Mirai Rebirth Highlights Importance of Defending IoT

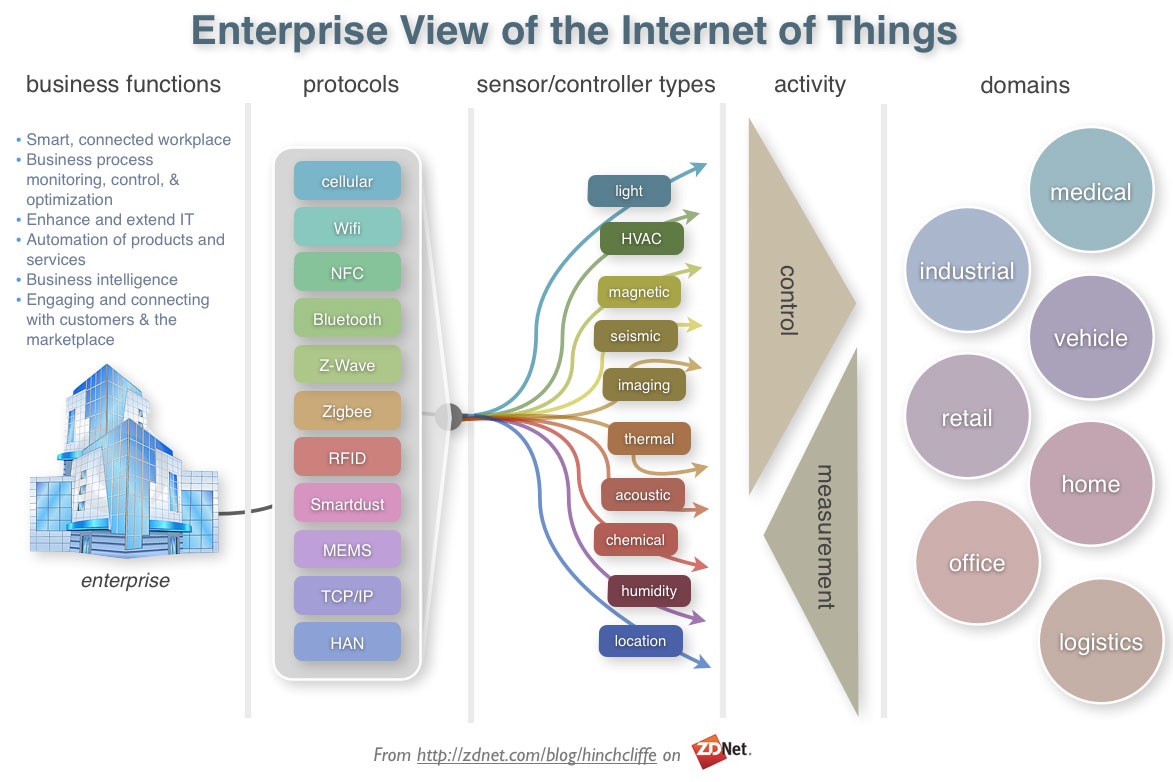
Enterprises of all sizes face a massive challenge when it comes to IoT security.
With so many business operations reliant on technology, there can be vulnerabilities hiding in a multitude of places. Security teams, especially those who work in or with DevOps teams, need to be able to locate those issues before cyber criminals are able to exploit them.
One of the most common forms of cyberattack is a denial-of-service (DoS), where hackers seek to take down a company or website by overloading its network and servers with unexpected traffic. The methods of DoS attacks have evolved over time, with the Mirai Botnet being one of the most dangerous forms in recent history.
In this blog, we’ll cover the history of the Mirai Botnet and what it means for modern day enterprises, especially those that rely on smart devices in the workplace.
Background on the Mirai Botnet
The Mirai Botnet was first discovered by a team of researchers in 2016. Its true origins are unknown and same for the person or group who created it. At the most basic level, the Mirai Botnet acts as a piece of malware that can be installed on any computer or device running the Linux open-source operating system.
Malware like the Mirai Botnet is intended infiltrate the operating system and perform nefarious actions without user or administrator consent. The biggest risk with the Mirai Botnet is its ability to spread across a local network, which means that if one device within your company becomes infected, then every other piece of hardware is in danger.
A device that runs the Mirai Botnet is capable of scanning its local network and looking for other machines that could be vulnerable. It is even smart enough to remotely remove other forms of malware that could be in conflict with its intentions.
Once the hacker behind the exploit has gathered the desired hardware resources, they can use the Mirai Botnet to execute a DoS attack. This becomes what is known as a distributed DoS because of how the traffic is sent from multiple streams. Enterprise IT solutions have become adept at blocking single-stream DoS attacks, but it is much harder to stop one being spread by a botnet.
The New Exploit on the IoT
When people discuss the Internet of Things (IoT), the conversation is usually based around consumer devices that offer new conveniences within the home. For example, you may choose to purchase a smart speaker that can respond to voice commands or a smart light bulb that can be turned on or off from your smartphone.
However, the IoT movement is much more widespread and has made a significant impact on the corporate space. Many companies have come to rely on smart appliances and hardware that can optimize and automate their workspaces. Internet-based security cameras and thermostats are quite popular in modern offices.
What many company leaders fail to recognize is that every new smart device that you add to your corporate network becomes a new risk and potential point of vulnerability. In fact, IoT devices often care more danger than a typical computer because of their simple software and lack of a user interface.
The Mirai Botnet has evolved to take advantage of the vulnerabilities in smart devices. Its codebase actually includes a lookup table to identify the manufacturer and model for different IoT hardware. As it scans the web for certain internet protocol (IP) addresses, it checks to see whether the device at the other end is running a basic version of Linux.
Once the Mirai Botnet has identified a potential target for installation, it checks its code for usernames and passwords that are commonly used by manufactures on IoT devices. If one of those sets of credentials is successful, then the hacker essentially gains full control over the device.
The code behind the Mirai Botnet has been shared online through open-source communities and that is part of the reason why its danger has increased in recent years. Hackers have the ability to tweak the malware so that it meets certain needs and becomes harder to detect and defend against.
How to Defend at the Enterprise Level
Because of malware like the Mirai Botnet, companies across the globe are dealing with a tricky cyber-based threat. First, they need to be concerned that a compromised device within their enterprise could result in other hackers gaining access to their network.
Second, there is a good chance that devices infected with the Mirai Botnet will suck up large amounts of bandwidth, which slows down network communications and potentially raises internal costs. Lastly, companies need to watch out for when the Mirai Botnet transitions into a full-blown DoS attack.
The best strategy for any enterprise is to be as proactive as possible when it comes to IT security. Resources should be invested into threat hunting to help uncover areas of weakness before a hacker can exploit them. Also, incident response tools that use artificial intelligence will flag potential threats without a human even needing to take action.
At an even more foundational level, any CEO who doesn’t require company network users to protect against data theft and other hacker schemes by only connecting to the internet through the encrypted protection of a VPN (now used by 26% of people who go online as of 2018) is asking for trouble.
If it’s too late and the Mirai Botnet has already infected IoT devices on your corporate network, the first step to take is turning off the compromised hardware. This will temporarily stop the botnet from spreading. You need to change the administrator password on each device very quickly or else the malware will reinstall itself after each reboot.
The Bottom Line
As the IoT movement grows and more smart devices make their way into corporate workspaces, IT security teams face a daunting task. They need to continue to safeguard all of the servers, networks, and data collections in their enterprise while also shifting part of their focus to smart devices. Threats like the Mirai Botnet are too dangerous to ignore.
The post Mirai Rebirth Highlights Importance of Defending IoT appeared first on Carbon Black.
Sam Bocetta, a guest author on the Carbon Black blog, is a freelance journalist specializing in U.S. diplomacy and national security, with emphases on technology trends in cyber warfare, cyber defense, and cryptography.