Accelerating digital transformation with Secure SD-WAN

Digital Transformation has risen to the top of many enterprises’ and government agencies’ IT agendas. While it is frequently being used as a rationale for almost any initiative, most Digital Transformation efforts usually begin with using cloud applications and internet technologies to make people more productive and reduce costs. Retailers, banks, hotels, large school systems and public-facing government agencies with many locations are embracing new “direct-to-cloud” ways to connect and protect people in stores, branch offices, and remote offices around the world.
Why is “Direct-to-Cloud” Suddenly a Thing?
Cloud apps and (relatively) fast internet links have been around for two decades, so why has going “direct-to-cloud” suddenly become such a big thing? The short answer is that traditional “hub-and-spoke” networks used by distributed organizations can no longer keep up as modern cloud apps become interactive.
Microsoft Office 365 is the most widespread example. Organizations are adopting it at astounding rates, but often experience dramatically slower user performance at remote sites than in their central offices. This can happen whenever remote stores, branches or offices aren’t connecting to the internet directly. Instead, they’re going over internal networks that send traffic back to centralized gateways. These “backhauled” internal networks, often built on slow, expensive technologies such as MPLS, introduce delays that kill the performance of the modern cloud apps that organizations are looking to adopt.
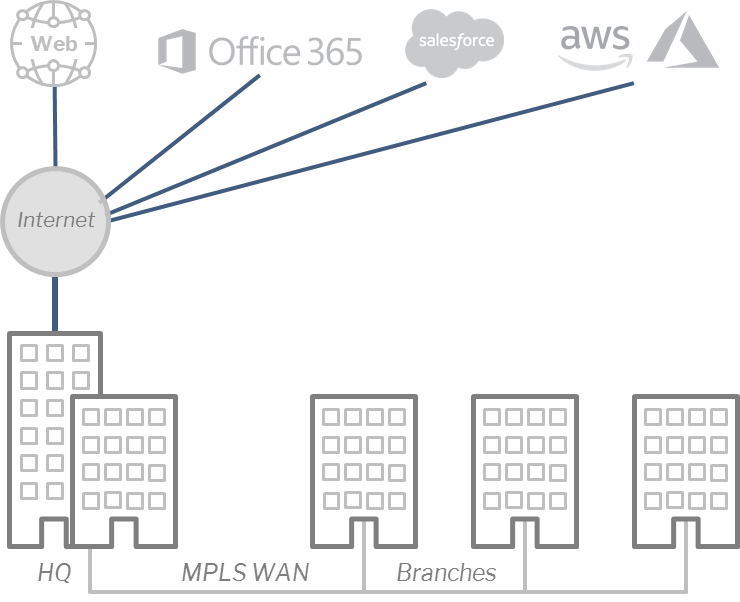
Traditional Networks “Backhaul” Traffic Through Central Hubs
Step 1. SD-WAN Boosts Performance and Reduces Infrastructure Costs
To eliminate the delays of traditional backhauled network architectures, enterprises and government agencies are connecting their remote sites directly to the internet using low-cost broadband links like DSL, cable, fiber or even mobile LTE. These links are managed through Software-Defined Wide-Area Networking (SD-WAN), a new class of networking technologies that automatically route each application’s traffic over the right network links. This gives operations teams new levels of visibility and control over their networks.
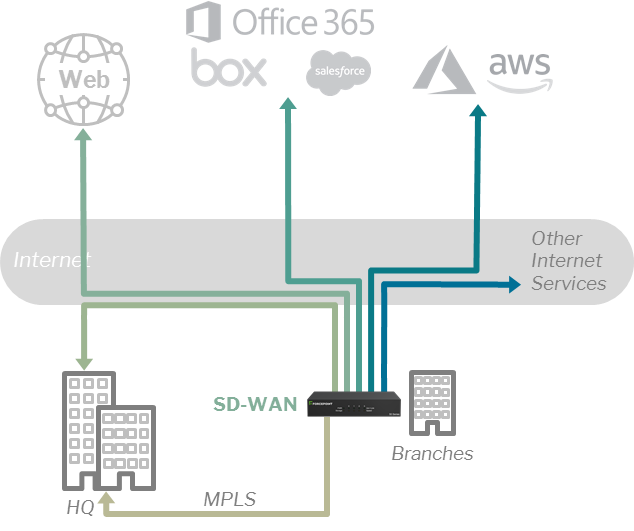
SD-WAN Sends Each Applications’ Traffic Over the Right Network Link
For example, it’s not unusual to see retailers run separate connections into each large store for different types of applications:
- Fast, low-latency links (fiber, cable, etc.) – for cloud-based business apps like Office 365, CRM, ERP, streaming video for promotions or training, etc.
- Less expensive links (DSL, etc.) – for customer internet access over Wi-Fi
- Wireless links (LTE) – as a backup in case one of the other links goes down
- Internal legacy links (MPLS) – for sensitive point-of-sale data and legacy apps
SD-WAN makes it possible to automatically direct each application over different links to optimize performance and cost. For example, expensive fiber links can be reserved for business traffic (rather than cat videos) in a way that also addresses auditors’ requirements for segmentation and rapid response to potential problems.
Step 2. Security is Necessary to Complete SD-WAN
SD-WAN solutions almost always can encrypt traffic as it travels over the internet. But that’s privacy, not security. SD-WAN is great for handling new applications, but it breaks old, centralized security architectures that are based on having all network traffic flow back through headquarters-based security gateways. The security that used to be provided by those gateways now has to follow the network traffic and move closer to sites and users:
- Network Security – next-generation firewalls (NGFW) enforce enterprise access policies and prevent intrusions by internet-based attackers; they are usually deployed as remotely managed appliances but true NGFW-as-a-service offerings that are more than just basic firewalls are starting to come to market.
- Web Security – real-time network scanning protects users against advanced threats that lurk in web pages and downloaded content while also providing insight into the “Shadow IT” risks associated with web apps accessed by users; this is most commonly delivered as a cloud service complemented by hybrid enforcement at sites that have special data sovereignty requirements.
- Cloud App Security – cloud application security brokers (CASB) monitor organizations’ cloud-based business apps to prevent abuse and enforce data protection policies for information stored in those applications.
Bringing the Pieces together: Secure SD-WAN
Forcepoint is the only company in the industry to bring all of these pieces together into a single solution, from a single vendor. With Forcepoint Secure SD-WAN, organizations can seamlessly—and safely—connect and protect their networks, users and data to accelerate their digital transformation.
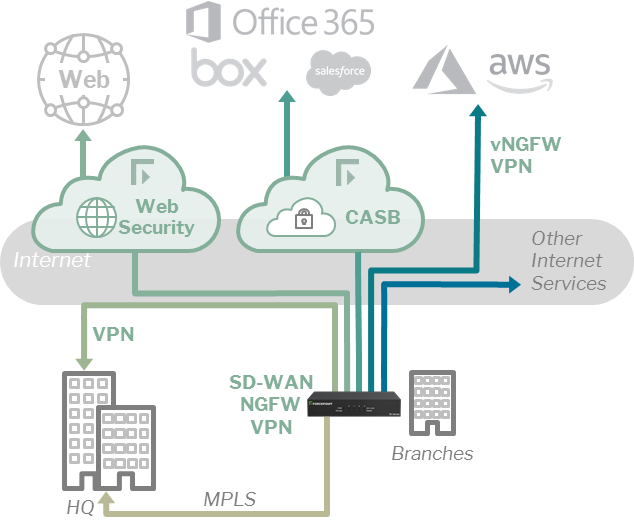
Secure SD-WAN Integrates Connectivity into Security
Forcepoint’s approach is different. We integrate excellent SD-WAN networking performance with the strongest NGFW network security, enabling 2000 sites to be managed from a single pane of glass. In fact, we pioneered the centralized management of multiple network connections (internet links as well as MPLS lines) combined with strong security.
Making Secure SD-WAN with Web Security Even Easier and More Affordable
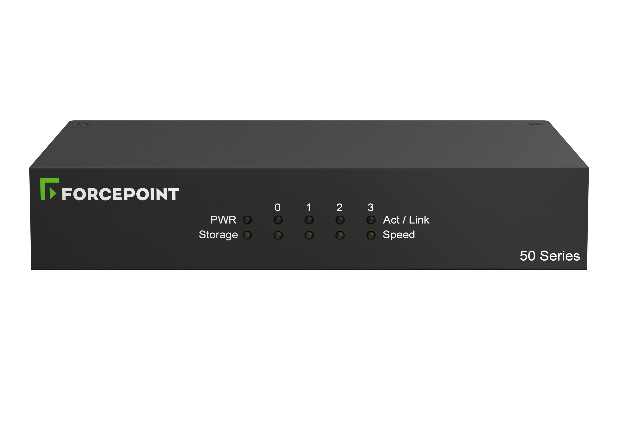
We’ve just taken our Secure SD-WAN to the next level with the release of two new parts of our solution. Our latest network security appliance, the Forcepoint NGFW 51 is our most compact, all-in-one SD-WAN, firewall, IPS, and VPN device ever. It delivers the full power of Forcepoint’s rack-mounted appliances, including our mixed-model advanced clustering, in a package that’s less than 5.5 inches (180mm) wide and only 1.5 inches (37mm) high—ideal for stores, branches and remote offices.
It comes with the latest version of our NGFW operating software, version 6.6, that integrates our SD-WAN even more efficiently with our Forcepoint Web Security Cloud so that sites can automatically protect users against web-based threats. This version also includes a new web-based interface to our renowned Security Management Center (SMC) console, making it easier than ever for operations teams to manage their connectivity and security from a single pane of glass.

