Cloud app security in a direct-to-cloud world

An increasing number of organizations are embarking on the ‘direct-to-cloud’ journey. This provides a number of benefits from a performance, operations and cost standpoint due to the efficiencies achieved by remote and branch locations routing traffic differently.
There are a few more things to think about when considering direct-to-cloud connectivity: How it impacts cloud application usage and organizational security.
Impact of direct-to-cloud on business applications
Traditional environments have on-premises infrastructures to support most of the business applications. When we migrate from a central hub infrastructure, does that mean there will be increased dependency on cloud applications?
Most probably, yes!
Larger percentage of new business services will be cloud hosted to gain the benefits that come along with it like mobile workforce that’s more productive and competitive while on-the-go, reduced cost of operations, scalability, business continuity, etc. Over time, even on-prem solutions will most likely have a migration path to the cloud.
What are the considerations for security in this new environment?
One of the main things we hear from our discussions with organizations migrating business services to the cloud is around visibility. Traditionally, security teams had full visibility to the environment when services were hosted on-prem. Now they wonder about things like:
- Who is accessing the cloud service?
- When are they accessing it?
- Where are they accessing it from?
- How are they accessing it?
- What information are they accessing?
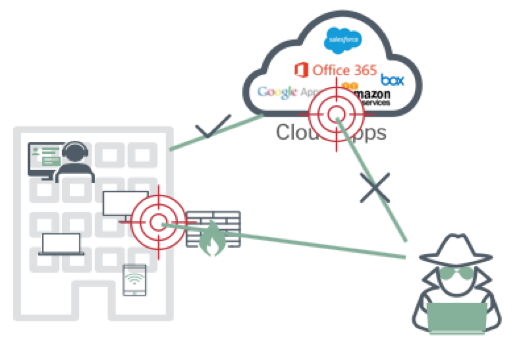
Cloud becomes the new attack surface
With a shared security responsibility model, the cloud becomes another attack surface in addition to the on-prem corporate environment. Consider this scenario: An employee using a personal device (BYOD) to access a sanctioned cloud service like Office365, will have access to the business information. However, the IT/IS team never sees that traffic hit the corporate infrastructure.
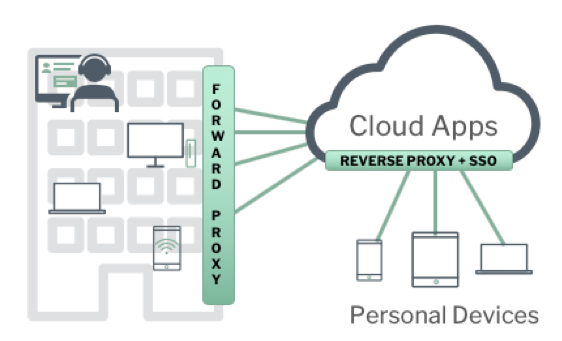
Accessing cloud apps using personal devices (BYOD)
In a cloud environment, we also need to think about compliance, which can be streamlined to keep the auditors happy. Some things to think about:
- How do on-prem policies extend to the cloud?
- Do you need a central console for compliance policy management?
- Do you have the visibility to achieve compliance in the cloud?
To achieve this, we need to change the approach around security.
Thinking about security differently
Security in a cloud or hybrid environment doesn’t have to be complicated. It just requires us to think about it differently. We do not have to dismiss the good things we have in place around on-prem security. But we do need to add cloud visibility and control to the mix. Cloud Access Security Broker (CASB) can provide the visibility and control for cloud applications that organizations are looking for. In fact, Gartner listed CASB as one of the ‘Top 10 Security Projects for 2019’. Adding cloud protection or CASB to an existing on-prem environment doesn’t need to be done in a silo. On the contrary, it becomes more effective if done in an integrated manner. This can be done in multiple ways. If you have web security already in place, you can augment it with cloud application security as an add-on. For example, Forcepoint Web Security comes with the ability to add cloud app control module to provide visibility and control over cloud applications in an integrated manner. If your organization is focused on data protection with a solution like DLP even that can be extended to the cloud to have unified policy management. No matter where you come from adding cloud security to it should be straightforward. Regardless of where you are in the ‘direct-to-cloud” journey, the advantages of embracing a cloud/hybrid environment will transform your business. It will bring greater productivity, lower cost due to infrastructure and operational efficiencies, reduce risk with frictionless security and also streamline compliance.
Please follow the links to learn about Forcepoint Web Security, CASB and more. You can also find more information on direct-to-cloud evolution from a network perspective in a recent blog by my colleague Jim Fulton here.
View the on-demand webcast on this topic here.

