Centrify: Zero Trust Lessons from a Holiday Classic

Every year when the holidays roll around, I’m amazed at the way shopping deals dominate the headlines. Black Friday and Cyber Monday are annual juggernauts that produce some amazing opportunities for shoppers and retailers alike.
Yet this year, even the mighty shopping season has taken back-seat to the continuing domination of security breaches in the press. With $114 billion being spent on Information Security products and services in 2018, as estimated by Gartner, we should see the frequency of data breaches going down.
Instead, rather than seeing fewer headlines, we’re seeing more. In the past two weeks alone we’ve seen reported breaches or breach attempts by/at Dell, Dunkin Donuts, the National Republican Congressional Committee, Quora, and the Marriott/Starwood mega-breach affecting 500 million customers.
This much is clear: it’s time for most CISOs to rethink their security strategies. There’s no better time than the holidays to take some time to assess your company’s risk factors and put a plan in place to strengthen its security posture for 2019. A good place to start is with Zero Trust Privilege.
ZERO TRUST LESSONS FROM AN 8-YEAR-OLD
One of my favorite things about the holidays are the classic movies that show up on endless repeat throughout the season.
Recently, I got sucked into one of my holiday favorites: Home Alone.
As I watched little Kevin McCallister, played by Macaulay Culkin, develop ingenious and hilarious ways to keep out the bad guys, I was struck with the realization that he’s an incredible example of someone who takes a Zero Trust approach. To the extreme.
Let’s take a look at how Kevin takes measures to protect himself and his family’s possessions.
TRUST NO ONE
Like any good 8-year-old who has been taught the “Stranger, Danger” mindset, Kevin doesn’t trust anyone. That includes Joe Pesci and Daniel Stern (the robbers, Harry and Marv), his older brother Buzz, the scary old man down the street, and even the poor pizza delivery guy.
DEVELOP A PLAN
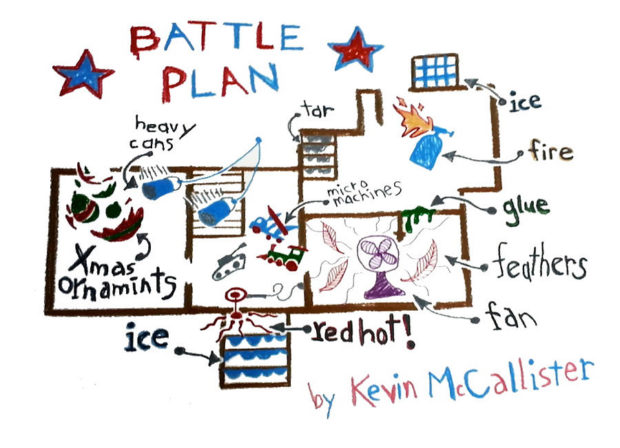
My favorite part about the battle plan Kevin draws up is that it assumes that, despite the creative ways he comes up with to keep them out, the bad guys are inevitably going to get in.
He’s got ice on the front and back steps, tar on the basement steps (complete with a nail), a red-hot front door handle, and who knows what else protecting his perimeter, along with the usual locks on his doors and windows.
But what’s most impressive is all of the measures Kevin has put in place INSIDE his house, because he’s assuming the bad guys are eventually going to make their way in and start looking around for valuables.
He’s got the following preventive tactics:
-
- Broken Christmas ornaments inside a window (for bare-footed burglars who lost their shoes to the tar outside)
- A tripwire
- A falling, scalding iron
- A homemade blowtorch to roast anyone who sticks his head in a window
- Glue, a fan, and feathers to slow them down
- Micro Machines in the entryway for a comical and painful double-slip
- Buzz’s tarantula!
- Swinging paint cans from the balcony upstairs (my personal favorite)
Any one of these would go a long way to deterring any bad guys once they’re inside. In the movie, however, Marv and Harry take all of this and just keep on coming.
HOME ALONE AND ZERO TRUST PRIVILEGE
As I watched the movie, I thought about the pillars of Zero Trust Privilege and how Kevin’s mindset correlates. I realized that you can draw two examples that show how Zero Trust can reduce risk, whether it’s warranted (in the case of the burglars) or not necessary (in the case of the pizza guy).
Verify who is requesting access
While the poor pizza guy doesn’t necessarily request access, there is expectation for Kevin to open the door. Instead, Kevin directs him to the back door, where he can identify him without being seen himself.
In the case of Harry and Marv, Kevin is already suspicious of them, but once he overhears their plans to break into his house that night, he knows they’re the burglars who’ve been victimizing the neighborhood and it’s up to him to stop them.
Contextualize the request
This one is pretty straightforward.
The pizza guy is confirmed to be who he is purporting to be. Kevin ordered a pizza, and he’s there to deliver it. Still, Kevin only gives him just enough access to get his payment and drop the pie on the doorstep.
For the burglars, the context is pretty clear. They want valuables from the McCallister house, and are willing to do whatever it takes to get them. Hence, the battle plan.
Ensure a clean access environment
Okay, so this one is a bit harder to draw a parallel to the movie. (What if the pizza box had a hidden camera? What if Harry and Marv had the flu? I’m reaching here, I know).
Still, it’s important to make sure access is only achieved through a clean source, so you don’t enable malware access to servers or introduce infections during connections to servers.
Grant least privilege
This is where Kevin excels.
He knows the pizza guy is coming, but still isn’t going to take any chances. He sends him to the back door, identifies him, pushes the payment and tip out of a mail slot, and requests the pizza be left on the doorstep. Just because he’s a known person operating with expected intent, he still doesn’t get any extra access privileges. Of course, that doesn’t stop Kevin from having some fun with him first.
For the burglars, malicious intent is clear, and every step is taken to grant absolutely zero privilege. Cue the paint can pendulum!
As things continue slowing down for the holidays, I hope you will all take some time to reflect on the year behind us and what you’re thankful for, and to also think about the year ahead. I hope it will be peaceful and insightful.
For you cybersecurity-minded folks, I also hope you’ll take some lessons in Zero Trust from Kevin McCallister. Remember, Zero Trust doesn’t require you to know someone has bad intentions, it just requires that you treat everyone with the same amount of trust: ZERO.
Wishing you and yours a very Happy Holiday season from all of us at Centrify, and here’s hoping for a secure and successful 2019.

