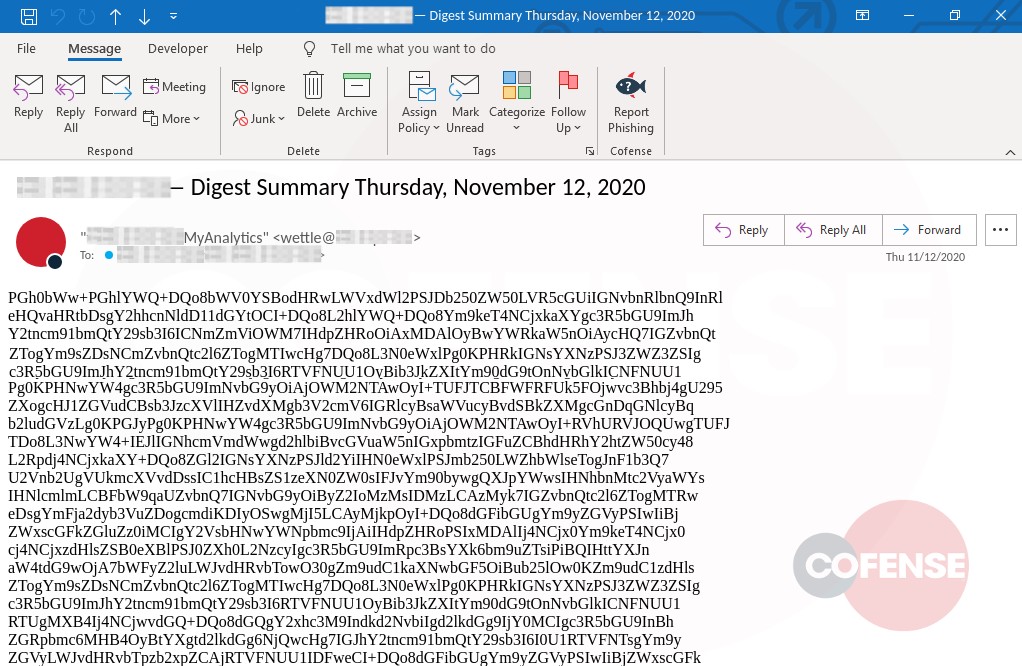
The second campaign is a little more unusual at first glance as the entire email body has been encoded. The attacker may have done this to evade existing security controls, assuming that, once the email was opened, it would decode to reveal the email message in plain text. The email message did not decode, revealing a rather confusing layout and raising red flags immediately. This may have been caused by a bug in the threat actor’s toolkit. We later decoded the text to reveal several links of which most were benign, to which we narrowed down the malicious link through trial and error that led to the matching phishing landing page below:
Figure 2 – Encoded body of email
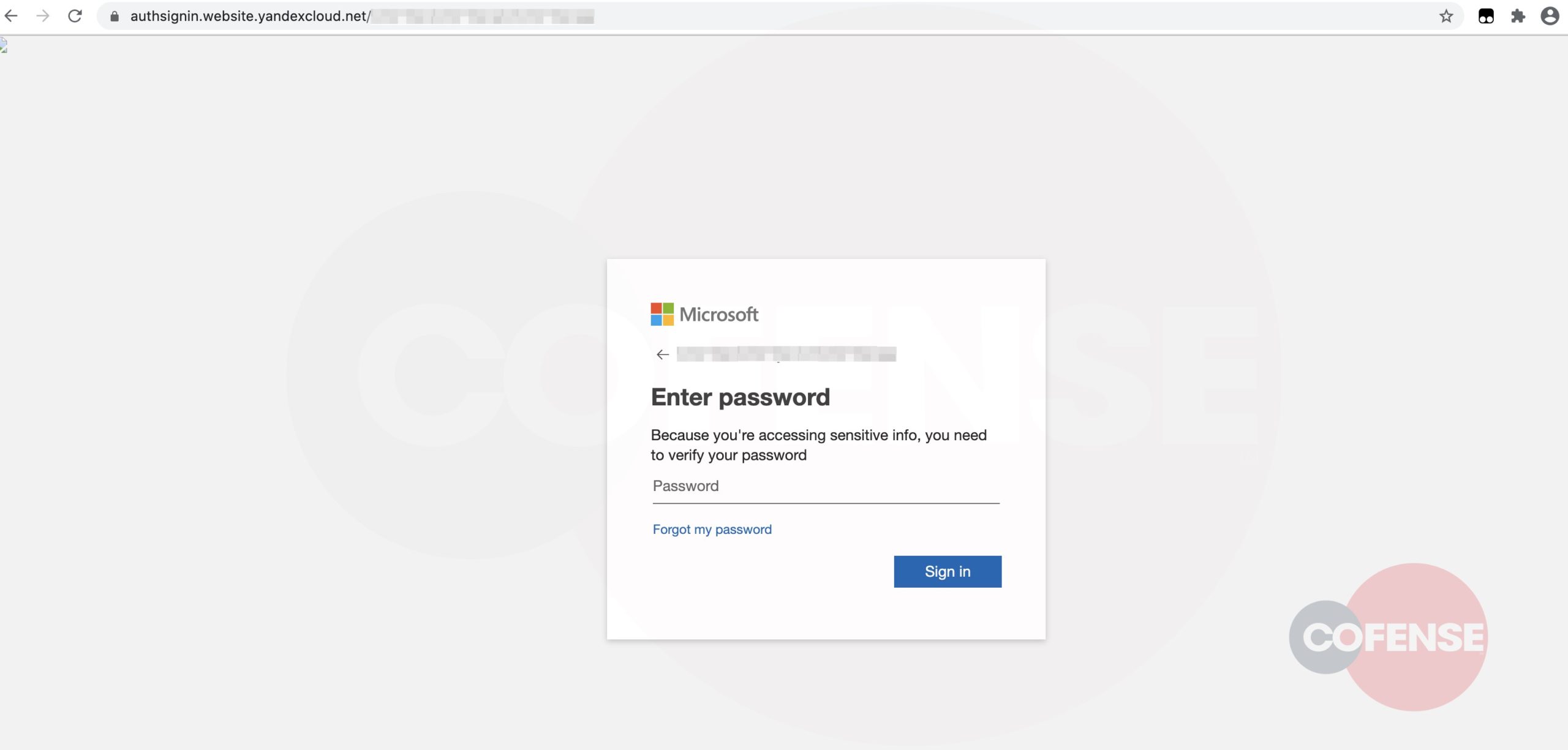
hXXps://authsignin[.]website[.]yandexcloud[.]net/
Attackers are always exploring new sophisticated tools and techniques, as demonstrated in the above examples, to bypass the SEG. Cofense PDC uses human detection and auto response to remediate and quarantine such threats, and continues to evolve to stay ahead of the latest phishing and malware threats.
As seen above in Figure 3, the phishing landing page has been carefully designed to replicate the official Office 365 login page, luring users into thinking they are authenticating via a genuine service. Assuming users logged in with their true Microsoft credentials, their personal data could unfortunately be in the hands of the threat actor.
Indicators of Compromise
119[.]28[.]148[.]150
| Network IOC | IP |
| hXXps://googleads[.]g[.]doubleclick[.]net/pcs/click?xai=AKAOjssIdZGtK2LGw4coQMwtQcONuf8cVZUVHUrlFgT33_wiLCuxpoweUvHdBH9neY4iW-CZh2SzgITptx6j64F0B2pEU0uoeRfmKTeyn7LSG5Irubqjv6IFl9MeqTp84ZT99WRJlZDMgrwUaUI7QjgNwL22AVveJm980wuVNryiILT2WhxCPmcY8M7PVIOygAXT_382p7PUn7bIByn2OjlTfCiaqta3tAhZWCuROeXZPznm5cGhgUYspVywPb8Y8GbuT5pyEUyF89icmqe5zg&sig=Cg0ArKJSzFtr0kI2Y6Ll&adurl=https:%2F%2Fauthsignin.website%E2%80%8B.yandexcloud.net%23 | 172[.]217[.]7[.]226 |
| hXXps://authsignin[.]website[.]yandexcloud[.]net/ | 213[.]180[.]193[.]247 |
| hXXps://auth-1304164361[.]cos[.]ap-seoul[.]myqcloud[.]com/index.html | 119[.]28[.]148[.]128
119[.]28[.]148[.]172 |
| hXXps://authsignin[.]website[.]yandexcloud[.]net/ | 213[.]180[.]193[.]247 |
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.
This post was first first published on Cofense’s website by Cofense. You can view it by clicking here

