What to Expect from the Next Generation of Secure Web Gateways
While secure web gateways (SWGs) have operated on a far more compressed timetable, a similarly drastic evolution has taken place. SWGs are still largely focused on ensuring users are protected from unsafe or non-compliant corners of the internet, but the transition to a cloud- and remote-working world has created new security challenges that the traditional SWG is no longer equipped to handle. It’s time for the next generation of SWGs that can empower users to thrive safely in an increasingly decentralized and dangerous world.
After more than a century of technological innovation since the first units rolled off Henry Ford’s assembly lines, automobiles and transportation bear little in common with the Model T era. This evolution will continue as society finds better ways to achieve the outcome of moving people from point A to point B.
URL filtering then transitioned to proxy servers sitting behind corporate firewalls. Since proxies terminate traffic coming from users and complete the connection to the desired websites, security experts quickly saw the potential to perform more thorough inspection than just comparing URLs to existing blacklists. By incorporating anti-virus and other security capabilities, the “secure web gateway” became a critical part of modern security architectures. However, the traditional SWG could only play this role if it was the chokepoint for all internet traffic, sitting at the edge of every corporate network perimeter and having remote users “hairpin” back through that network via VPN or MPLS links.
How We Got Here
The SWG actually started out as a URL filtering solution and enabled organizations to ensure that employees’ web browsing complied with corporate internet access policy.
This remarkable transformation also expands the requirements for data and threat protection, leaving security teams to grapple with a number of new sophisticated threats and compliance challenges. Unfortunately, traditional SWGs haven’t been able to keep pace with this evolving threat landscape.
Next-Generation SWG
The transition to a cloud and remote-working world has put new burdens on the traditional perimeter-based SWG. Users can now directly access IT infrastructure and connected resources from virtually any location from a variety of different devices, and many of those resources no longer reside within the network perimeter on corporate servers.
Another issue revolves the encrypted nature of the internet. The majority of web traffic and virtually all cloud applications use SSL or TLS to protect communications and data. Without the ability to decrypt, inspect and re-encrypt traffic in a compliant, privacy-preserving manner, a traditional SWG is simply not able to cope with today’s world.
Just about every major breach now involves sophisticated multi-level web components that can’t be stopped by a static engine. The traditional SWG approach has been to coordinate with other parts of the security infrastructure, including malware sandboxes. But as threats have become more advanced and complex, doing this has resulted in slowing down performance or letting threats get through. This is where Remote Browser Isolation (RBI) brings in a paradigm shift to advanced threat protection. When RBI is implemented as an integral component of SWG traffic inspection, and with the right technology like pixel mapping, it can deliver real-time, zero-day protection against ransomware, phishing attacks and other advanced malware while not hindering the browsing experience.
What we need from Next-Gen SWGs
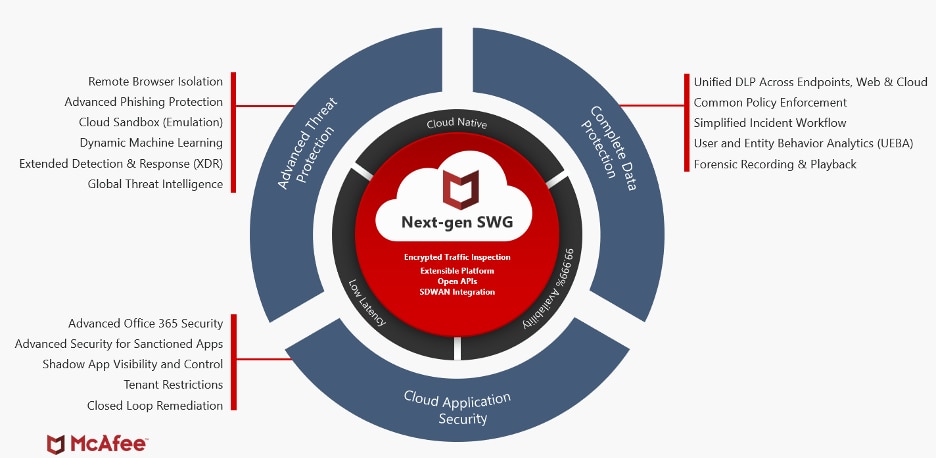
A next-gen SWG should help simplify the implementation of Secure Access Service Edge (SASE) architecture and help accelerate secure cloud adoption. At the same time, it needs to provide advanced threat protection, unified data control, and efficiently enable a remote and distributed workforce.
Finally, there is the question of cloud applications. While cloud applications operate on the same internet as traditional websites, they function in a fundamentally different way that traditional SWGs simply can’t understand. Cloud Access Security Brokers (CASBs) are designed to provide visibility and control over cloud applications, and if the SWG doesn’t have access to a comprehensive CASB application database and sophisticated CASB controls, it is effectively blind to the cloud.
Here are some of the use cases:
- Enable a remote work force with a direct-to-cloud architecture that delivers 99.999% availability – As countries and states slowly came out of the shelter-in-place orders, many organizations indicated that supporting a remote and distributed workforce will likely be the new norm. Keeping remote workers productive, data secured, and endpoints protected can be overwhelming at times. A next-gen SWG should provide organizations with the scalability and security to support today’s remote workforce and distributed digital ecosystem. A cloud-native architecture helps ensure availability, lower latency, and maintain user productivity from wherever your team is working. A true cloud-grade service should offer five nines (99.999%) availability consistently.
- Reduce administrative complexity and lower cost – Today, with increased cloud adoption, more than eighty percent of traffic is destined for the internet. Backhauling internet traffic to a traditional “Hub and Spoke” architecture which requires expensive MPLS links can be very costly. Network slows to a halt as traffics spikes, and VPN for remote workers have proven to be ineffective. A next-gen SWG should support the SASE framework and provide a direct-to-cloud architecture that lowers the total operating costs by reducing the need for MPLS links. With a SaaS delivery model, next-gen SWG’s remove the need to deploy and maintain hardware infrastructure reducing hardware and operating costs. Per Gartner’s SASE report, organizations can “reduce complexity now on the network security side by moving to ideally one vendor for secure web gateway (SWG), cloud access security broker (CASB)…” By unifying CASB and SWG, organizations can benefit from unified policy and incident management, shared insights on business risk and threat database, and reduced administrative complexity.
- Defend against known and unknown threats – As the web continues to grow and evolve, web-borne malware attacks grow and evolve as well. Ransomware, Phishing and other advanced web-based threats are putting users and endpoints at risk. A next-gen SWG should provide real-time Zero-day malware and advanced phishing protection via a layered approach that integrates dynamic threat intelligence for URL, IPs and file-hashes and real-time protection against unknown threats with machine-learning and emulation-based sandboxing. A next-gen SWG should also include integrated Remote Browser Isolation to prevent unknown threats from ever reaching the endpoints. Furthermore, a next-gen SWG should provide the capability to decrypt, inspect and re-encrypt SSL/TLS traffic so threats and sensitive data cannot hide in encrypted traffic. Lastly, a next-gen SWG should be XDR-integrated to improve SOC efficiencies. SOC teams have too much to deal with already and they shouldn’t settle for Siloed security tools.
- Lock down your data, not your business – More than 95% of companies today use cloud services, yet only 36% of companies can enforce data loss prevention (DLP) rules in the cloud at all. A next-gen SWG should offer a more effective way to enforce protection with built-in Data Loss Prevention templates and in-line data protection workflows to help organizations comply with regulations. A device-to-cloud data protection offers comprehensive data visibility and consistent controls across endpoints, users, clouds, and networks. When incidents do happen, administrators should be able to manage investigations, workflows, and reporting from a single console. Next-gen SWGs should also integrate user and entity behavior analytics (UEBA) to further protect business sensitive data by detecting and separating normal users from the malicious or compromised ones.
SWGs have clearly come a long way from just being URL filtering devices to the point where they are essential to furthering the safe and accelerated adoption of the cloud. But we need to push the proverbial envelope a lot further. Digital transformation demands nothing less.
This post was first first published on Enterprise – McAfee Blogs’s website by Sadik Al-Abdulla. You can view it by clicking here



