Emotet is Back for the Holidays with Updated Tactics
After a lull of nearly two months, the Emotet botnet has returned with updated payloads. The changes are likely meant to help Emotet avoid detection both by victims and network defenders. Apart from these updates, the campaigns’ targeting, tactics and secondary payloads remain consistent with previous active periods. Cofense Intelligence™ released a flash alert on the newest Emotet activity to customers with details about its new features.
By Brad Haas
Emotet Background and 2020 Activity
The Emotet botnet is one of the most prolific senders of malicious emails when it is active, but it regularly goes dormant for weeks or months at a time. This year, one such hiatus lasted from February through mid-July, the longest break we’ve seen in the last few years. Since then, we observed regular Emotet activity through the end of October, but nothing from that point until today.
Emotet has a few primary functions. It acts as an information stealer, harvesting credentials, contact lists and email content from an infected machine. It adds the contacts to its target list, and builds and sends authentic-looking emails using the stolen email content. Finally, it can deliver other malware as a secondary payload, often leading to separate attacks such as ransomware. In October the most common secondary payloads were TrickBot, Qakbot and ZLoader; today we observed TrickBot.
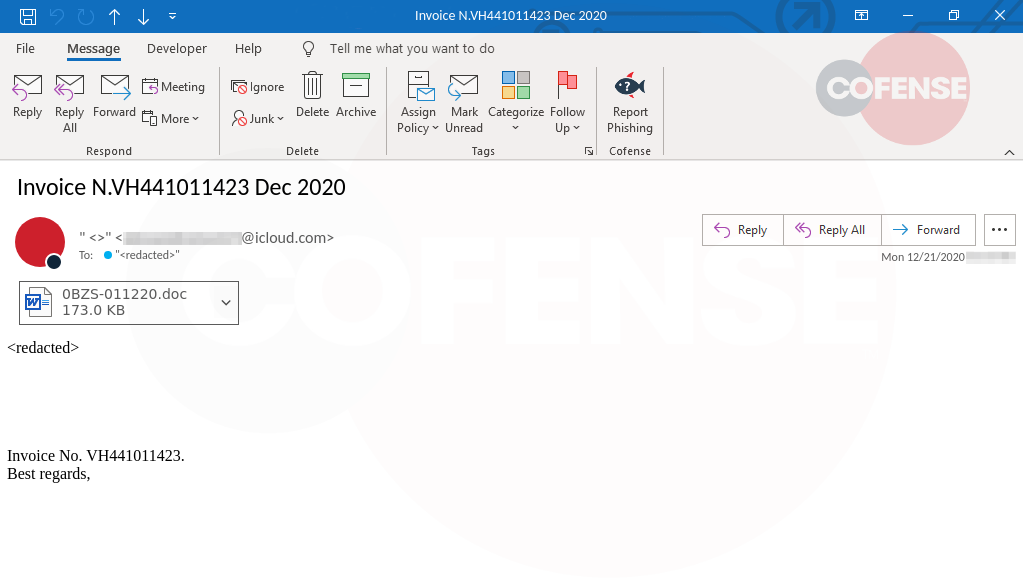
Figure 1: This is an invoice-themed Emotet email with a malicious document attached.
Updates Make Infection Less Obvious
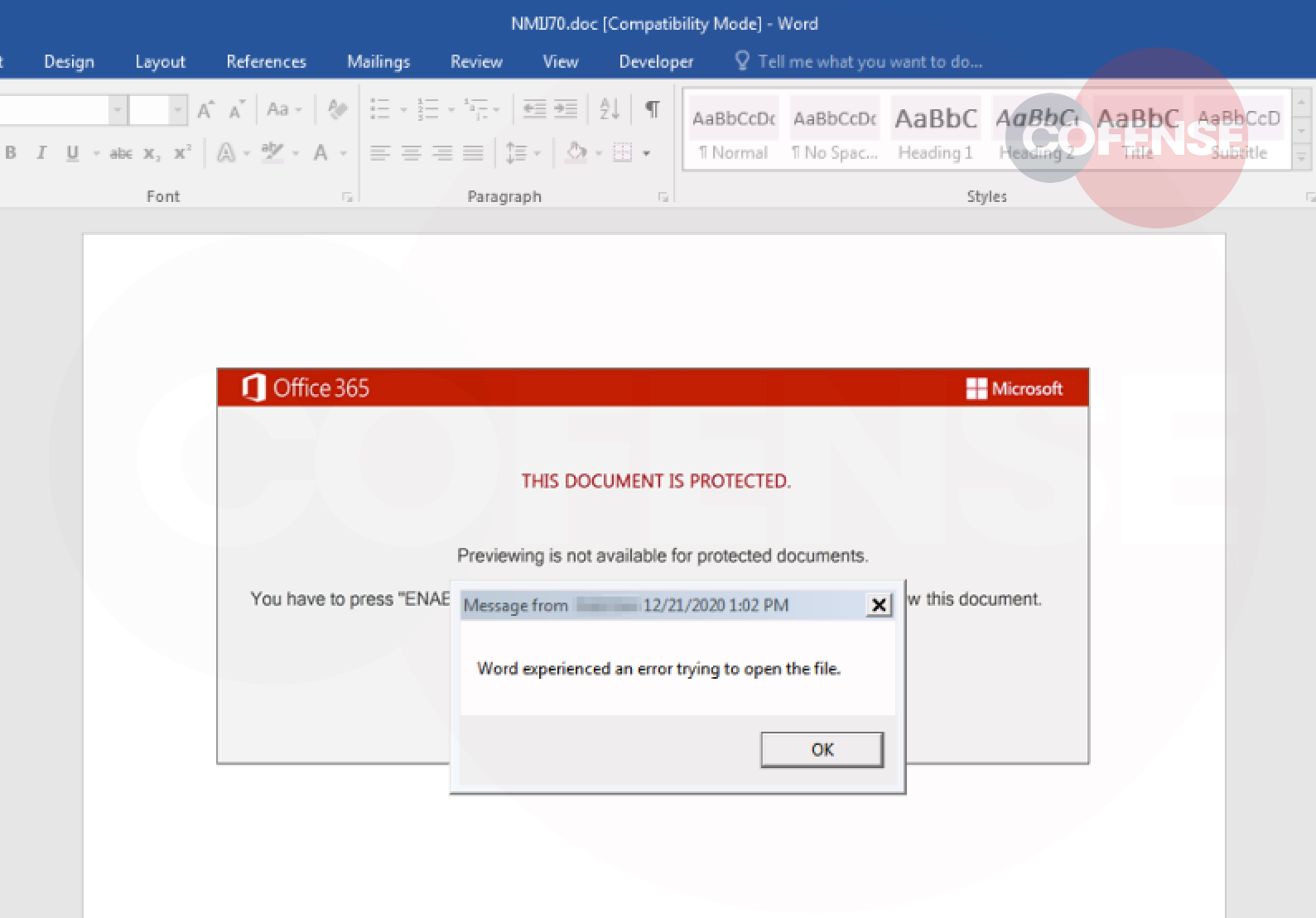
The new Emotet maldoc includes a noticeable change, likely meant to keep victims from noticing they’ve just been infected. The document still contains malicious macro code to install Emotet, and still claims to be a “protected” document that requires users to enable macros in order to open it. The old version would not give any visible response after macros were enabled, which may make the victim suspicious. The new version creates a dialog box saying that “Word experienced an error trying to open the file.” This gives the user an explanation why they don’t see the expected content, and makes it more likely that they will ignore the entire incident while Emotet runs in the background.
Emotet targets a wide variety of users spanning dozens of countries and many languages. Email themes are also varied–some are created from victims’ stolen data, while others use generic templates, which can be adapted to current topics. For example, today’s campaigns include some emails using a holiday theme. Each email uses one of a few different delivery mechanisms: embedded links, attached documents, or attached password-protected zip files. All techniques attempt to deliver a malicious Microsoft Office document (maldoc).
Figure 2: A fake error message is created when macros are run in a new Emotet maldoc.
Conclusion
Emotet’s active periods have been unpredictable, and its authors have made an effort to adapt both the email campaigns and the malware to spread more effectively. Cofense Intelligence customers have received relevant IOCs and Active Threat Reports (ATRs) as these campaigns are identified and analyzed. Customers can access the most up to date list of all relevant Cofense Intelligence IOCs and ATRs tied to Emotet via our API and on ThreatHQ.
The Emotet malware itself, which is installed if a user does run the malicious macros, also had a few updates. The malware was previously a standalone executable file with a “.exe” filename, but is now a DLL file initialized using the built-in Windows program rundll32.exe. This makes the presence of the malware a little more difficult to detect. Emotet’s command-and-control (C2) communication has also been changed to use binary data rather than plain text, which will likely make it more difficult to detect at the network level. Finally, the authors changed the binary to thwart extraction of C2 details and other indicators of compromise (IOCs).
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.
This post was first first published on Cofense’s website by Cofense. You can view it by clicking here

