IDG Study – Protecting the Human Side of Cybersecurity
Employees are Remote, Data is Everywhere
According to a recent survey conducted in May 2020 by IDG of over 100 IT leaders, one major problem is securing the hundreds of apps that their companies have deployed in the cloud. Over half of respondents (52%) listed securing those apps as “very” or “extremely” challenging and only 1% of them thought it wasn’t a challenge at all.
Blocking every non-approved application would certainly help, but it would also impact employee efficiency and undermine some of the advantages of remote work.
According to the survey, remote working presents a number of security challenges. Workers are use multiple devices that need to be secured (50%), tracking and managing cloud assets (41%), and data backup and recovery (40%), which are generally the most common challenges of remote workers from an IT perspective. Shadow IT is also a challenge, with 43% of the respondents listing it as their number one security issue.
Behavioral Analytics May Hold the Key
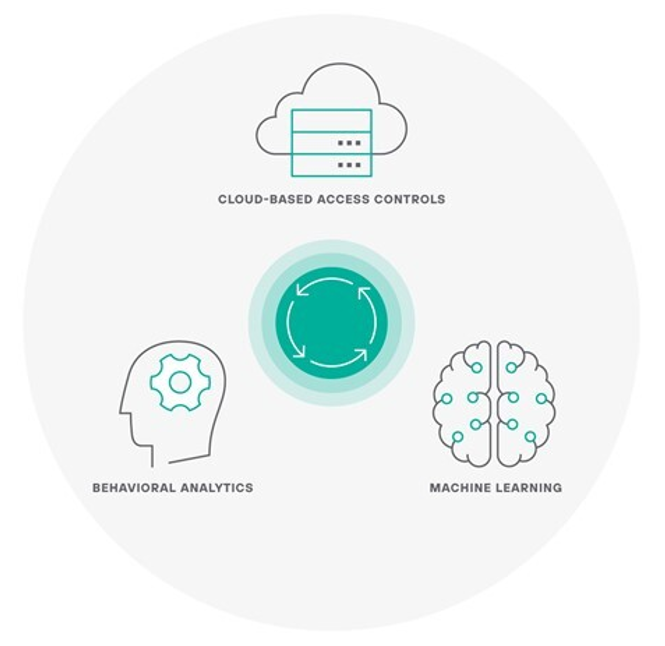
Among the companies reporting the largest number of applications, a majority tend to favor behavioral analytics technology, with 65% either currently deploying it or planning to. Among those that do use it, 46% find it to be the single most useful cloud security technology. They also tend to be less concerned about data loss than other companies.
Behavioral analytics in the cybersecurity realm refers to the use of software tools to detect individual behavior patterns that might be high risk and the alerting IT managers.2In other words, behavioral analytics can shine a light on the human element that plays a role in almost any cybersecurity incident.
When it comes to identifying and closing their security gaps, survey respondents favored these three habits:
3 Ways to Close Security Gaps
To see more findings and learn more about behavioral analytics cybersecurity, download the IDG Market Pulse Study, “Protecting the Human Side of Cybersecurity.”
- Review Processes, Change Passwords, and Audit for Threats: Look for hidden data sources by inspecting the business processes, applications used, and data involved in that particular business process. Encourage frequent password changes and conduct threat audits often.
- Monitoring and tracking: Turn on your cloud security notifications, use intrusion detection systems (IDSs) to spot interlopers and use identity and access management (IAM) to limit and track employee access.
- Technology solutions: Try out different technologies that monitor access and alerts. Use security information and event management (SIEM) solutions to identify and stop breaches, but don’t rely too heavily on it. SIEM fails to give you a full view of user behavior and tends to generate more noise than insight.
The use of cloud-based applications continues to explode. But securing those apps and preventing data loss has presented enterprise companies with a major challenge. The companies that seem to be faring better are the ones using behavioral analytics and focus on the user as the security perimeter, not the infrastructure. It’s still early days for behavioral analytics cybersecurity, but with 59% of companies, according to IDG, planning to use it by 2021, it clearly has a lot of traction.
This post was first first published on Forcepoint website by Jim Fulton. You can view it by clicking here

