Twelve Flavors of Phish: Canadian Workers Targeted With Fake Covid-19 Relief Deposits
Financial aid programs continue to be popular targets in the midst of the COVID-19 pandemic, with government relief grants a particularly great one to exploit.
By Jake Longden and Elmer Hernandez, Cofense Phishing Defense Center
With multiple world governments providing such grants, and millions of people relying on these as their main source of sustenance, adversaries will continue exploiting such dependence.
The Cofense Phishing Defence Center (PDC) has observed a recent phishing campaign in Canada that aims to harvest banking credentials and other personal information from 12 different banking institutions. This was achieved by preying on employees who were expecting COVID-19 relief grants in the form of the CERB (Canada Emergency Response Benefit). These funds are supposedly sent via an electronic transfer from Interac, a legitimate Canadian interbank network.
The CERB scheme gives financial support to employed and self-employed Canadians who have been affected by the COVID- 19 pandemic. It offers $2,000 CAD (approx. $1,490 USD) for a four-week period.
CERB Deposit
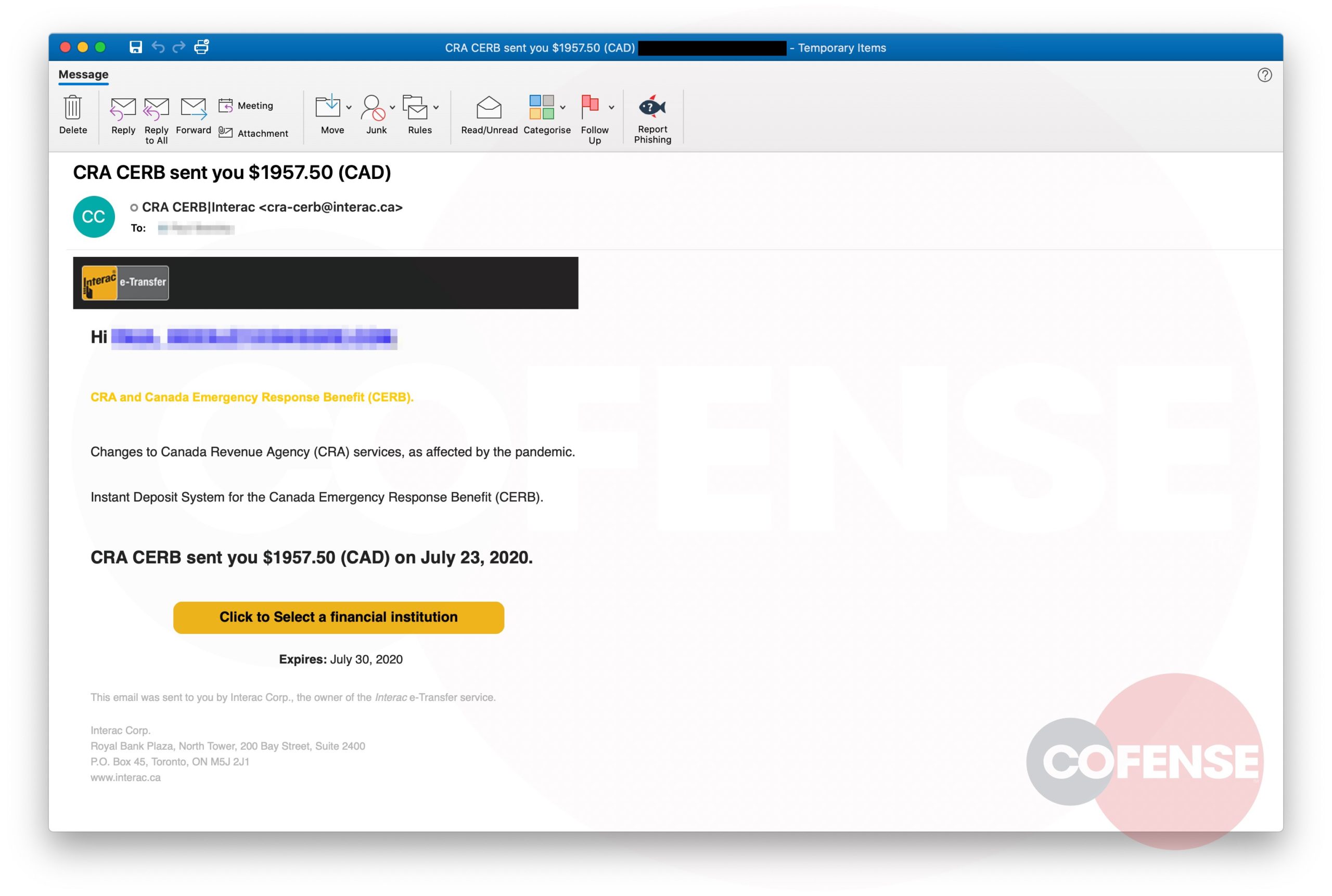
The email purports to be a notification from Interac’s e-transfer service, indicating that the Canada Revenue Agency (CRA) has made a CERB deposit of $1,957.5 CAD (approx. $1,463 USD). A fictitious expiration date is included in an attempt to instill a sense of urgency.
Figure 1 – Email Body
Header
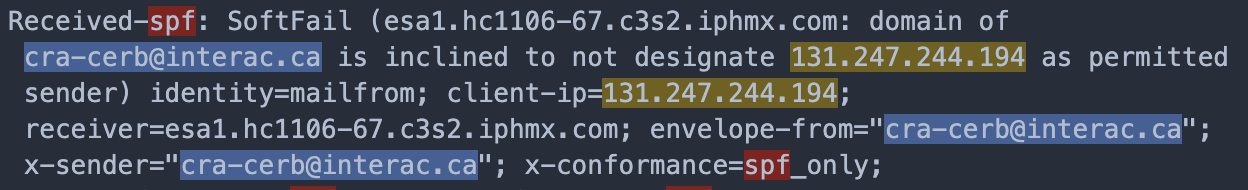
The SPF fail in the headers (Figure 2) indicates that the email is likely spoofed, and the IP address suggests that it came from a potentially compromised device using the University of South Florida network (Figure 3). The choice of the name ‘cra-cerb’ in the address is used to add credibility to the email.
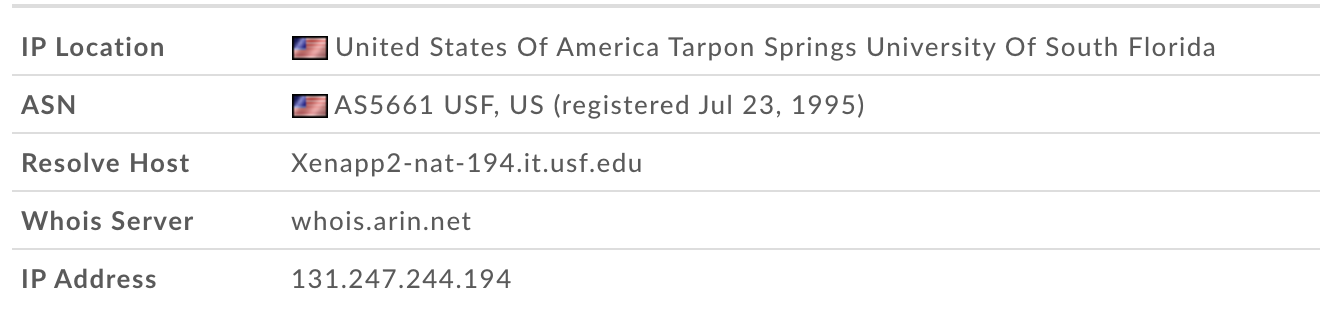
Figure 2 – SPF Fail
A Phish of 12 Different Flavors
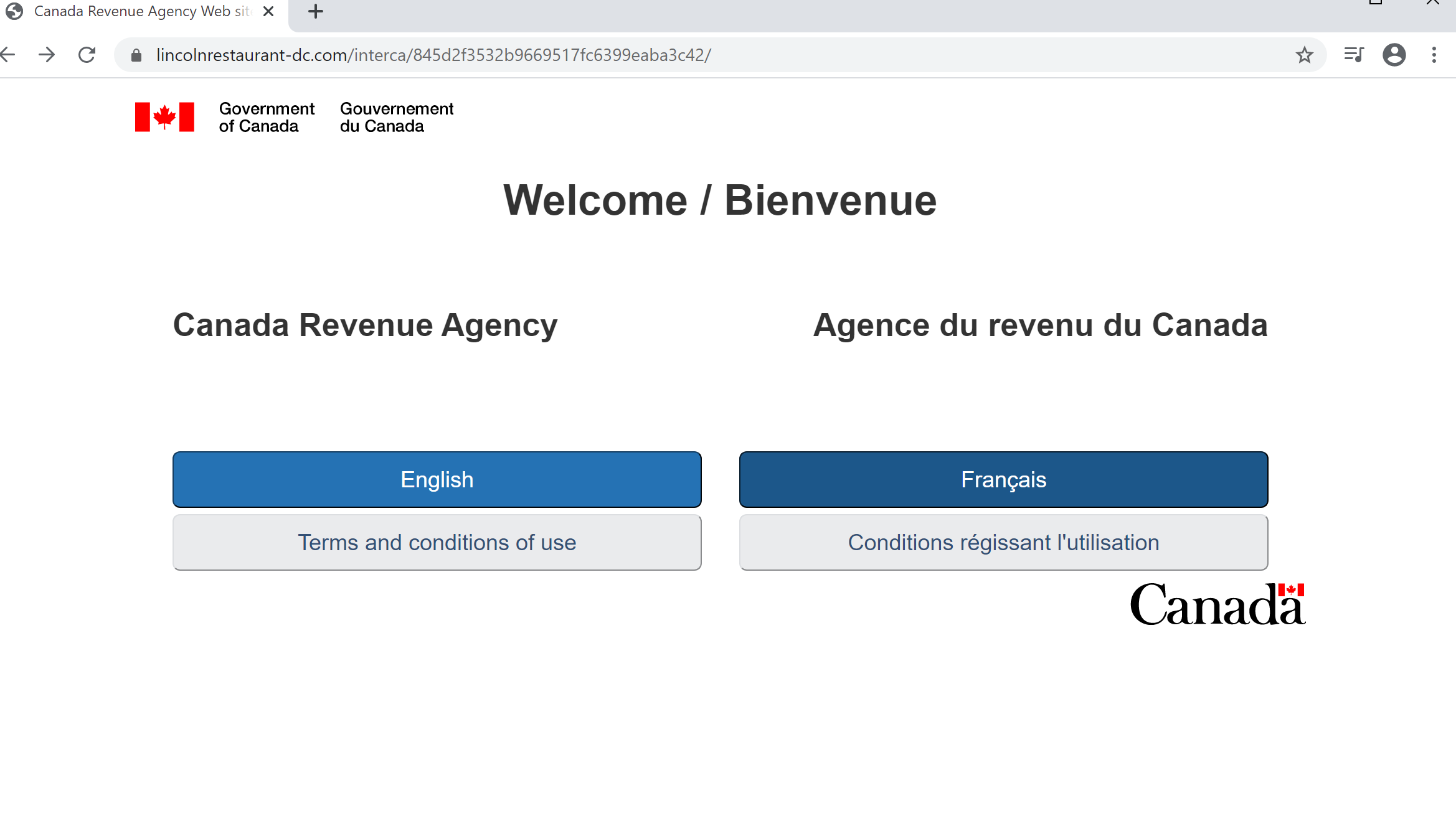
The first landing page the phish visits is an impersonation of the CRA. It has working links in both French and English like a legitimate site from the Canadian government. Once the user has selected their language choice, they will be redirected to an impersonated Interac e-transfer site in said language.
Figure 3 – USF IP Address
Figure 4 – CRA Spoofed Site
- ATB Financial
- Bank of Montreal (BMO)
- Canadian Imperial Bank of Commerce (CIBC)
- Desjardins
- Laurentian Bank
- Meridian
- National Bank of Canada
- Royal Bank of Canada (RBC)
- Scotiabank
- Simplii Financial
- Tangerine
- TD Canada Trust
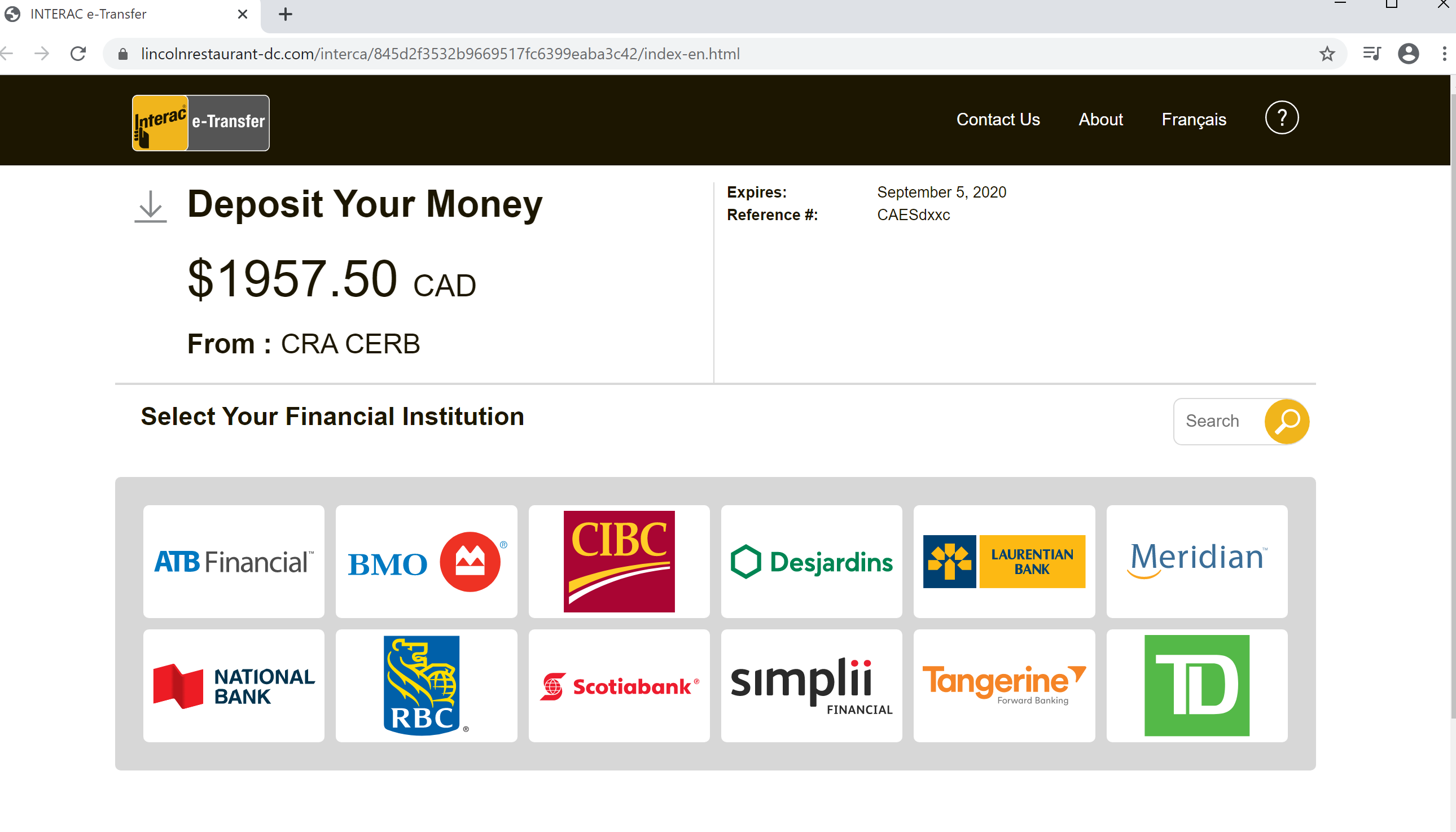
Once in the spoofed Interac e-transfer site (Figure 5), the user must choose their personal bank from twelve different options in order to receive the deposit. All of these banks are actual members of the Interac network, which suggests attention to detail from adversaries:
Next, the recipient is taken through a series of spoofed pages for the corresponding bank, with some offering both English and French versions. All pages reside within a compromised website of a Washington, DC area business. The URL paths vary depending on the bank, but follow the following format:
Figure 5 – Spoofed Interac Page
Although no two options are identical, most of the twelve spoofed banks ask for similar details:
hxxps://lincolnrestaurant-dc[.]com/interca/{unique 32 character string}/bank/{bank name}/{html or php file}
- Usernames
- Card Numbers
- Passwords
- Security Questions and Answers
- Personal Information (PI) (Full Name, Date of Birth, Email, etc)
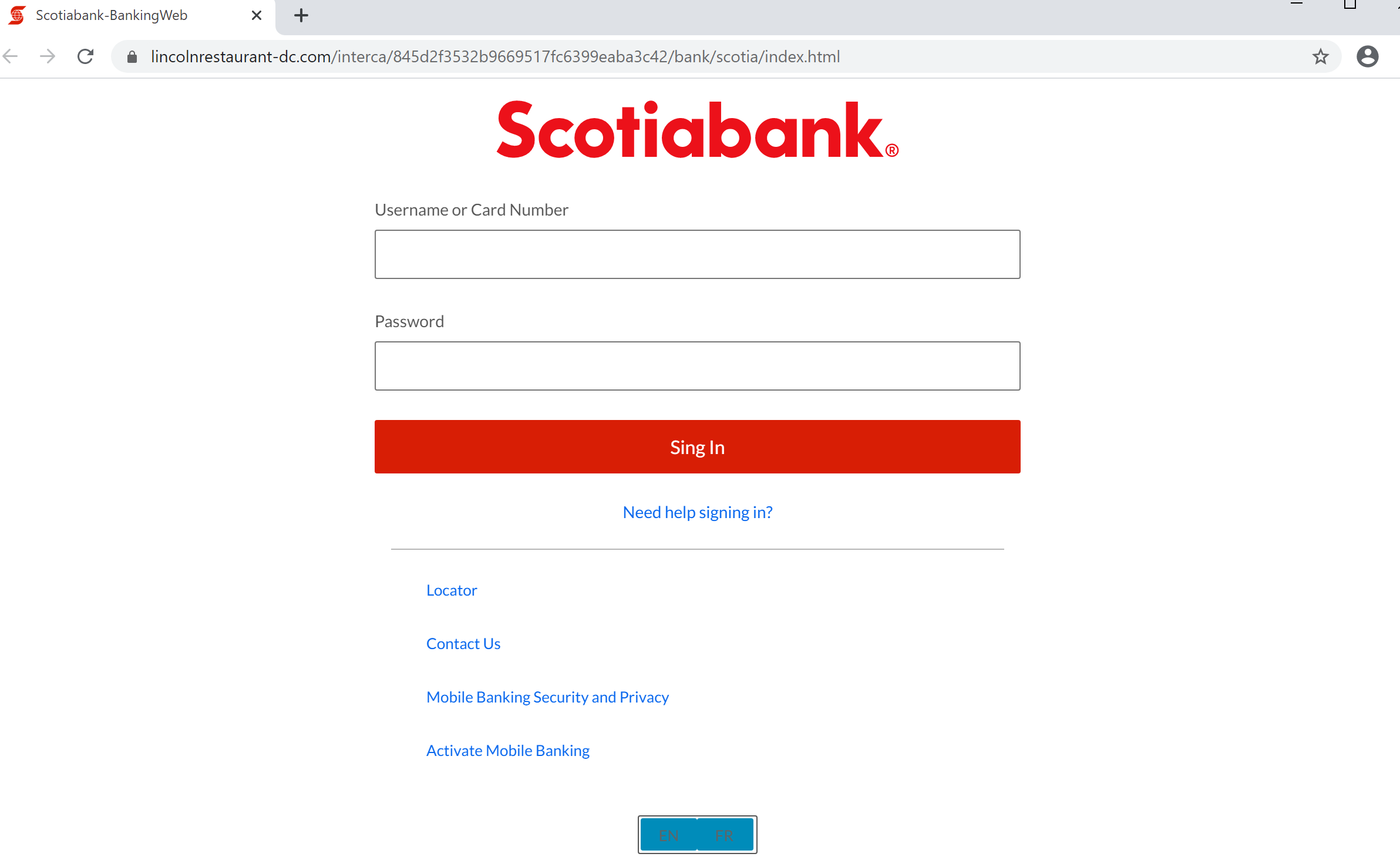
Scotiabank (English) was chosen to showcase an example of the entire phish process. The initial page the user is presented with is a standard login page asking for credentials, notice the slight typo of the word “sign” on the “Sing in” button (Figure 6).
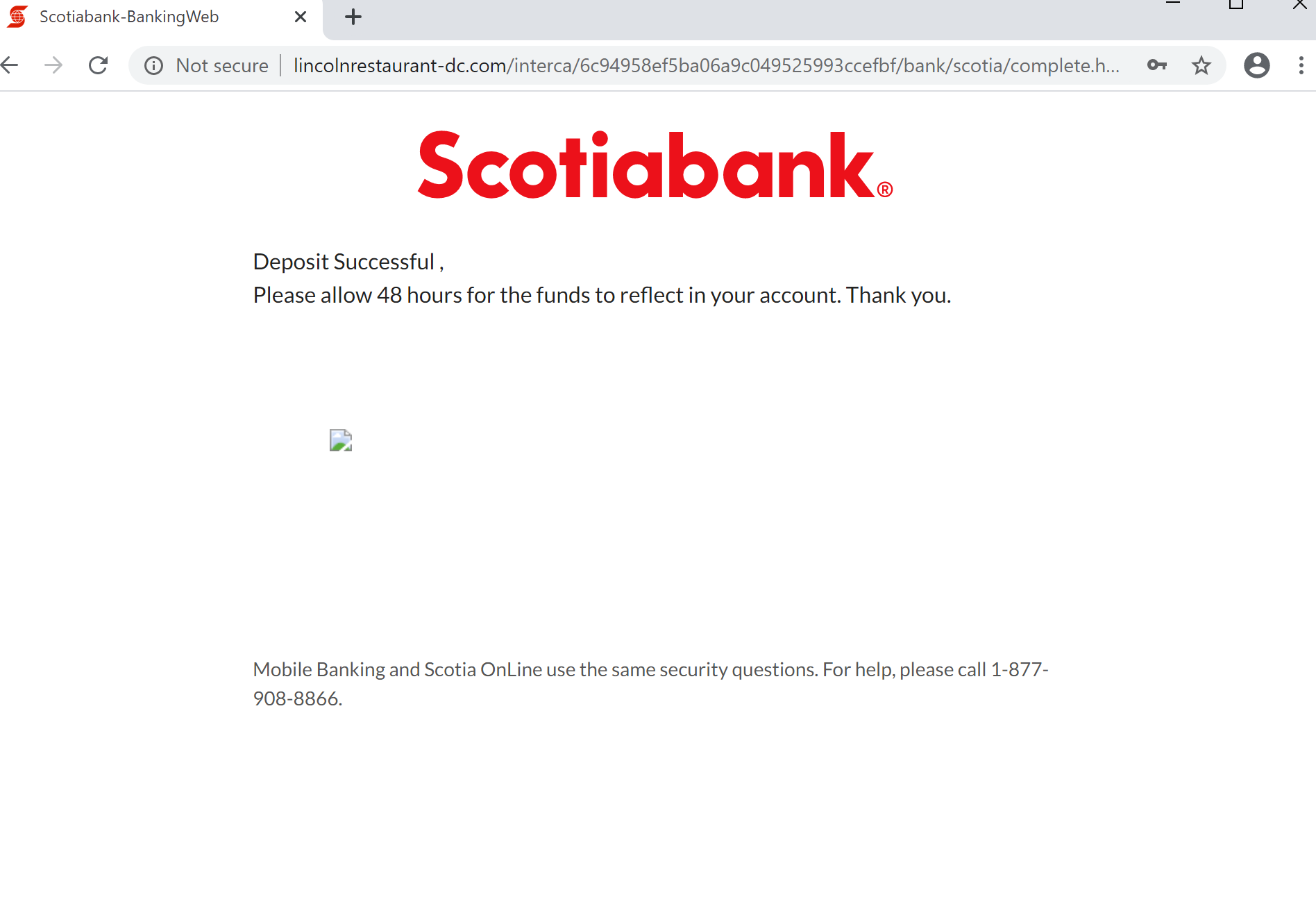
The next page asks for sensitive PI and card information (Figure 7). The user is then asked for Security questions and answers (Figure 8), which might falsely provide the reassurance that some form of multi-factor authentication is being employed. The combination of PI such as a Social Insurance number, credit card numbers and MFA questions could form a fairly solid base for identity theft/impersonation. Once submitted a final page confirms the funds will be deposited in 48 hours (Figure 9).
Figure 6 – Scotiabank Sign in
Figure 7 – Scotia PI and Card Info
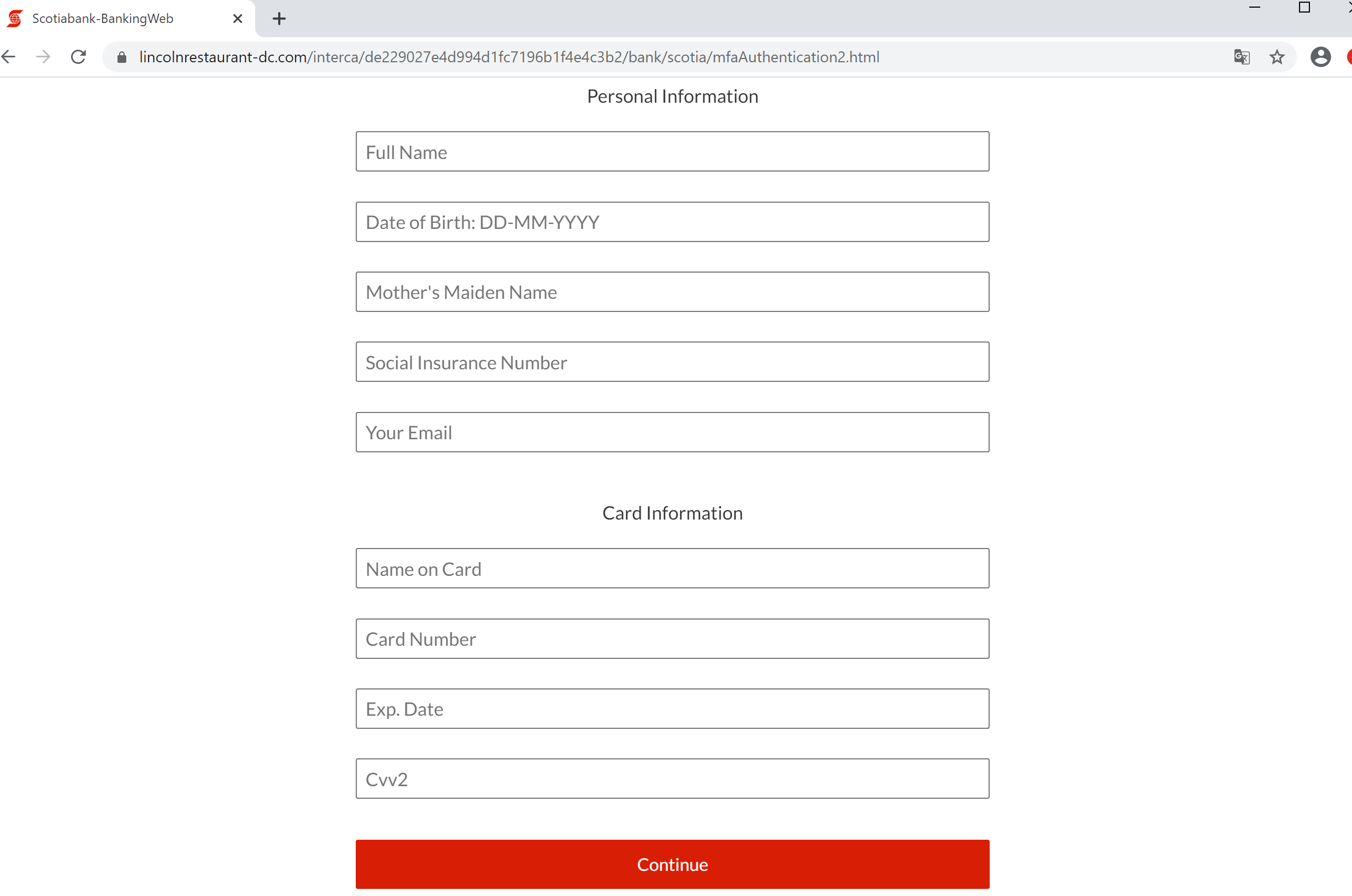
Figure 8 – Scotia MFA Security Questions

Figure 9 – Deposit Successful
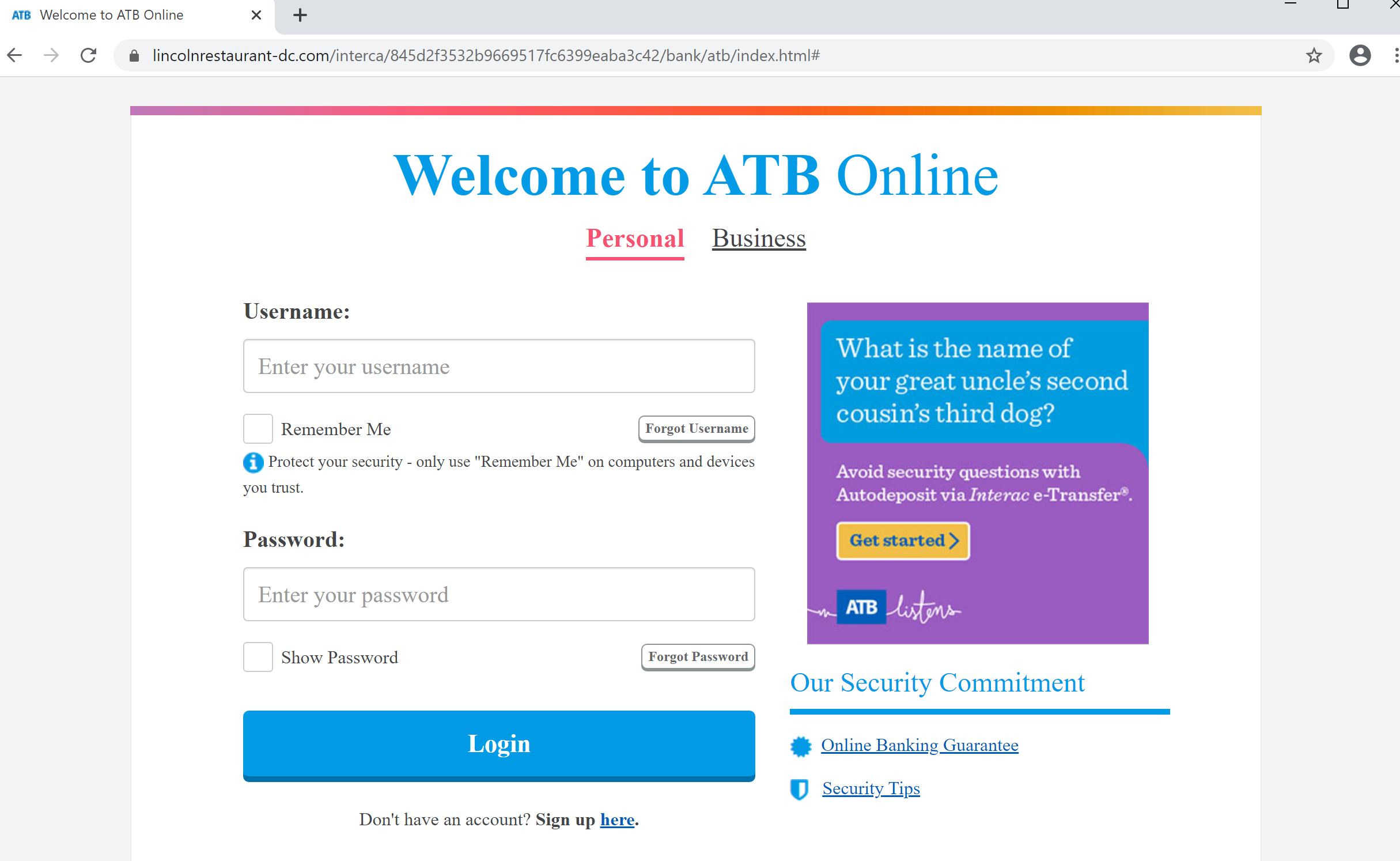
Figures 10 through 20 show the login pages for the remaining eleven spoofed banks.
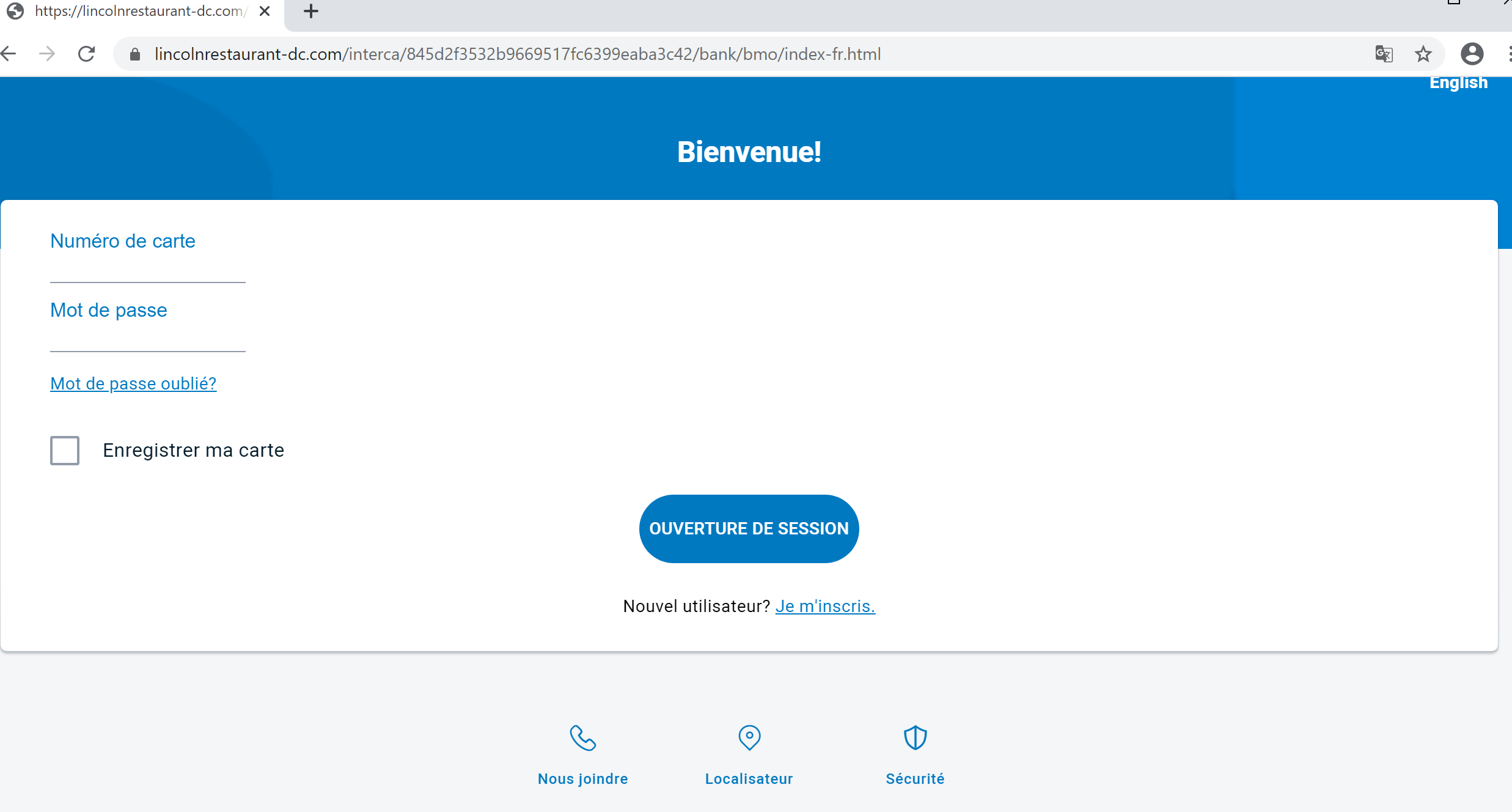
Figure 10 – ATB
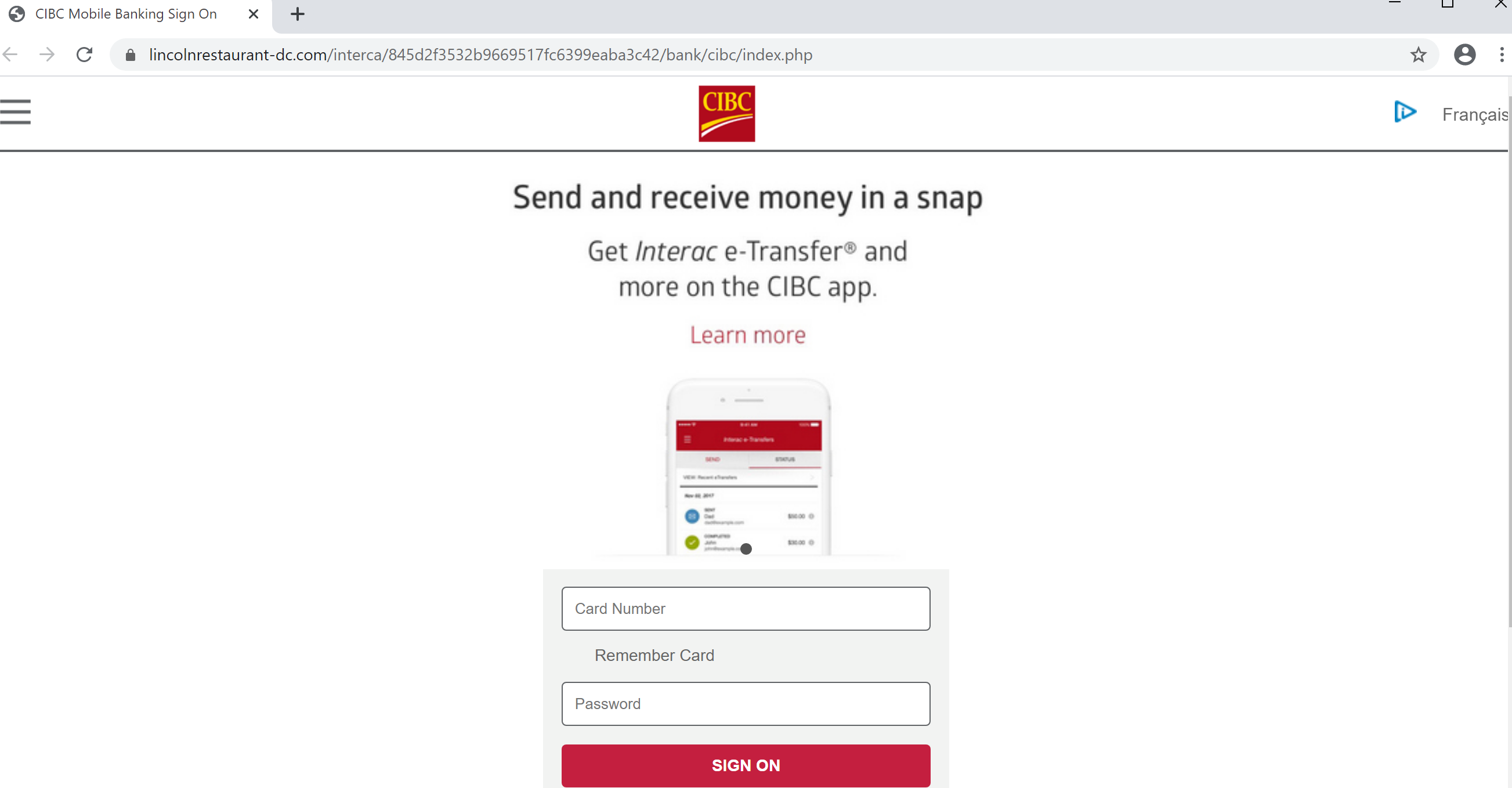
Figure 11 – BMO
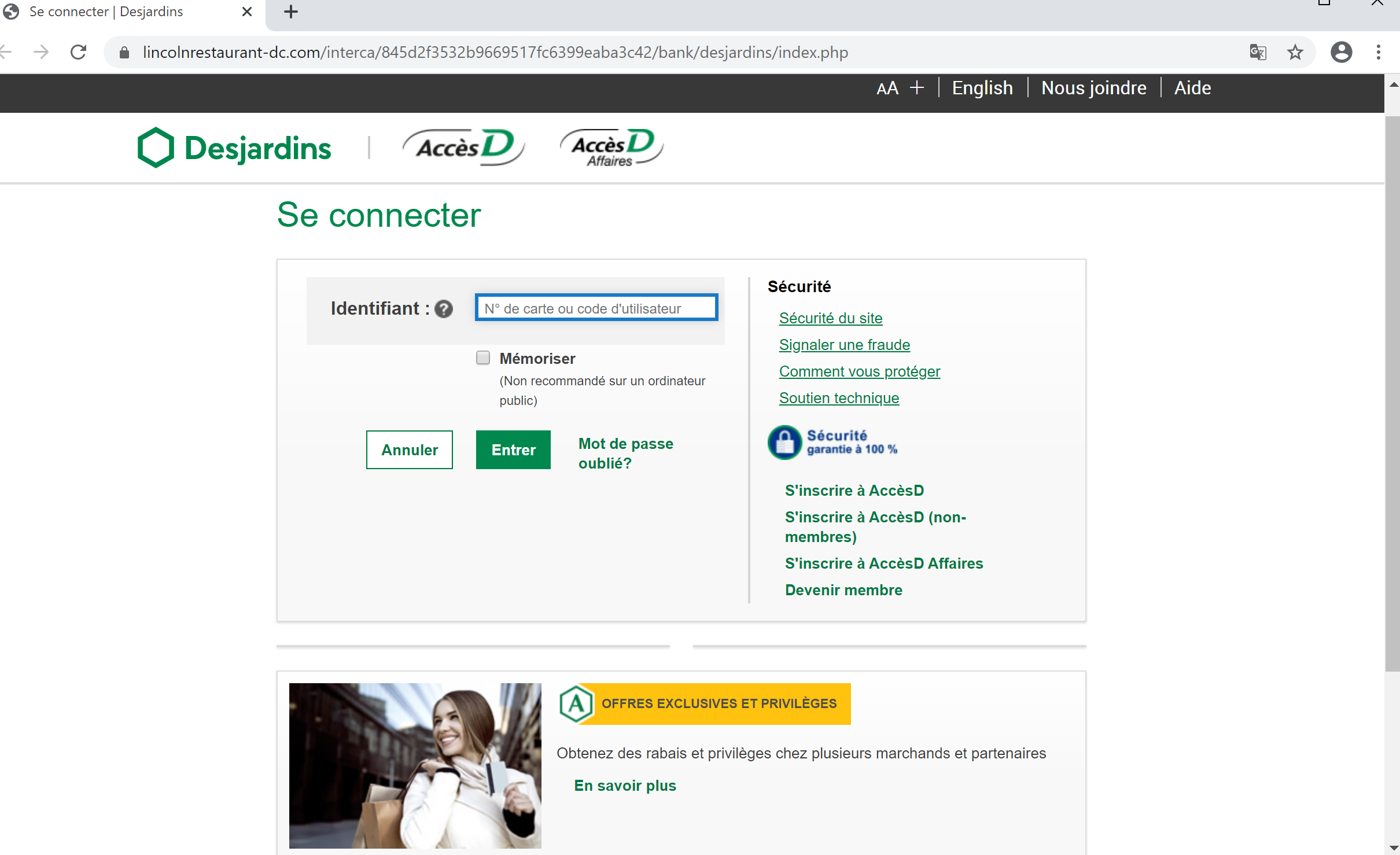
Figure 12 – CIBC
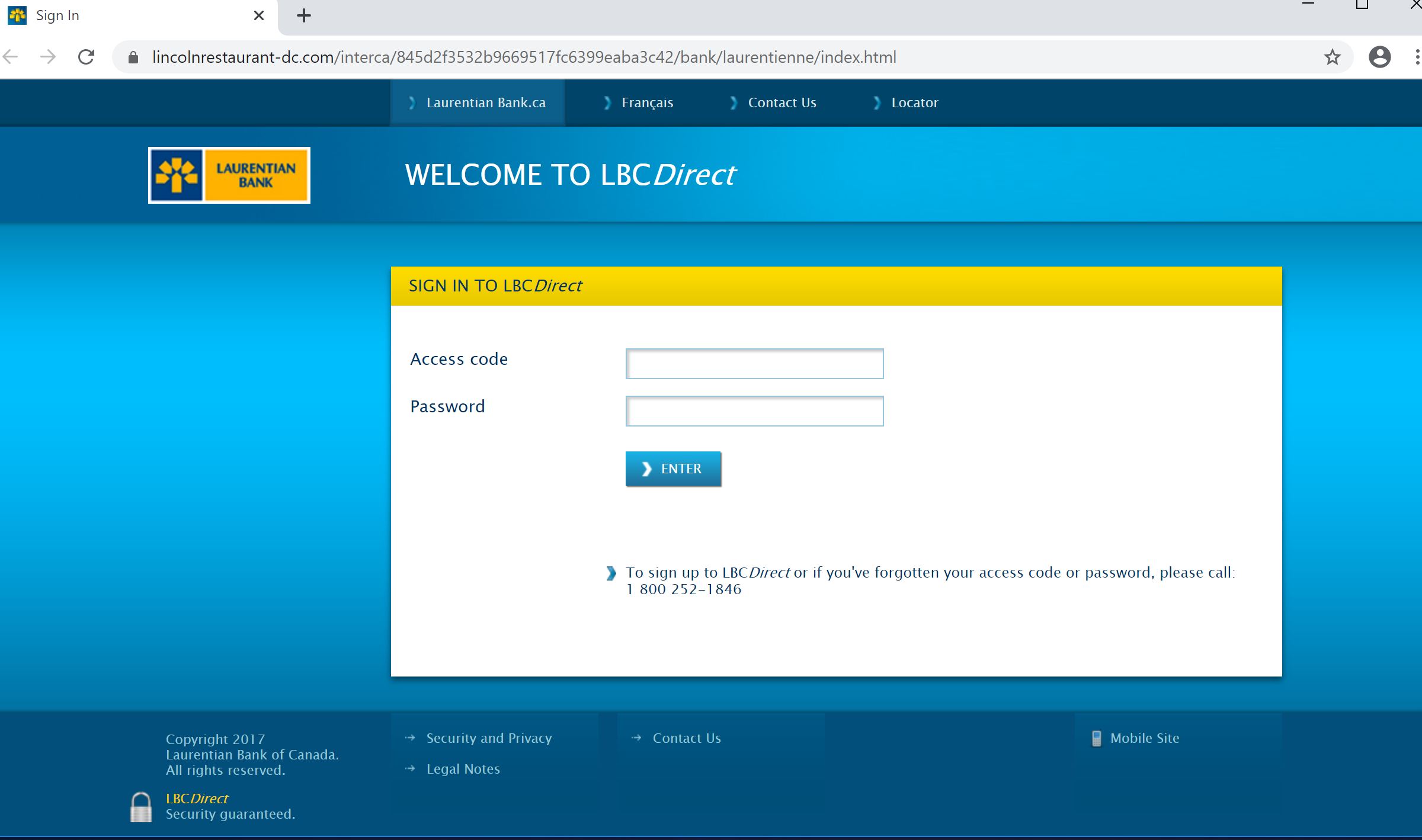
Figure 13 – Desjardins
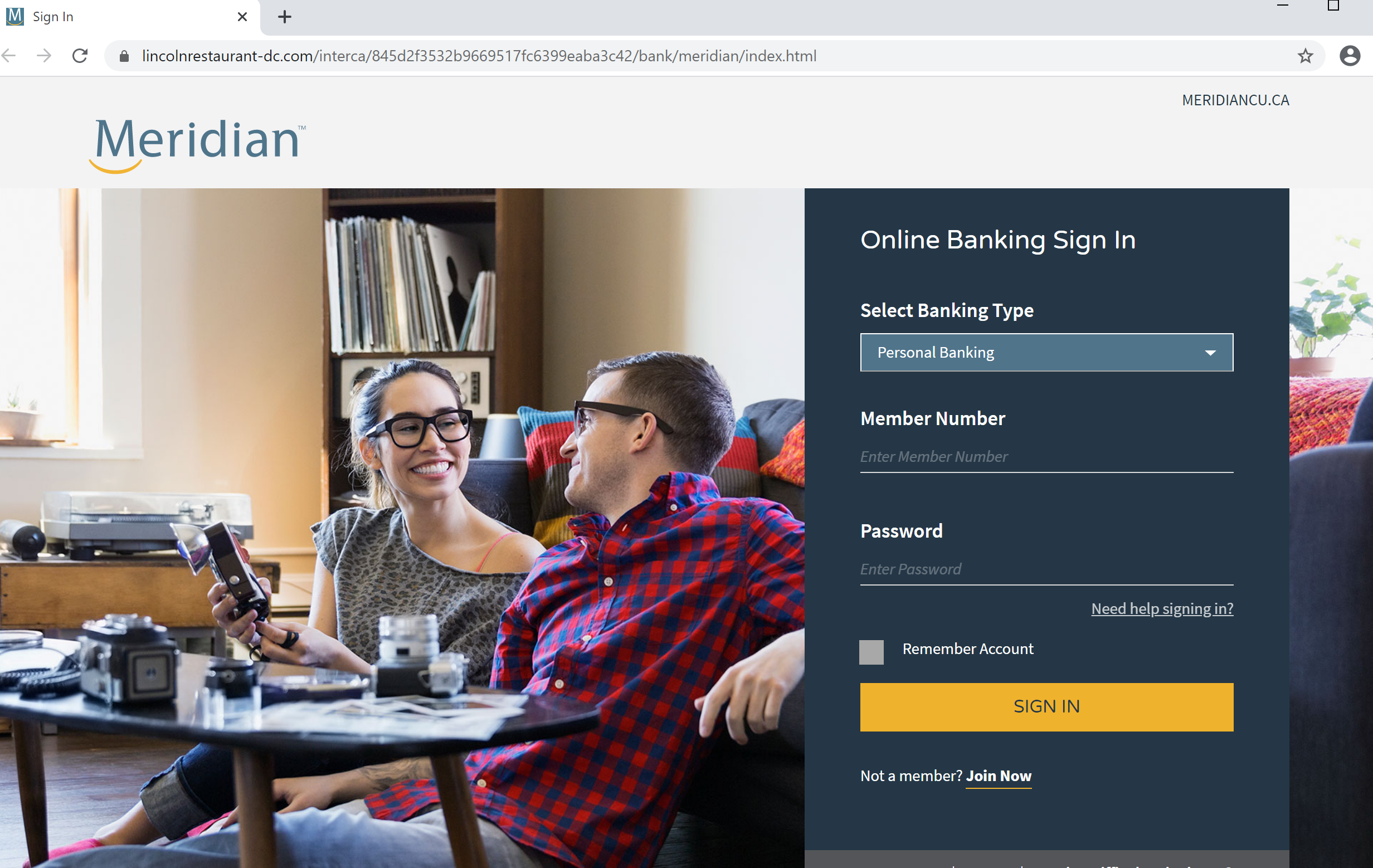
Figure 14 – Laurentian
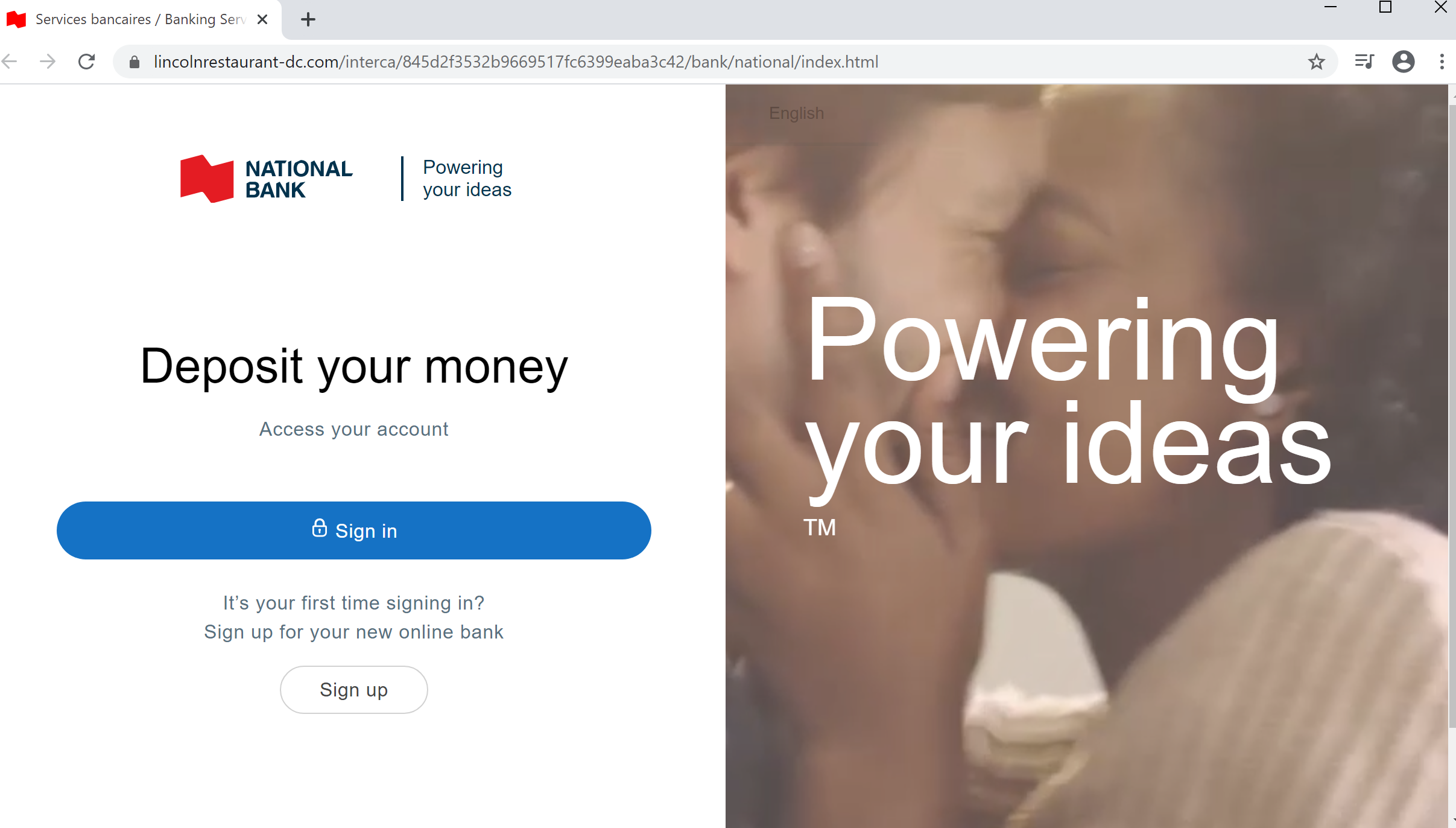
Figure 15 – Meridian
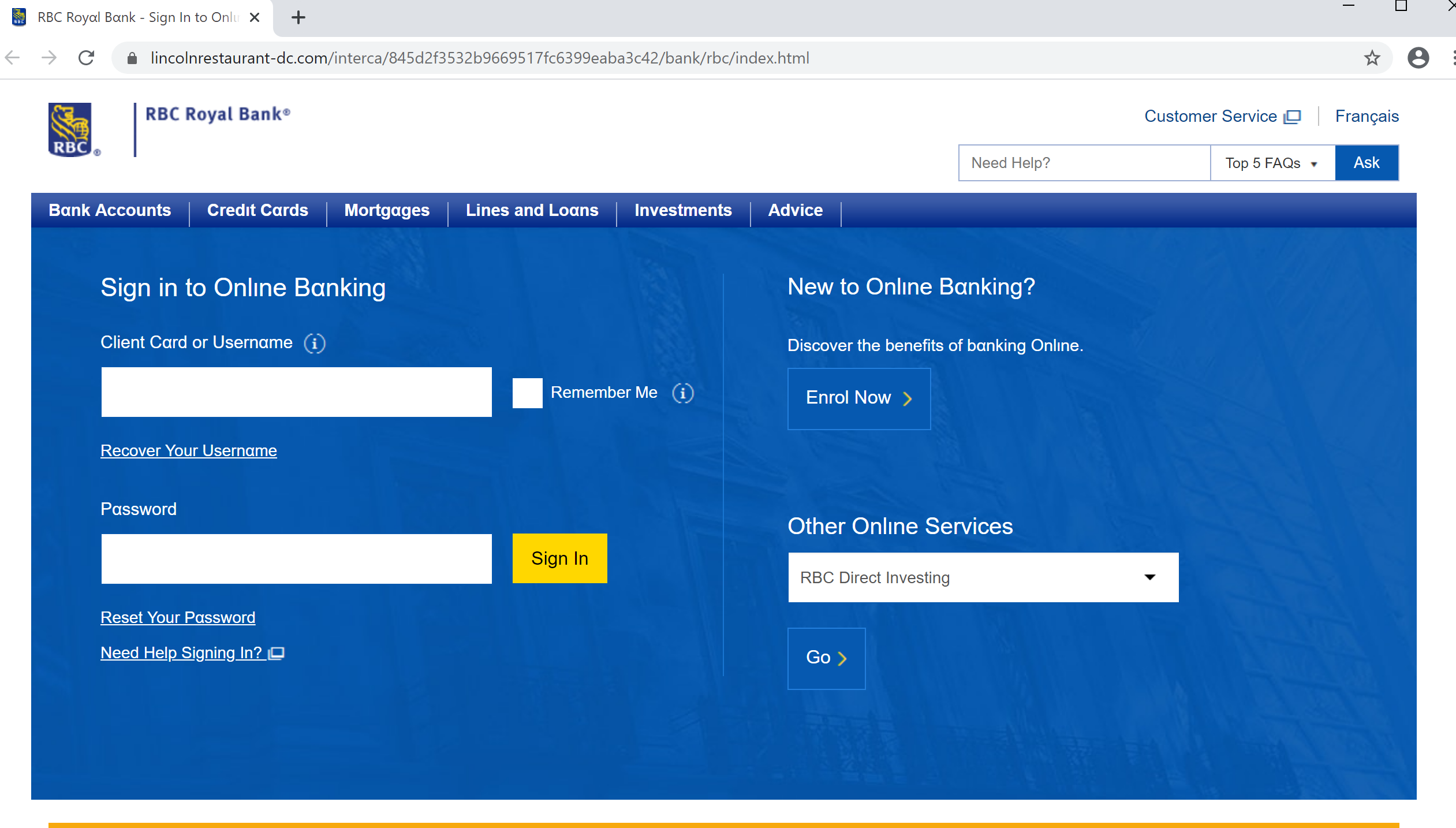
Figure 16 – National Bank
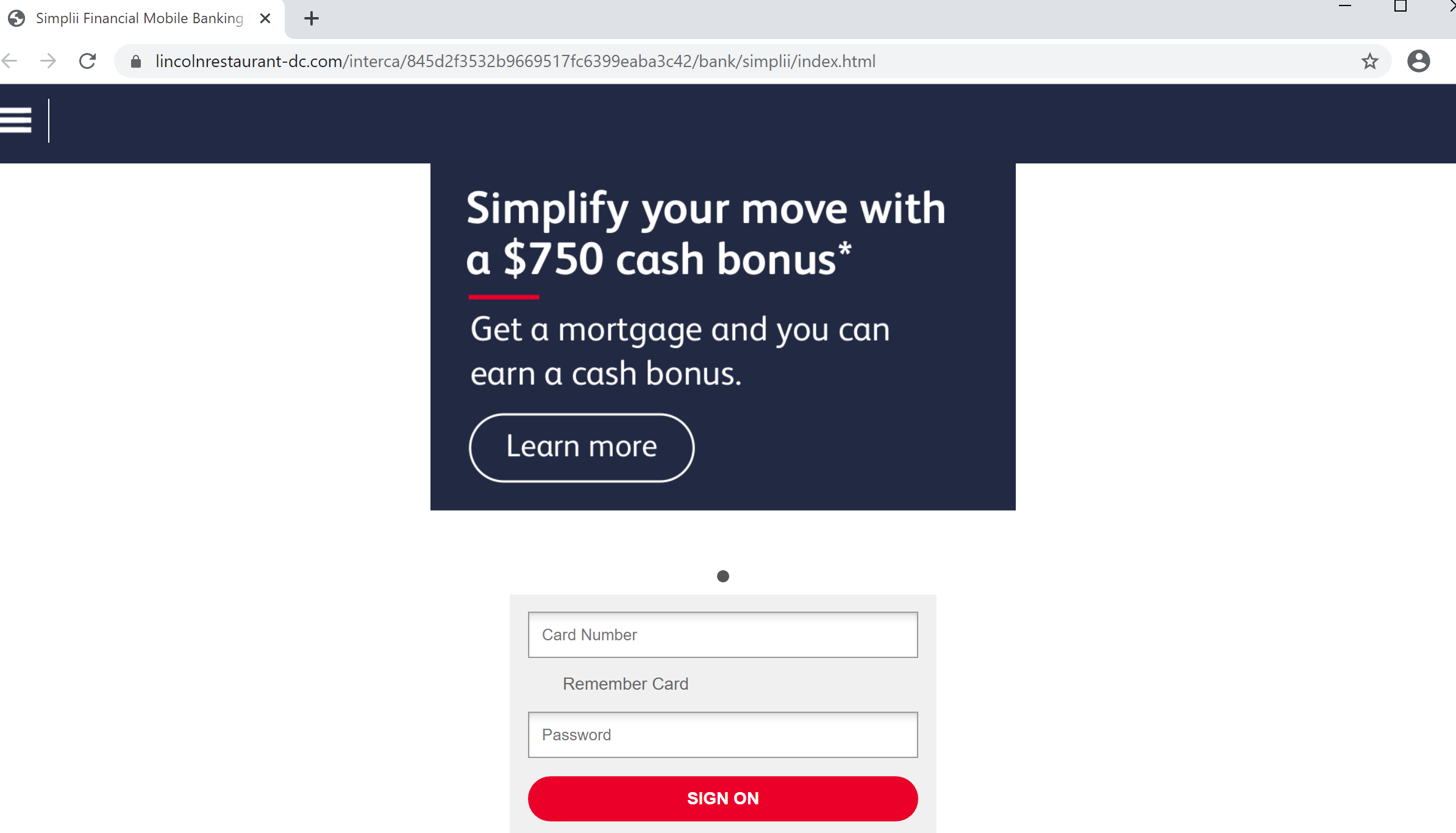
Figure 17 – RBC
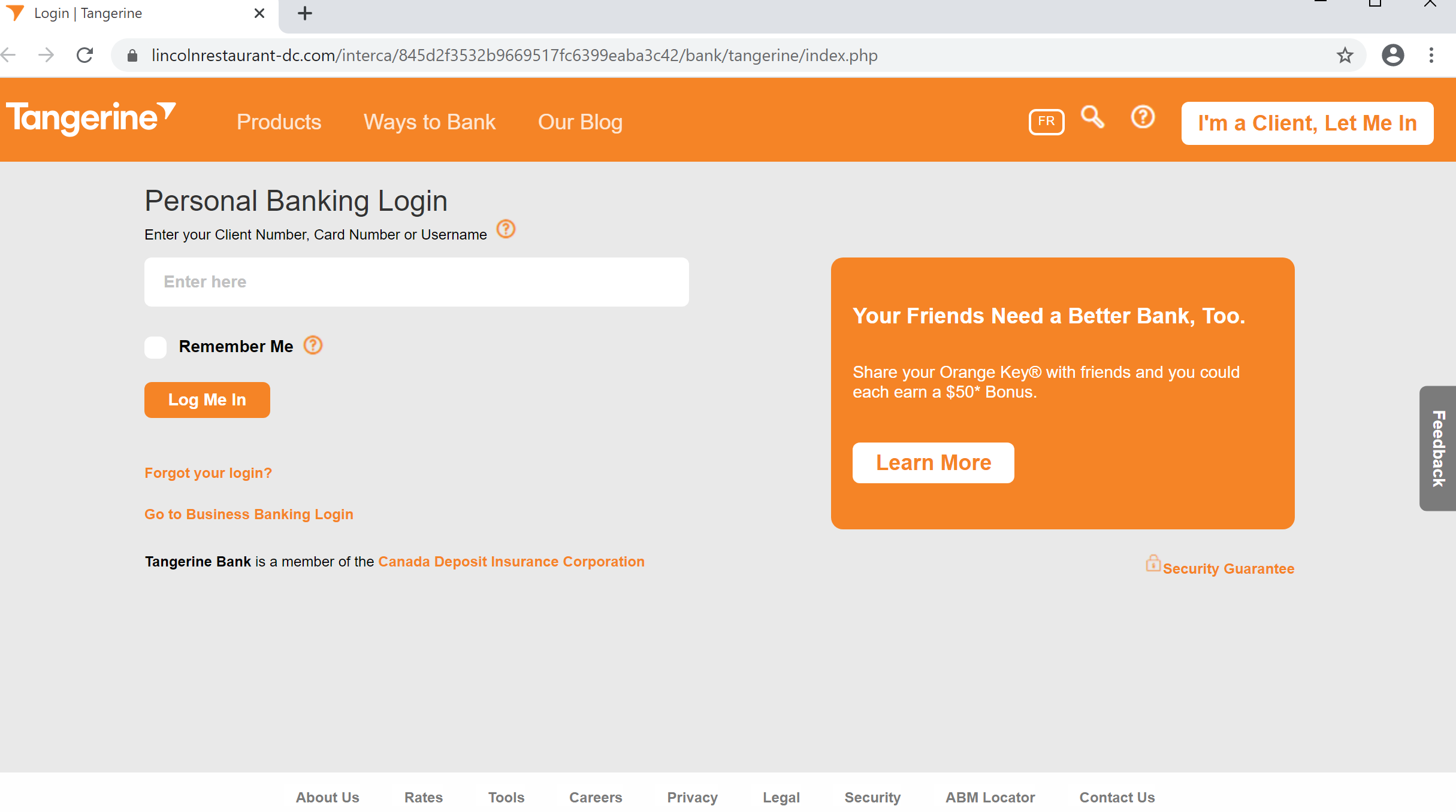
Figure 18 – Simplii
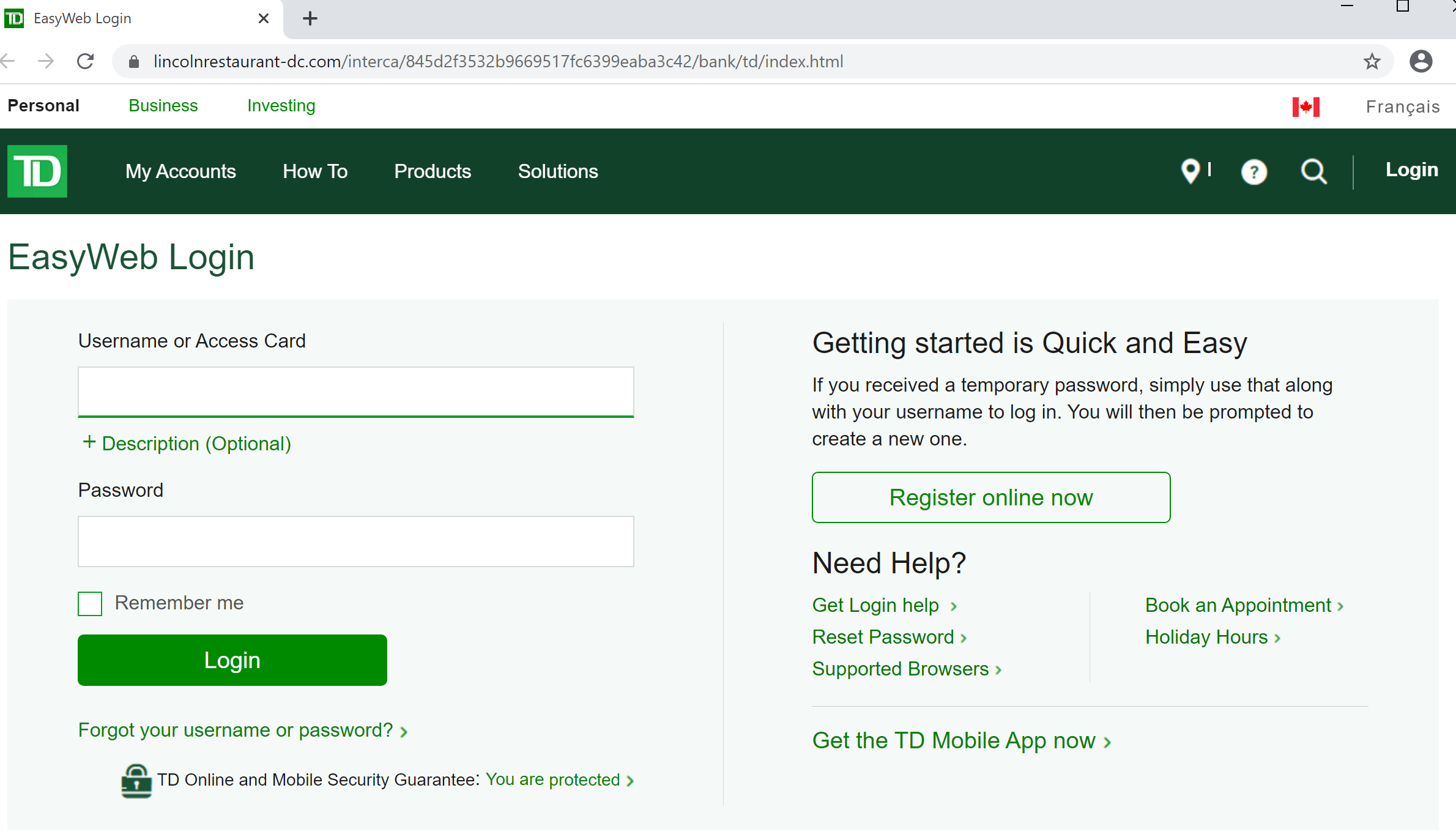
Figure 19 – Tangerine
Indicators of Compromise
Malicious URL:
Figure 20 – TD
Associated IP:
hxxps://lincolnrestaurant-dc[.]com/interca
All third-party trademarks referenced by Cofense whether in logo form, name form or product form, or otherwise, remain the property of their respective holders, and use of these trademarks in no way indicates any relationship between Cofense and the holders of the trademarks. Any observations contained in this blog regarding circumvention of end point protections are based on observations at a point in time based on a specific set of system configurations. Subsequent updates or different configurations may be effective at stopping these or similar threats.
The Cofense® and PhishMe® names and logos, as well as any other Cofense product or service names or logos displayed on this blog are registered trademarks or trademarks of Cofense Inc.
108[.]167[.]182[.]39
This post was first first published on Cofense’s website by Cofense. You can view it by clicking here

